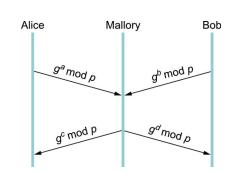
The DiffieHellman key exchange protocol is vulnerable to a manin-the-middle attack as shown in Figure 8.7. Outline
Question:
The Diffie–Hellman key exchange protocol is vulnerable to a “manin-the-middle” attack as shown in Figure 8.7. Outline how Diffie–Hellman can be extended to protect against this possibility.
Figure 8.7)
Transcribed Image Text:
Alice g mod p gf mod p Mallory g mod p go mod p Bob
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 0% (1 review)

Answered By

Asim farooq
I have done MS finance and expertise in the field of Accounting, finance, cost accounting, security analysis and portfolio management and management, MS office is at my fingertips, I want my client to take advantage of my practical knowledge. I have been mentoring my client on a freelancer website from last two years, Currently I am working in Telecom company as a financial analyst and before that working as an accountant with Pepsi for one year. I also join a nonprofit organization as a finance assistant to my job duties are making payment to client after tax calculation, I have started my professional career from teaching I was teaching to a master's level student for two years in the evening.
My Expert Service
Financial accounting, Financial management, Cost accounting, Human resource management, Business communication and report writing. Financial accounting : • Journal entries • Financial statements including balance sheet, Profit & Loss account, Cash flow statement • Adjustment entries • Ratio analysis • Accounting concepts • Single entry accounting • Double entry accounting • Bills of exchange • Bank reconciliation statements Cost accounting : • Budgeting • Job order costing • Process costing • Cost of goods sold Financial management : • Capital budgeting • Net Present Value (NPV) • Internal Rate of Return (IRR) • Payback period • Discounted cash flows • Financial analysis • Capital assets pricing model • Simple interest, Compound interest & annuities
4.40+
65+ Reviews
86+ Question Solved
Related Book For 

Computer Networks A Systems Approach
ISBN: 9780128182000
6th Edition
Authors: Larry L. Peterson, Bruce S. Davie
Question Posted:
Students also viewed these Computer science questions
-
The Crazy Eddie fraud may appear smaller and gentler than the massive billion-dollar frauds exposed in recent times, such as Bernie Madoffs Ponzi scheme, frauds in the subprime mortgage market, the...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Bakers yeast is produced in a 50,000-litre fermenter under aerobic conditions. The carbonnsubstrate is sucrose; ammonia is provided as the nitrogen source. The average biomassncomposition is CH1.83...
-
Solve the right triangles with the given parts or state that there is not enough information to solve. Round off results according to Table 4.1. Refer to Fig. 4.37. B = 32.1, c = 238 Data from Table...
-
Suppose that the logons to a computer network follow a Poisson process with an average of 3 counts per minute. (a) What is the mean time between counts? (b) What is the standard deviation of the time...
-
The volume of cola in a can of regular Coke is 12.3 oz. Determine whether the given values are from a discrete or continuous data set.
-
In September 2013, Ugo Mattera entered into a written construction contract with Baja Properties, LLC. Stephen Chad Golden, the sole owner of Baja Properties, signed the contract and addendums on...
-
Howie Stars produces stars for elementary teachers to reward their students. Howie Stars trial balance on June 1 follows: June 1 balances in the subsidiary ledgers were as follows: ¢ Materials...
-
In service partnerships, if properly booked for tax purposes pursuant to Treasury Regulations under IRC 731, partners who receive so-called "draw" allowances are not deemed to receive distributions...
-
Suppose we have a very short secret s (e.g., a single bit or even a Social Security number), and we wish to send someone else a message m now that will not reveal s but that can be used later to...
-
Suppose a user employs one-time passwords as above (or, for that matter, reusable passwords) but that the password is transmitted sufficiently slowly. (a) Show that an eavesdropper can gain access to...
-
A flagpole is guyed by three cables. If the tensions in the cables have the same magnitude P, replace the forces exerted on the pole with an equivalent wrench and determine (a) The resultant force R,...
-
3. (30 points) Given the following function, when r is a 1 x 60 vector with linearly spaced values from 0 to 1.7 and 0 is a 1 x 73 vector with linearly spaced values from 0 to 2: I = T COS(0) Y = r...
-
Using this knowledge about the concepts of employees' empowerment and autonomy, suggest five practical work-related policies and practices that a Human Resource Manager can promulgate.
-
SEC Charges Seismic Data Company, Former Executives with $100 Million Accounting Fraud CASE. https://www.sec.gov/files/litigation/complaints/2020/comp24943.pdf can you provide a introduction on what...
-
Your are a supervisor for an ethnically diverse team within a manufacturing facility. You wish to seek input from your team on managing workplace health and safety compliance issues. You know a...
-
SHINAGAWA MONKEY - HARUKI MURAKAMI 2006 Describe a connection between the protagonist & the monkey in terms of trauma / isolation / depression in details. What things lead them to the loneliness /...
-
Refer to the CVS annual report in the Supplement to Chapter 5 to answer the questions below. Keep in mind that every company, while following basic principles, adapts financial statements and...
-
Do public and private companies follow the same set of accounting rules? Explain.
-
A file contains 2 million bytes. How long does it take to download this file using a 56-Kbps channel? 1-Mbps channel?
-
We measure the performance of a telephone line (4 KHz of bandwidth). When the signal is 10 V, the noise is 5 mV. What is the maximum data rate supported by this telephone line?
-
A line has a signal-to-noise ratio of 1000 and a bandwidth of 4000 KHz. What is the maximum data rate supported by this line?
-
14. a) Explain what is meant by the Fisher Separation Theorem (FST). Graphically demonstrate FST for the case where an individual ends up lending in financial markets. (40 marks) b) Graphically...
-
Suppose that a bank trading desk has just entered into a hypothetical 2x5 "squared" FRA where the bank pays a fixed rate and receives LIBOR X LIBOR in return. For example, if LIBOR=5%, the bank would...
-
Asset Amount ($b) Risk Weight Risk Weighted Assets ES funds 4.5 0% T-notes and CG bonds 5.5 0% Home loans (LVR < 80%) 190 75% Home loans (LVR >85%) 60 100% Business loans 150 100% Total 410 Calculate...

Study smarter with the SolutionInn App