In Figure 19.4, show how the sum, wrapped sum, and checksum can be calculated when each word
Question:
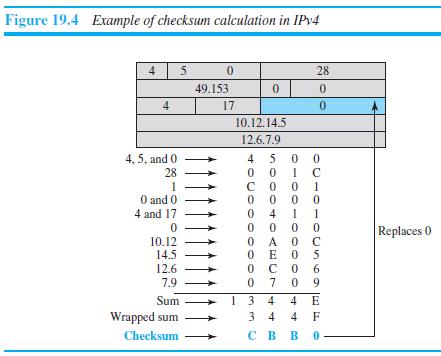
In Figure 19.4, show how the sum, wrapped sum, and checksum can be calculated when each word (16 bits) is created instead of waiting for the whole packet to be created.
Transcribed Image Text:
Figure 19.4 Example of checksum calculation in IPV4 4 5 0. 28 49.153 0. 4 17 10.12.14.5 12.6.7.9 4 5 0 0 4, 5, and 0 28 1 O and 0 4 and 17 1 0 0 O A 0 C O E O 5 с о 0 9 4 Replaces 0 10.12 14.5 12.6 6. 7.9 7 1 3 4 3 4 Sum 4 E Wrapped sum 4 F Checksum св в о. 0-00-0
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 66% (6 reviews)
We can calculate the sum wrapped sum and checksum after each word if we keep track of the sum i...View the full answer

Answered By

Sarfraz gull
have strong entrepreneurial and analytical skills which ensure quality tutoring and mentoring in your international business and management disciplines. Over last 3 years, I have expertise in the areas of Financial Planning, Business Management, Accounting, Finance, Corporate Finance, International Business, Human Resource Management, Entrepreneurship, Marketing, E-commerce, Social Media Marketing, and Supply Chain Management.
Over the years, I have been working as a business tutor and mentor for more than 3 years. Apart from tutoring online I have rich experience of working in multinational. I have worked on business management to project management.
5.00+
3+ Reviews
10+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
Show how the sum of two five-bit integers can be found using full and half adders.
-
In Figure 11.9, we show the packet path as a horizontal line, but the frame path as a diagonal line. Can you explain the reason? Figure 11.9 Sending node Receiving node Network Network Data-link...
-
Suppose, instead of waiting for the economy described in question 13 to return to long-run equilibrium, the central bank opted to use the positive supply shock as an opportunity to move to a lower...
-
If Converse introduced a new SMART WATCH for Men and Women, should they launch the product using Market Skimming or Marketing Penetration? Explain answer
-
Aquatech is a U.S.-based company that manufactures, sells, and installs water purification equipment. On April 11, the company sold a system to the City of Nagasaki, Japan, for installation in...
-
Rustafson Corporation is a diversified manufacturer of consumer goods. The company's act the following seven activity cost pools: Activity Cost Pool Labor-related Estimated Overhead Cost $ 17,200...
-
The two wires are connected together at A. If the force P causes point A to be displaced horizontally 2 mm, determine the normal strain developed in each wire. C 300 mm 30 B 300 mm 30 A -P
-
Yount Co. has equipment that cost $50,000 and that has been depreciated $22,000. Record the disposal under the following assumptions. (a) It was scrapped as having no value. (b) It was sold for...
-
A tin of cat food weighing 28 g is placed at the top of a dry chopping board made of wood and the board is slowly raised in angle until the tin slides downwards. Measured by the mid-point of a...
-
In the model displayed in the Exhibit above, which predictor variables are most likely to be chosen by a Stepwise regression approach for best model fit. You may use JMP Stepwise Regression operation...
-
Mention the three auxiliary protocols at the network layer of the TCP/IP suite that are designed to help the IPv4 protocol.
-
In an IPv4 datagram, the value of the header-length (HLEN) field is (6) 16 . How many bytes of options have been added to the packet?
-
Kangaroo Jim Company reported beginning inventory of 100 units at a per unit cost of $25. It had the following purchase and sales transactions during 2012: Jan. 14 Sold 25 units at unit sales price...
-
Show that \(\mathbf{x}_{i} \perp y_{i t} \mid \mathbf{x}_{i t}\) and \(E\left(y_{i t} \mid \mathbf{x}_{i t} ight)=\mu_{i t}\) imply the FCCM.
-
In January 2009, approximately how many employees did Satyam Computer Services employ?
-
Express the AUC of a binormal ROC curve in terms of the means and variances of the two underlying normal distributions.
-
In a study to determine the distribution of time to the occurrence of cancer after exposure to certain type of carcinogen, a group of mice is injected with the carcinogen, and then sacrificed and...
-
Show that the ROC curve is invariant under monotone transformation of the test variable.
-
Which has more total energy: a hydrogen atom with an electron in a high shell (large n) or in a low shell (small n)? Which is moving faster: the high shell electron or the low-shell electron? Is...
-
Privitera and Freeman (2012) constructed a scale to measure or estimate the daily fat intake of participants; the scale was called the estimated daily intake scale for fat (EDIS-F). To validate the...
-
A token bucket scheme is used for traffic shaping. A new token is put into the bucket every 5 sec. Each token is good for one short packet, which contains 48 bytes of data. What is the maximum...
-
The network of Fig. 5-34 uses RSVP with multicast trees for hosts 1 and 2 as shown. Suppose that host 3 requests a channel of bandwidth 2 MB/sec for a flow from host 1 and another channel of...
-
A router can process 2 million packets/sec. The load offered to it is 1.5 million packets/ sec on average. If a route from source to destination contains 10 routers, how much time is spent being...
-
Why is compassion and empathy valuable traits to have as a leader ?
-
what leadership development activities are most likely to be successful for the TRS society
-
As a support services worker, you may be tasked with not only assisting your assigned client but also the members of the community in which your client will reside. You will also be a part of case...

Study smarter with the SolutionInn App


