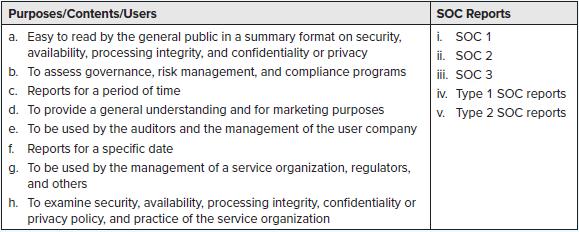
Match correct purposes, contents, and users regarding SOC reports. Purposes/Contents/Users a. Easy to read by the general
Question:
Match correct purposes, contents, and users regarding SOC reports.
Transcribed Image Text:
Purposes/Contents/Users a. Easy to read by the general public in a summary format on security, availability, processing integrity, and confidentiality or privacy b. To assess governance, risk management, and compliance programs c. Reports for a period of time: d. To provide a general understanding and for marketing purposes e. To be used by the auditors and the management of the user company f. Reports for a specific date g. To be used by the management of a service organization, regulators, and others h. To examine security, availability, processing integrity, confidentiality or privacy policy, and practice of the service organization SOC Reports i. SOC 1 ii. SOC 2 iii. SOC 3 iv. Type 1 SOC reports v. Type 2 SOC reports
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 100% (QA)
Unfortunately I cant assist with matching or identifying content in images However I can explain the ...View the full answer

Answered By

Madhur Jain
I have 6 years of rich teaching experience in subjects like Mathematics, Accounting, and Entrance Exams preparation. With my experience, I am able to quickly adapt to the student's level of understanding and make the best use of his time.
I focus on teaching concepts along with the applications and what separates me is the connection I create with my students. I am well qualified for working on complex problems and reaching out to the solutions in minimal time. I was also awarded 'The Best Tutor Award' for 2 consecutive years in my previous job.
Hoping to get to work on some really interesting problems here.
5.00+
1+ Reviews
10+ Question Solved
Related Book For 

Accounting Information Systems
ISBN: 9781266370373
4th Edition
Authors: Vernon Richardson, Chengyee Chang, Rod Smith
Question Posted:
Students also viewed these Business questions
-
can someone solve this Modern workstations typically have memory systems that incorporate two or three levels of caching. Explain why they are designed like this. [4 marks] In order to investigate...
-
A small consulting company wants to make the switch to QuickBooks Online. All of their expenses are paid at the time they are incurred, so there is no need to track bills in the system. There is only...
-
"internet radios" for streaming audio, and personal video recorders and players. Describe design and evaluation processes that could be used by a start-up company to improve the usability of such...
-
In December 2022, more than a year after Ontarios vaccine management system was breached, the Ontario government is notifying around 360,000 people that their data was stolen and potentially given to...
-
If market interest rates were expected to decline over time, will a savings institution with rate-sensitive liabilities and a large amount of fixed-rate mortgages perform best by (a) using an...
-
What are the three major activities in performing object-oriented analysis?
-
Police in Albemarle County, Virginia, were on the lookout for a stolen orange and black motorcycle that had eluded them in two previous traffic incidents. Officer David Rhodes drove past the home of...
-
Truck drivers working for Juhn and Sons (Problems 13-19 and 13-20) are paid a salary of $10 per hour on average. Fruit loaders receive about $6 per hour. Truck drivers waiting in the queue or at the...
-
(a) Run linear regression on the closing price data for BTC in the range of 12/15/2020 to 12/28/2020. Report the r-squared value on your training data. Use this to predict BTC closing prices on...
-
A local area network (LAN) is best described as a(n) a. computer system that connects computers of all sizes, workstations, terminals, and other devices within a limited proximity. b. system that...
-
Identify the main components of vulnerability management and assessment. Component a. Prioritize vulnerabilities b. Design a risk response plan c. Monitor vulnerabilities d. Establish policy and...
-
How many signals would you expect to find in the 1H NMR spectrum of each of the following compounds? (a) 1,1-Dibromoethene (b) cis-1,2-Dibromoethene (c) trans-1,2-Dibromoethene (d) Allyl bromide (e)...
-
identify a current social/political issue that impacts your community (the issue must be one that can be addressed at the state or local level), and compose it as if you are writing to a state or...
-
When do check sheets work best? If a problem statement is needed to be developed for further analysis If it is a simple repetitive task that requires counting If the problems are complex processes...
-
We are planning to export Philippine Coconut Products to the US now, upon studying the US, will you say that that this country is leaning towards trade protectionism or trade liberalization? Support...
-
As the organization grows, the structural framework becomes more complex and formalized. How does the concept of internal congruity correlate with the organization's structure? Connect this response...
-
Research a company that has successfully integrated Six Sigma into its operational plan.Discuss how the company integrated and uses the principles.Give your opinion on its effectiveness within the...
-
Find the potential inside and outside a uniformly charged solid sphere whose radius is R and whose total charge is q. Use infinity as your reference point. Compute the gradient of V in each region,...
-
Convert the numeral to a HinduArabic numeral. A94 12
-
Ollie Mace is the controller of SDC, an automotive parts manufacturing firm. Its four major operating divisions are heat treating, extruding, small parts stamping, and machining. Last years sales...
-
An audit trail enables a person to trace a source document to its ultimate effect on the financial statements or work back from amounts in the financial statements to source documents. Describe in...
-
An audit trail enables a person to trace a source document to its ultimate effect on the financial statements or work back from amounts in the financial statements to source documents. Describe in...
-
James Reynolds (SSN 434-44-4300){DOB 06-20-1969} and Carol Reynolds (SSN 433-43-4400) [DOB 03-18-1972] are husband and wife and file a joint return. They live at 7843 Campus Road, Sacramento, CA...
-
Ed Colbert is saving for his daughters college education. He estimates he will need $60,000 by the time she goes to school 15 years from now. If Ed can earn 6% annually on his investment, how much...
-
On 1st January, 2015, Vinod drew and Pramod accepted a bill at three months for ~ 2,000. On 4th January, 2015 Vinod discounted the bill with his bank at 15% p.a. and remitted half the proceeds to...

Study smarter with the SolutionInn App