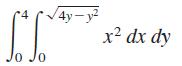
Evaluate the iterated integral by converting to polar coordinates. 10 Jo | 4y-y2 x dx dy
Question:
Evaluate the iterated integral by converting to polar coordinates.
Transcribed Image Text:
오 10 Jo | 4y-y2 x² dx dy
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 57% (7 reviews)
4yy x dx dy x2 4 sin 0 co...View the full answer

Answered By

JAPHETH KOGEI
Hi there. I'm here to assist you to score the highest marks on your assignments and homework. My areas of specialisation are:
Auditing, Financial Accounting, Macroeconomics, Monetary-economics, Business-administration, Advanced-accounting, Corporate Finance, Professional-accounting-ethics, Corporate governance, Financial-risk-analysis, Financial-budgeting, Corporate-social-responsibility, Statistics, Business management, logic, Critical thinking,
So, I look forward to helping you solve your academic problem.
I enjoy teaching and tutoring university and high school students. During my free time, I also read books on motivation, leadership, comedy, emotional intelligence, critical thinking, nature, human nature, innovation, persuasion, performance, negotiations, goals, power, time management, wealth, debates, sales, and finance. Additionally, I am a panellist on an FM radio program on Sunday mornings where we discuss current affairs.
I travel three times a year either to the USA, Europe and around Africa.
As a university student in the USA, I enjoyed interacting with people from different cultures and ethnic groups. Together with friends, we travelled widely in the USA and in Europe (UK, France, Denmark, Germany, Turkey, etc).
So, I look forward to tutoring you. I believe that it will be exciting to meet them.
3.00+
2+ Reviews
10+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Mathematics questions
-
Evaluate the iterated integral by converting to polar coordinates ! V16-x2 3xdydx -4 J-V16-x2
-
Q\ Evaluate the iterated integral by converting to polar coordinates -2 cV2x-x2 Vx2 + y? dy dx
-
why the iterated integral is written in the above form. I thought x=rcos, and y=rsin, so after simple substitution, shouldn't it be like: 2-(rcos/3)-(2rsin)/3? B2. Consider the solid below the plane...
-
2. Imagine a college basketball team has the following supply and demand figures for a typical game: Price 8 16 24 32 40 Quantity Demanded 28000 22000 16000 10000 4000 Quantity Supplied 16000 16000...
-
Sawada Insurance Ltd. issues bonds with a face value of $100 million that mature in 12 years. The bonds carry a 6% interest rate and are sold at 104.35 to yield 5.5%. They pay interest semi-annually....
-
A computer chip is essentially a series of micro-sized transistors that function as tiny switches to control the flow of electrons. Millions, sometimes billions, of transistors are packed into chips...
-
What information should the independent auditor consider when assessing the objectivity of the internal auditors?
-
An investor has two bonds in his portfolio that have a face value of $1,000 and pay a 10% annual coupon. Bond L matures in 15 years, while Bond S matures in 1 year. a. What will the value of each...
-
You have reformulated the Imber Aedax Company's most recent financial statements and extracted the following information: Year ended 31 December 2019 Sales Interest expense minus interest income...
-
Use a computer algebra system to find the mass and center of mass of the lamina bounded by the graphs of the equations for the given density. r = 2 cos 30, 6 TT 6' 0 - p = k
-
Write a double integral that represents the surface area of z = (x, y) over the region R. Use a computer algebra system to evaluate the double integral. (x, y) = 2/3x /2 + cos x R = {(x, y): 0 x ...
-
A person jumps from the roof of a house 3.9-m high. When he strikes the ground below, he bends his knees so that his torso decelerates over an approximate distance of 0.70m. If the mass of his torso...
-
An S-R flip flop is implemented with NOR gates. The flip-flop's transitions are trigger by a clock input signal on the rising edge, and can be reset with a synchronous active-low clear input. The...
-
a) Show that if f(n) is O(g(n)) and d(n) is O(h(n)), then f(n) d(n) is O(g(n) h(n)). b) Show that 3(n + 1)5 + 2n log n is O(n). c) Algorithm A executes 10n2 logn operations, while algorithm B...
-
a) Write a C++ program that ask the users for an odd integer (n), and displays the following pattern on the screen. Please use character literal and loop. For the example below, assume n =5; 00 000...
-
2.22 Convert each of the following expressions into sum of products and product of sums: (a) (u+xw)(x+u'v) (b) x' + x(x + y')(y + z')
-
Your branch target buffer (and branch history buffer) each have 8 slots. Your CPU executes the following code fragment. Assume that prediction takes place in the Fetch cycle, and that the result of a...
-
If you selected options "a" or "b" in question 1, assume now that the client has decided that they will make an adjustment of up to $250,000 to their financial statements. Please decompose the total...
-
Create a data model for one of the processes in the end-of-chapter Exercises for Chapter 4. Explain how you would balance the data model and process model.
-
Add, subtract, or multiple, as indicated. Express your answer as a single polynomial in standard form. (2x + 1) 3
-
Add, subtract, or multiple, as indicated. Express your answer as a single polynomial in standard form. (3x 2) 3
-
Find the quotient and the remainder. Check your work by verifying that (Quotient)(Divisor) + Remainder = Dividend 4x 3 3x 2 + x + 1 divided by x + 2
-
1.Discuss the methods of eliminating risks at the workplace and give 5 examples of administrative controls that management can implement. 2.You have been assigned to minimize the source noise emitted...
-
1) What did you learn from experience of group work? 2) Why is that learning important to you? activity or activities? How do you know if your actions were effective? What did you learn from your...
-
Protecting information resources. 1. What are six examples of information technologies that could be used in computer crimes. 2. What is the CIA triangle? 3. What are three most common security...

Study smarter with the SolutionInn App