Convert A into a binary number. What makes base 16 (hexadecimal) an attractive numbering system for representing
Question:
Convert A into a binary number. What makes base 16 (hexadecimal) an attractive numbering system for representing values in computers?
The following table also shows pairs of hexadecimal numbers.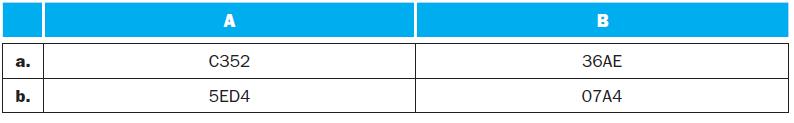
Transcribed Image Text:
a. b. A C352 5ED4 B 36AE 07A4
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 100% (QA)
To convert the given hexadecimal number A into a binary number you can convert each hexadecimal digi...View the full answer

Answered By

JAPHETH KOGEI
Hi there. I'm here to assist you to score the highest marks on your assignments and homework. My areas of specialisation are:
Auditing, Financial Accounting, Macroeconomics, Monetary-economics, Business-administration, Advanced-accounting, Corporate Finance, Professional-accounting-ethics, Corporate governance, Financial-risk-analysis, Financial-budgeting, Corporate-social-responsibility, Statistics, Business management, logic, Critical thinking,
So, I look forward to helping you solve your academic problem.
I enjoy teaching and tutoring university and high school students. During my free time, I also read books on motivation, leadership, comedy, emotional intelligence, critical thinking, nature, human nature, innovation, persuasion, performance, negotiations, goals, power, time management, wealth, debates, sales, and finance. Additionally, I am a panellist on an FM radio program on Sunday mornings where we discuss current affairs.
I travel three times a year either to the USA, Europe and around Africa.
As a university student in the USA, I enjoyed interacting with people from different cultures and ethnic groups. Together with friends, we travelled widely in the USA and in Europe (UK, France, Denmark, Germany, Turkey, etc).
So, I look forward to tutoring you. I believe that it will be exciting to meet them.
3.00+
2+ Reviews
10+ Question Solved
Related Book For 

Computer Organization And Design The Hardware Software Interface
ISBN: 9780123747501
4th Revised Edition
Authors: David A. Patterson, John L. Hennessy
Question Posted:
Students also viewed these Computer science questions
-
Convert A into a binary number. What makes base 8 (octal) an attractive numbering system for representing values in computers? The following table also shows pairs of octal numbers. a. b. A 7040 4365...
-
Convert 5ED4 into a binary number. What makes base 16 (hexadecimal) an attractive numbering system for representing values in computers?
-
What is the sum of A and B if they represent signed 16-bit hexadecimal numbers stored in sign-magnitude format? The result should be written in hexadecimal. Show your work. Hexadecimal (base 16) is...
-
In Problems 5994, solve each inequality. Express your answer using set notation or interval notation. Graph the solution set. 2x2 3 + x
-
In another short paragraph, describe the effect of adding bankruptcy costs to the MM model with taxes.
-
What is the principle of vicarious liability (respondeat superior)?
-
Leicht Transfer & Storage provides warehousing services and often purchases pallets from Pallet Central. The companies followed a standard practice for documenting these transactions in which Pallet...
-
Tami Tyler opened Tamis Creations, Inc., a small manufacturing company, at the beginning of the year. Getting the company through its first quarter of operations placed a considerable strain on Ms....
-
The threshold frequency v0 describes the smallest light frequency capable of ejecting electrons from a metal. Determine the minimum energy E0 of a photon capable of ejecting electrons from a metal...
-
Write an MIPS assembly language program to calculate the sum of A and B, assuming they are stored using the format described in 3.11.1. Now modify the program to calculate the sum assuming the format...
-
How many register read ports should the processor have to avoid any resource hazards due to register reads? This exercise explores how branch prediction affects performance of a deeply pipelined...
-
Cost per contact is high with the ___________ element of the promotional mix.
-
A closed economy has income of $1,000, government spending of $200, taxes of $150, and investment of $250. What is private saving? a. $100 b. $200 c. $300 d. $400
-
If the government wants to expand aggregate demand, it can ________ government purchases or ________ taxes. a. increase; increase b. increase; decrease c. decrease; increase d. decrease, decrease
-
If the business community becomes more optimistic about the profitability of capital, the ________ curve for loanable funds would shift, driving the equilibrium interest rate ________. a. supply; up...
-
Greta obtained an auto loan from Ridgeline Bank, but the bank did not give her a payment schedule and refused her attempts to make payments. In fact, Ridgeline told Greta that it had not given her a...
-
If the interest rate is zero, then $100 to be paid in 10 years has a present value that is a. less than $100. b. exactly $100. c. more than $100. d. indeterminate.
-
Splitland is a developing economy with two distinct regions. The northern region has great investment opportunities, but the people who live there need to consume all of their income to survive....
-
In Exercises discuss the continuity of each function. f(x) -3 1 x - 4 y 3 2 -1 -2 -3+ 3 X
-
Repeat the previous problem, considering the case in which ys children start with different heights. Previous problem Consider a deletion operation in an AVL tree that triggers a trinode...
-
NASA wants to link n stations spread over the country using communication channels. Each pair of stations has a different bandwidth available, which is known a priori. NASA wants to select n1...
-
Repeat Exercise R-14.28 for Figure 14.13 that illustrates the topological sorting algorithm. Repeat Exercise Describe the meaning of the graphical conventions used in Figure 14.9 illustrating a DFS...
-
Explain the benefits to using a layered model to describe network protocols and operations.
-
dont use chat gpt pls You are investigating if arrivals at a queue to use an ATM machine are well described by a Poisson distribution. 1. [3 marks] If you got to an ATM and there were already 5...
-
The main goal of any penetration test should be to find the current security baseline (I.E., where are things vulnerable and where are they not). After a final assessment report summary is delivered,...

Study smarter with the SolutionInn App