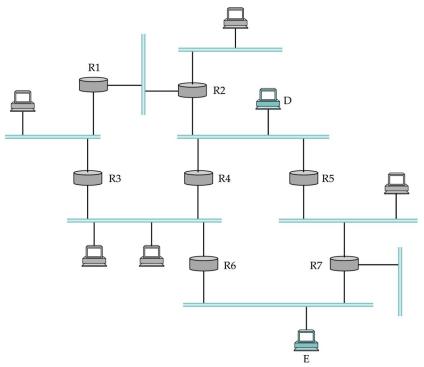
Consider the example internet shown in Figure 4.30, in which sources D and E send packets to
Question:
Consider the example internet shown in Figure 4.30, in which sources D and E send packets to multicast group G, whose members are shaded in gray. Show the shortest path multicast trees for each source.
Figure 4.30)
Transcribed Image Text:
R1 R3 R2 R4 R6 D R5 R7 E
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 100% (QA)

Answered By

Carly Cimino
As a tutor, my focus is to help communicate and break down difficult concepts in a way that allows students greater accessibility and comprehension to their course material. I love helping others develop a sense of personal confidence and curiosity, and I'm looking forward to the chance to interact and work with you professionally and better your academic grades.
4.30+
12+ Reviews
21+ Question Solved
Related Book For 

Computer Networks A Systems Approach
ISBN: 9780128182000
6th Edition
Authors: Larry L. Peterson, Bruce S. Davie
Question Posted:
Students also viewed these Computer science questions
-
Consider the example internet shown in Figure 4.31, in which sources S1 and S2 send packets to multicast group G, whose members are shaded in gray. Show the shortest-path multicast trees for each...
-
Transaction Analysis Goal Systems, a business consulting firm, engaged in the following transactions: a. Issued common stock for $50,000 cash. b. Borrowed $10,000 from a bank. c. Purchased equipment...
-
Investigate the properties of the polynomial equation f(x) = x + 5x6 +x4 - x + x - 2 = 0, by proceeding as follows. (a) By writing the fifth-degree polynomial appearing in the expression for f'(x) in...
-
Solve the compound linear inequality graphically. Write the solution set in set-builder or interval notation, and approximate endpoints to the nearest tenth whenever appropriate. 1.59.10.5x6.8
-
A 10-GHz weather radar uses a 15-cm-diameter lossless antenna. At a distance of 1 km, what are the dimensions of the volume resolvable by the radar if the pulse length is 1 s?
-
Identity theft often begins by someone discovering your nine-digit social security number or your credit card number. Answer each of the following. Express probabilities as fractions. a. What is the...
-
The company is committed to ethical conduct and has no tolerance for fraud and unethical behavior. There are some concerns about abuses in your department. Do you know anything about the concerns I...
-
Cost Behavior and Cost-Volume-Profit Analysis for Many Glacier Hotel The purpose of this integrated exercise is to demonstrate the interrelationship between cost estimation techniques and subsequent...
-
Suppose a home's UATOTAL for heating is 1500 BTU/hr-F. Suppose the average outdoor temperature over a day is 28F and the desired indoor temperature is 68 F. Any electricity the heating system uses...
-
Suppose host A is sending to a multicast group; the recipients are leaf nodes of a tree rooted at A with depth N and with each nonleaf node having k children; there are thus k N recipients. (a) How...
-
Under what conditions could a nonrouter host on an Ethernet receive a IP multicast packet for a multicast group it has not joined?
-
1. What is the maximum voltage in an ac circuit in which the instantaneous voltage at = 35.0 is 27.0 V? 2. The instantaneous voltage in an ac circuit at = 65.0 is 82.0 V. What is the maximum...
-
Data (attributes) - all have private access double quadraticCoefficient (this is the coefficient of the quadratic term of the polynomial) double linearCoefficient (this is the coefficient of the...
-
identify some of the risk that firms face and explain on the strategies that they use to mitigate the risks as part of their risk management effort. Use Kontiki Finance (Finance company in Fiji) and...
-
Rona Sdn Bhd is a retail company. For the purpose of company planning and control, the company intends to prepare a budget for the first half of 2024, from January to June 2024. The following...
-
Let U = span span {(64) (9)} s C M2x2(C). Find U. Use the inner product (A, B) = tr(BHA). (Recall that tr(M) is the trace function, i.e., the sum of the diagonal entries of M, and MH denotes the...
-
I am having issues printing the display from the staff and manager can you please assist? public abstract class Cisco { private String phone; private int phonemodel; public Cisco (String phone, int...
-
You have been asked to develop a work breakdown structure for a project. How should you go about accomplishing this? Should the WBS be time-phased, department-phased, division-phased, or some...
-
A company pledges their receivables so they may Multiple Choice Charge a factoring fee. Increase sales. Recognize a sale. Collect a pledge fee. Borrow money. Failure by a promissory notes' maker to...
-
Imagine that someone in the math department at Stanford has just written a new document including a proof that he wants to distribute by FTP for his colleagues to review. He puts the program in the...
-
Is it possible that when a user clicks on a link with Firefox, a particular helper is started, but clicking on the same link in Internet Explorer causes a completely different helper to be started,...
-
Consider the Chord circle of Fig. 7-71. Suppose that node 18 suddenly goes online. Which of the finger tables shown in the figure are affected? how? Figure 7-71 of successor 4 31 (30 29 Start Actual...
-
The current market price of a stock is 45.5. Over the next two quarters, this stock is projected to either increase by 7% or decrease by 6% each period, as per a binomial lattice model. The risk-free...
-
Good discussion so far on the general application of the NPV and IRR formulas. Let's say the pizza oven is depreciated for 10 years, cost of the oven is $100,000, tax rate is 30%, it does not change...
-
Varun invested in a $ 3 0 0 0 , 2 0 % 1 5 - year quarterly bond for $ ( 3 6 0 0 ) , aiming to sell it after 5 years, right after the 2 0 th bond coupon payment has been collected ) . a ) What sale...

Study smarter with the SolutionInn App