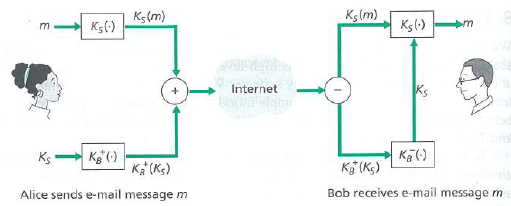
Figure 8.19 shows tie operations that Alice must perform with POP to provide confidentiality, authentication, and integrity.
Question:
Figure 8.19
Transcribed Image Text:
Kşlm) Kg(m) K5() Ksl) Internet Kg () Ks Kg (Ks) Ka (KG) Bob receives e-mail message m Alice sends e-mail message m
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 88% (9 reviews)
Figure Operations performed b...View the full answer

Answered By

Muhammad Umair
I have done job as Embedded System Engineer for just four months but after it i have decided to open my own lab and to work on projects that i can launch my own product in market. I work on different softwares like Proteus, Mikroc to program Embedded Systems. My basic work is on Embedded Systems. I have skills in Autocad, Proteus, C++, C programming and i love to share these skills to other to enhance my knowledge too.
3.50+
1+ Reviews
10+ Question Solved
Related Book For 

Computer Networking A Top-Down Approach
ISBN: 978-0133594140
7th edition
Authors: James Kurose, Keith Ross
Question Posted:
Students also viewed these Computer science questions
-
Figure 8.20 shows the operations that Alice must perform with PGP to provide confidentiality, authentication, and integrity. Diagram the corresponding perations that Bob must perform on the package...
-
Consider our authentication protocol in Figure 8.18 in which Alice authenticates herself to Bob, which we saw works well (i.e., we found no flaws in hi. Now suppose that while Alice is authenticating...
-
1. Based on the fact statements provided, summarize the maintenance departments most important strengths, weaknesses, opportunities, and threats. 2. Compared to a profit-making company, is it more...
-
Please graphically demonstrate the effects on the level of prices and the value of money if consumers increase their spending due to stock market boom and therefore make more transactions. On the...
-
Read the Country Focus on Venezuela under the leadership of Hugo Chvez, then answer the following questions: a. Under Chvez's leadership, what kind of economic system was put in place in Venezuela?...
-
The Wilcox Student Health Center has just implemented a new computer system and service process to improve efficiency. The process flowchart and analysis framework is also provided. As pharmacy...
-
The City of Central Falls has engaged Robert Cohen, CPA to audit the June 30, 1999 financial statements of the City's Water Department under the GAO's Government Auditing Standards. Cohen's report...
-
The comparative balance sheets for Yanik Company as of December 31 are presented below. Additional information: 1. Operating expenses include depreciation expense of $42,000. 2. Land was sold for...
-
The Segway is a two-wheeled self-balancing electric vehicle, as shown in Fig. 1. In this problem, we only consider the translational motion of the vehicle and rotation of the control panel bar. The...
-
InstraMatronics, a distributor of electrical monitoring equipment, is looking to reduce inventory costs. Hal, the new materials manager, is considering the inventory policy for HS008, a popular...
-
In the SSL record, there is a field for SSL sequence numbers. True or false?
-
What does it mean to say that a nonce is a once-in-a-lifetime value? In whose lifetime?
-
Can a business enter into a transaction that affects only the left side of the basic accounting equation? If so, give an example.
-
Explain the reasoning behind the creation of copyright law and what its impacts are. such as: to benefit society, to protect an author's creative work, economic reasons, and/or incentives. outside...
-
Explain how advanced computational methods, such as Monte Carlo simulation and Bayesian networks, can be applied to improve hazard analysis accuracy and reduce uncertainty in risk assessment .
-
Fresh Fruit, Inc. has a $3,000 par value bond that is currently selling for $1,457. It has an annual coupon rate of 14.86 percent, paid semiannually, and has 22-years remaining until maturity. What...
-
What do you think of the accuracy of your perceptions of the average "typical" American diet? Any surprises?Use this website "https://insteading.com/blog/food-consumption-in-america/" Do you agree...
-
Discuss the role of human factors in hazard analysis. How do techniques like Human Reliability Analysis (HRA) contribute to understanding and mitigating risks associated with human errors in...
-
The spectral emissivity of an opaque surface at 1500 K is approximated as Determine the total emissivity and the emissive flux of thesurface. for <2 m | -0 0.85 ) for 2 6 for for >6 =0
-
Use a calculator to evaluate the expression. Round your result to the nearest thousandth. V (32 + #)
-
Suppose the information content of a packet is the bit pattern 1110 10 II 100 I 1101 and an even parity scheme is being used, What would the value of the field containing the parity bits be for the...
-
Consider two nodes, A and B, that use the slotted ALOHA protocol to contend for a channel. Suppose node A has more data to transmit than node B. and node A's retransmission probability PAis greater...
-
Suppose four active nodes-nodes A, B, C and D-are competing for access to a channel using slotted ALOHA. Assume each node has an infinite number of packets to send. Each node attempts to transmit in...
-
How do the resource descriptions (typing) used in the Incident Command System lead to a more effective response?
-
A company incurs $4172000 of overhead each year across three departments: Ordering and Receiving, Mixing, and Testing. The company prepares 2000 purchase orders, works 50000 mixing hours, and...
-
Hemming Company reported the following current-year purchases and sales for its only product. Date January 1 January 10 Activities Beginning inventory March 14 March 15 July 30 Sales Purchase Sales...

Study smarter with the SolutionInn App


