Figure 28.43 shows the generated and the arrival time for ten audio packets. Answer the following questions:
Question:
Figure 28.43 shows the generated and the arrival time for ten audio packets. Answer the following questions:
Figure 28.43
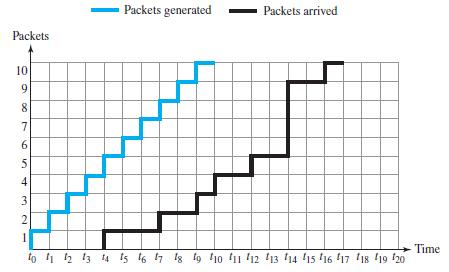
a. If we start our player at t8, which packets cannot be played?
b. If we start our player at t9, which packets cannot be played?
Transcribed Image Text:
Packets generated Packets arrived Packets 10 9. 7 5 3 Time to 1 2 13 14 is 16 7 1g tg 1o f11 '12 13 14 15 16 17 18 19 20 6, 4) 2I
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 60% (10 reviews)
We can use a table in each case to see which packets arrive...View the full answer

Answered By

ANDREW KIPRUTO
Academic Writing Expert
I have over 7 years of research and application experience. I am trained and licensed to provide expertise in IT information, computer sciences related topics and other units like chemistry, Business, law, biology, biochemistry, and genetics. I'm a network and IT admin with +8 years of experience in all kind of environments.
I can help you in the following areas:
Networking
- Ethernet, Wireless Airmax and 802.11, fiber networks on GPON/GEPON and WDM
- Protocols and IP Services: VLANs, LACP, ACLs, VPNs, OSPF, BGP, RADIUS, PPPoE, DNS, Proxies, SNMP
- Vendors: MikroTik, Ubiquiti, Cisco, Juniper, HP, Dell, DrayTek, SMC, Zyxel, Furukawa Electric, and many more
- Monitoring Systems: PRTG, Zabbix, Whatsup Gold, TheDude, RRDtoo
Always available for new projects! Contact me for any inquiries
4.30+
1+ Reviews
10+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
Figure 15.23 shows the frame format of the baseband layer in Bluetooth (802.15). Based on this format, answer the following questions: Figure 15.23 a. What is the range of the address domain in a...
-
Answer the following questions related to the FSMs for the Go-back-N protocol with m = 6 bits. Assume the window size is 63. (Figure 23.27):
-
Answer the following questions related to the FSMs for the Selective-Repeat protocol with m = 7 bits. Assume the window size is 64. (Figure 23.34): a. The sending machine is in the ready state with S...
-
(a) Compute the primary Class 1 NICs payable by the following weekly-paid employees for the week ending 14 August 2020: (i) Employee A has earnings for the week of 110. (ii) Employee B has earnings...
-
With reference to a particular example, explain how an organisation might seek to communicate its corporate brand identity.
-
Jobco is planning to produce at least 2000 widgets on three machines. The minimum lot size on any machine is 500 widgets. The following table gives the pertinent data of the situation. Formulate the...
-
Pick out the correct relation between the \(\mathrm{COP}\) of a refrigerator \(\left(\mathrm{COP}_{\mathrm{R}} ight)\) and that of the heat pump \(\left(\mathrm{COP}_{\mathrm{HP}} ight)\) (a)...
-
(Disclosures: Pension Expense and Other Comprehensive Income) Tavares Enterprises provides the following information relative to its defined benefit pension plan. (a) Prepare the note disclosing the...
-
Provide an example of a Cross Site Scripting (XSS) attack. Include an explanation of the differences between stored and reflective XSS attacks. 2). Provide an example of a SQL Injection attack. Why...
-
Sherina Smith (Social Security number 785-23-9873) lives at 536 West Lapham Street, Milwaukee, WI 53204, and is self-employed for 2019. She estimates her required annual estimated tax payment for...
-
In the fourth approach to streaming audio/video (Figure 28.27), what is the role of RTSP? Figure 28.27 Server machine Client machine GET: metafile Web Browser RESPONSE server 3 Metafile SETUP...
-
Given an RTP packet with the first 8 hexadecimal digits as (86032132) 16 , answer the following questions: a. What is the version of the RTP protocol? b. Is there any padding for security? c. Is...
-
In Problems 3340, find the nth term a n of each geometric sequence. When given, r is the common ratio. 43 || 46 || -la 81
-
Discuss the sampling strategy and technique to be used. Develop a hypothetical research scenario that would necessitate the use of the Qualitative Method and the Grounded Theory Perspective. The...
-
How will these threats be addressed in accordance, based on the discussion of the control techniques in the previous question? Develop a hypothetical research scenario that would necessitate the use...
-
Develop the appropriate primary research question to be associated with this design. Develop a hypothetical research scenario that would necessitate the use of the Qualitative Method and the Grounded...
-
What type of sampling procedure and sampling technique will be used to access the appropriate sample? Develop a hypothetical research scenario that would necessitate the use of a Longitudinal Design....
-
Identify the research scenario, including the relevant predictor variable and criterion variable. Develop a hypothetical research scenario that would necessitate the use of a Predictive Design. The...
-
Refer to the loglinear models for Table 8.8. a. Explain why the fitted odds ratios in Table 8.10 for model (GI, GL, GS, IL, IS, LS) suggest that the most likely accident case for injury is females...
-
Which provision could best be justified as encouraging small business? a. Ordinary loss allowed on $ 1244 stuck. b. Percentage depletion. c. Domestic production activates deductions. d. Interest...
-
When should an underscore symbol ( _ ) be used with the LIKE operator?
-
Because % is a wildcard character, how can the LIKE operator search for a literal percent sign (%) in a character string?
-
Which of the following SQL statements isnt valid? a. SELECT address || city || state || zip "Address" FROM customers WHERE lastname='SMITH'; b. SELECT * FROM publisher ORDER BY contact; c. SELECT...
-
Question 3 (4 marks) Students at the school who are studying mathematics in Years 7 to 10 can receive one of three grades at the end of the year: distinction (D), credit (C) or pass (P). A regular...
-
How has technology brought about social change in your lives in comparison to your parents' and your grandparents' generation? how has technology brought about change in your grandparents'/parents'...
-
Identify the role and function of the major components of the Canadian criminal justice system Demonstrate the manner in which the criminal justice system components relate and interact with each...

Study smarter with the SolutionInn App


