Determine graphically any (a) Local extrema and (b) Absolute extrema. f(x) = 6 x + 2x +
Question:
Determine graphically any
(a) Local extrema and
(b) Absolute extrema.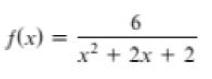
Transcribed Image Text:
f(x) = 6 x² + 2x + 2
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 83% (6 reviews)
a b The absolute maximum of 6 occurs ...View the full answer

Answered By

Carly Cimino
As a tutor, my focus is to help communicate and break down difficult concepts in a way that allows students greater accessibility and comprehension to their course material. I love helping others develop a sense of personal confidence and curiosity, and I'm looking forward to the chance to interact and work with you professionally and better your academic grades.
4.30+
12+ Reviews
21+ Question Solved
Related Book For 

College Algebra With Modeling And Visualization
ISBN: 9780134418049
6th Edition
Authors: Gary Rockswold
Question Posted:
Students also viewed these Mathematics questions
-
Determine graphically any (a) Local extrema and (b) Absolute extrema. f(x) 8 1 + x
-
Determine graphically any (a) Local extrema and (b) Absolute extrema. f(x) = -x + 4x - 8
-
Determine graphically any (a) Local extrema and (b) Absolute extrema. f(x) = -x + 4x - 4x
-
On May 1, Johnson Corporation purchased inventory for $40,000 on credit. On May 15, Johnson sold inventory with a cost of $10,000 for $25,000 on credit. Prepare journal entries to record these...
-
Beth Electronics makes DVD players in three processes: assembly, programming, and packaging. Direct materials are added at the beginning of the assembly process. Conversion costs are incurred evenly...
-
Students were surveyed on the number of visits to a Marc?s Milk convenience store (often, occasional, or never) and if the store was conveniently located to their school (yes or no) a. What is the...
-
Can option values be used to promote corporate legitimacy?
-
The Wilcox Student Health Center has just implemented a new computer system and service process to improve efficiency. The process flowchart and analysis framework is also provided. As pharmacy...
-
AAA has an issue regarding Alice, one of the members (of the LLC) that they would like us to research. As you may recall from our discussions, A limited liability company (LLC) combines the best...
-
Use the remainder theorem to find the remainder when f(x) is divided by the given x - k. f(x) = -x + 4x = x + 3 x-3
-
Use the remainder theorem to find the remainder when f(x) is divided by the given x - k. f(x) = 4x = x + 4x + 2 x+2
-
What is shopper marketing? Briefly explain and offer a new example of this concept.
-
How is centralized global cash management implemented?
-
How should multinationals structure their global earnings remittance strategy?
-
What are the defining characteristics of the Bretton Woods international monetary system?
-
Is international financial management different from domestic corporate finance?
-
What is corporate governance, and how does it vary across countries?
-
Are the self-regulatory attempts by the food and beverage industry enough in regard to regulating food marketing to children? What, if anything, additional would you propose? Explain.
-
Beginning with a country that has a trade deficit, demonstrate graphically what will happen to a countrys potential output with globalization if that countrys costs of production fall. Explain your...
-
In Exercises 3948, find the term indicated in each expansion. (x + 1); fourth term 2
-
In Exercises 4546, it is equally probable that the pointer on the spinner shown will land on any one of the eight regions, numbered 1 through 8. If the pointer lands on a borderline, spin again. Find...
-
In Exercises 4354, express each sum using summation notation. Use 1 as the lower limit of summation and i for the index of summation 1 4 + 2 4 + 3 4 +......+ 12 4
-
If you have a spectrum object, spectrum, and print the first few values of spectrum.fs, you'll see that they start at zero. So spectrum.hs[0] is the magnitude of the component with frequency 0. But...
-
1.)What can be done from an administrator's perspective to protect against WPA2-PSK bruteforce/cracking attacks assuming only WPA2-PSK can be used? Explain how this action will provide protection....
-
Data communication systems can be used in several different configurations, depending on users' needs, types of applications, and responsiveness of the system. During the past 60 years, three types...

Study smarter with the SolutionInn App