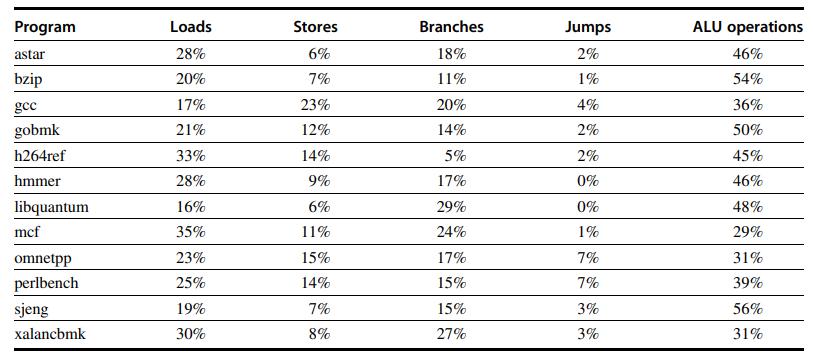
Compute the effective CPI for RISC-V using Figure A.29 and the table above. Average the instruction frequencies
Question:
Compute the effective CPI for RISC-V using Figure A.29 and the table above. Average the instruction frequencies of perlbench and sjeng to obtain the instruction mix.
Figure A.29
Transcribed Image Text:
Program astar bzip gec gobmk h264ref hmmer libquantum mcf omnetpp perlbench sjeng xalancbmk Loads 28% 20% 17% 21% 33% 28% 16% 35% 23% 25% 19% 30% Stores 6% 7% 23% 12% 14% 9% 6% 11% 15% 14% 7% 8% Branches 18% 11% 20% 14% 5% 17% 29% 24% 17% 15% 15% 27% Jumps 2% 1% 4% 2% 2% 0% 0% 1% 7% 7% 3% 3% ALU operations 46% 54% 36% 50% 45% 46% 48% 29% 31% 39% 56% 31%
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 100% (QA)

Answered By

Hassan Ali
I am an electrical engineer with Master in Management (Engineering). I have been teaching for more than 10years and still helping a a lot of students online and in person. In addition to that, I not only have theoretical experience but also have practical experience by working on different managerial positions in different companies. Now I am running my own company successfully which I launched in 2019. I can provide complete guidance in the following fields. System engineering management, research and lab reports, power transmission, utilisation and distribution, generators and motors, organizational behaviour, essay writing, general management, digital system design, control system, business and leadership.
5.00+
1+ Reviews
10+ Question Solved
Related Book For 

Computer Architecture A Quantitative Approach
ISBN: 9780128119051
6th Edition
Authors: John L. Hennessy, David A. Patterson
Question Posted:
Students also viewed these Computer science questions
-
Compute the effective CPI for RISC-V using Figure A.29 and the table above. Average the instruction frequencies of bzip and hmmer to obtain the instruction mix. You may assume that all other...
-
Compute the effective CPI for an implementation of an embedded RISC-V CPU using Figure A.29. Assume we have made the following measurements of average CPI for each of the instruction types: Figure...
-
Instructions: Read the footnotes included in the financial statements for H & B Bakery, then answer the following questions. *The exact requirement of this question, is to read the statements below...
-
A 75.0-kg wrecking ball hangs from a uniform heavy-duty chain having a mass of 26.0 kg. (a) Find the maximum and minimum tension in the chain. (b) What is the tension at a point three fourths of the...
-
Which of the following would be expected to have a dipole moment of zero on the basis of symmetry? Explain. a. SOCl 2 b. SiF 4 c. OF 2
-
At 3:00 a.m. on November 22, 2010, 16-year-old Sydney McLemore was driving a Mazda3 with her friend, Natalie Hurst, in the front passenger seat. The vehicle was traveling south on Ross Bridge Highway...
-
Lott Company specializes in manufacturing a unique model of bicycle helmet. The model is well accepted by consumers, and the company has enough orders to keep the factory production at 10,000 helmets...
-
ELLA'S ELECTRONICS ACCOUNTING PROJECT PART 2Adjusting InformationAt the end of February, the following information is determined:a. One month of the business insurance coverage has expired.b. At the...
-
When buying or leasing a new car, one of the factors that customers consider is the type of fuel it uses. Some people prefer vehicles that use diesel fuel, while others favor vehicles that use...
-
Compiler optimizations may result in improvements to code size and/or performance. Consider one or more of the benchmark programs from the SPEC CPU2017 or the EEMBC benchmark suites. Use the RISC-V...
-
Compute the effective CPI for an implementation of a RISC-V CPU using Figure A.29. Assume we have made the following measurements of average CPI for each of the instruction types: Figure A.29...
-
In Exercises 9 through 12, use logarithmic rules to rewrite each expression in terms of log 3 2 and log 3 5. log 3 100
-
The Canadian Restaurant Association states that the restaurant industry has an economic effect of more than $1.7 trillion annually, with every dollar spent in restaurants generating an estimated...
-
The next two questions are about interacting with people during COVID. When we encounter another person these days, we would like to know how likely it is that they have COVID-19 before we get too...
-
Macy's, long a leading department store in the United States, is trying a variety of new tactics to attract shoppers to its stores in the face of a sales decline. This activity is important because...
-
Provide two methods of developing environmental sustainability plans by providing an outline of how to implement each method. Method 1 Method 2
-
The Big Choo Choo Company (BCCC) owns a rail line from the town of Isolated to the coastal port of Notso. It cost them $20 million to build the rail line in 2016. It is now 2023. The Small Gold...
-
1. Baxendale was obviously late in transporting the shaft. What is the dispute about, anyway? 2. In Baxendales view, why would it be unfair to hold him liable for lost profits? 3. According to this...
-
In a paragraph of approximately 150-200 words, analyze a film or TV/Streaming Show poster of your choosing by focusing on the ways in which representations in the poster are gendered. Include an...
-
Power efficiency has become very important for modern processors, particularly for embedded systems. Create a version of gcc for two architectures that you have access to, such as x86, MIPS, PowerPC,...
-
How big should a TLB be? TLB misses are usually very fast (fewer than 10 instructions plus the cost of an exception), so it may not be worth having a huge TLB just to lower the TLB miss rate a bit....
-
It is possible to provide more flexible protection than that in the Intel Pentium architecture by using a protection scheme similar to that used in the Hewlett-Packard Precision Architecture (HP/PA)....
-
How difficult would it be to integrate new systems into your cloud infrastructure? If you were to progressively add virtual machines (VMs) to your cloud deployment without increasing capacity, what...
-
1. What network services did we investigate today? Your answer 2. Are these the only important network services? If so, why? If not, what are some of the other ones? Your answer
-
1. Explain the concept of authentication adaptors. What is biometric authentication? 2. Explain network authentication services, including Kerberos and NT LAN Manager (NTLM). 3. List principles of...

Study smarter with the SolutionInn App