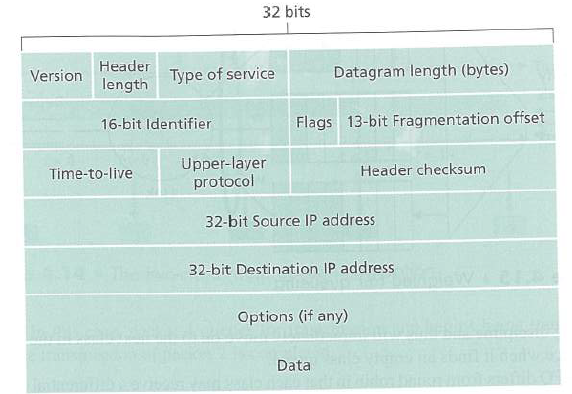
Recall that we the Internet checksum being used in both transport-layer segment (in UDP and TCP headers,
Question:
Figure 3.7
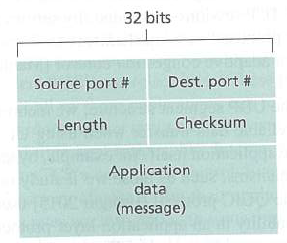
Figure 3.29
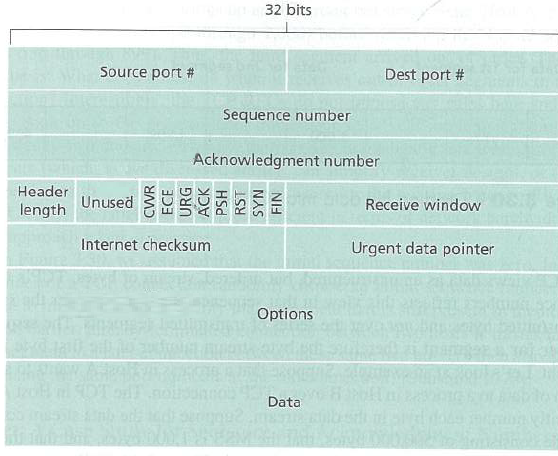
Figure 4.16
Transcribed Image Text:
32 bits Dest. port # Source port # Checksum Length Application data (message) 32 bits Source port # Dest port # Sequence number Acknowledgment number Header Unused 3 Receive window length Internet checksum Urgent data pointer Options Data NIH NAS HSd ACK URG
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 87% (8 reviews)
No IP header checksum only compu...View the full answer

Answered By

Aysha Ali
my name is ayesha ali. i have done my matriculation in science topics with a+ . then i got admission in the field of computer science and technology in punjab college, lahore. i have passed my final examination of college with a+ also. after that, i got admission in the biggest university of pakistan which is university of the punjab. i am studying business and information technology in my university. i always stand first in my class. i am very brilliant client. my experts always appreciate my work. my projects are very popular in my university because i always complete my work with extreme devotion. i have a great knowledge about all major science topics. science topics always remain my favorite topics. i am also a home expert. i teach many clients at my home ranging from pre-school level to university level. my clients always show excellent result. i am expert in writing essays, reports, speeches, researches and all type of projects. i also have a vast knowledge about business, marketing, cost accounting and finance. i am also expert in making presentations on powerpoint and microsoft word. if you need any sort of help in any topic, please dont hesitate to consult with me. i will provide you the best work at a very reasonable price. i am quality oriented and i have 5 year experience in the following field.
matriculation in science topics; inter in computer science; bachelors in business and information technology
_embed src=http://www.clocklink.com/clocks/0018-orange.swf?timezone=usa_albany& width=200 height=200 wmode=transparent type=application/x-shockwave-flash_
4.40+
11+ Reviews
14+ Question Solved
Related Book For 

Computer Networking A Top-Down Approach
ISBN: 978-0133594140
7th edition
Authors: James Kurose, Keith Ross
Question Posted:
Students also viewed these Computer science questions
-
Suppose that the UDP receiver computes the Internet checksum for the received UDP segment and finds that it matches the value carried in the checksum field. Can the receiver be absolutely certain...
-
YourFire, Inc., (the same YourFire we met at the end of Chapter 3, p. 75) is a small business owned by Curt and Julie Robards. Based in Brisbane, Australia, YourFire manufacturers and sells the...
-
Recall that TCP can be enhanced with SSL to provide process-to-process security services, including encryption. Does SSL operate at the transport layer or the application layer? If the application...
-
Find keys K such that DESK (DESK (x)) = x, for all x Such a key is sometimes called a weak key. How many weak keys can you find? To solve this problem you need to look up the exact key schedule...
-
Members of minority groups and women have made enough economic progress in the last several decades that they no longer need special legislation to protect them. Explain
-
The December 31 trial balance of Red Roses Boutique Inc. follows: Instructions (a) Create T accounts and enter the balances shown. (b) Prepare adjusting entries for the following and post to the T...
-
The activity of the component is defined as the ratio of (a) The fugacity of the component in the solution to the fugacity of the component in the ideal state (b) The fugacity of the component in the...
-
On May 22, 2012, the audit firm of Brock, Schechter & Polakoff LLP (hereafter BSP) was censured and fined $20,000 by the PCAOB in relation to its audits of public companies located in Taiwan and...
-
The City of McAllen has a water filtration system that consistsof a large rigid tank with a single 0.26 m diameter inlet pipe andtwo 0.12 m diameter exit pipes. Water enters the system through...
-
Which entities on the chart are affiliates of the audit client Port Co A? 100% ownership. 55% fund assets Port. Co. A Audit Client Fund 1 30% ownership, 4% fund assets Port. Co. B GP/RIA 1% ownership...
-
When a large data-gram is fragmented into multiple smaller data-grams, where are these smaller data-grams reassembled into a single larger data-gram?
-
Consider the SDN Open Flow network shown in Figure 4.30. Suppose that the desired forwarding behavior for data-grams arriving at s2 is as follows: Any datgrams arriving on input port 1 from hosts h5...
-
In Problems a-b, f"(x) is given. Find f (x) by antidifferentiating twice. Note that in this case your answer should involve two arbitrary constants, one from each antidifferentiation. For example, if...
-
A person inherited $34000 and invests it immediately at 8.75% compounded monthly. The person decides to quit his/her job and withdraws $1700 at the end of each month for as long as possible. a. How...
-
A bond is selling at par with the Macaulay duration of 11.2 years and the modified duration of 10.6 years. The convexity of the bond is 196. According to the duration rule, a 2% decrease in yield...
-
A desk is made of wood with density 9 0 0 kg m - 3 . It consists of a desktop 1 2 0 cm wide, 2 cm thick and 9 0 cm deep, resting on four square wooden legs 8 0 cm long and 5 cm on the other two...
-
Control systems exist in numerous varieties, both in type of applications and level of sophistications. Since most systems are dynamic in nature, to control or regulate against a set of desired...
-
A rigid container contains an ideal gas 40C which is stirred by a blade. The blade produces 200kJ of work. The temperature remains constant thanks to a heat exchange with the surroundings which are...
-
Table 11.3 gives probabilities for various combinations of events A, B, and their complements. Table 11.3 Find P(A). not A 0.4 B 0.2 not B 0.1 0.3
-
Choose a company from the SEC EDGAR Web site for your Key Assignment to evaluate for the impact of convergence to IFRS. Review the financial reports and notes of the company you have chosen from the...
-
What is the length of a bit in a channel with a propagation speed of 2 10 8 m/s if the channel bandwidth is a. 1 Mbps? b. 10 Mbps? c. 100 Mbps?
-
What is the transmission time of a packet sent by a station if the length of the packet is 1 million bytes and the bandwidth of the channel is 200 Kbps?
-
We have a channel with 4 KHz bandwidth. If we want to send data at 100 Kbps, what is the minimum SNR dB ? What is the SNR?
-
X1155: Throwing an Exception The method below takes in a String parameter representing a username. It should throw an Exception if the username is less than 3 characters long. The method correctly...
-
Catch Exception The method divideValues() will throw an IllegalArgumentException if either parameter is 5. The method below takes two integer values as parameters and calls divideValues() in a try...
-
Wyoming Products Inc. completed and transferred 145,000 particle board units of production from the Pressing Department. There was no beginning inventory in process in the department. The ending...

Study smarter with the SolutionInn App


