How many 16-byte cache lines are needed to store all 32-bit matrix elements being referenced? Locality is
Question:
How many 16-byte cache lines are needed to store all 32-bit matrix elements being referenced?
Locality is affected by both the reference order and data layout. The same computation can also be written below in Matlab, which differs from C by contiguously storing matrix elements within the same column.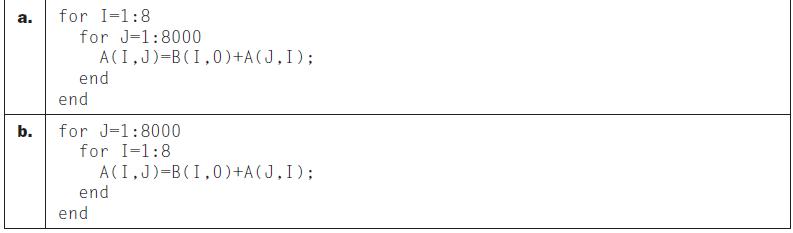
Transcribed Image Text:
a. b. for I-1:8 for J-1:8000 A(I,J)=B (1,0) +A(J, I); end end for J-1:8000 for I=1:8 A(I,J)=B (1,0) +A(J, I); end end
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 50% (6 reviews)
To determine the number of 16byte cache lines needed to store all 32bit matrix elements being referenced we need to consider the size of a 32bit eleme...View the full answer

Answered By

Mary Boke
As an online tutor with over seven years of experience and a PhD in Education, I have had the opportunity to work with a wide range of students from diverse backgrounds. My experience in education has allowed me to develop a deep understanding of how students learn and the various approaches that can be used to facilitate their learning. I believe in creating a positive and inclusive learning environment that encourages students to ask questions and engage with the material. I work closely with my students to understand their individual learning styles, strengths, and challenges to tailor my approach accordingly. I also place a strong emphasis on building strong relationships with my students, which fosters trust and creates a supportive learning environment. Overall, my goal as an online tutor is to help students achieve their academic goals and develop a lifelong love of learning. I believe that education is a transformative experience that has the power to change lives, and I am committed to helping my students realize their full potential.
5.00+
4+ Reviews
22+ Question Solved
Related Book For 

Computer Organization And Design The Hardware Software Interface
ISBN: 9780123747501
4th Revised Edition
Authors: David A. Patterson, John L. Hennessy
Question Posted:
Students also viewed these Computer science questions
-
In this exercise we look at memory locality properties of matrix computation. The following code is written in C, where elements within the same row are stored contiguously. Assume each word is a...
-
References to which variables exhibit spatial locality? Locality is affected by both the reference order and data layout. The same computation can also be written below in Matlab, which differs from...
-
References to which variables exhibit temporal locality? Locality is affected by both the reference order and data layout. The same computation can also be written below in Matlab, which differs from...
-
On January 5, Jones Ventures Inc. purchased 40% of the outstanding stock of Pilots Manufacturing Corp. The purchase was 20,000 shares at $10 per share. Jones received dividends from Pilots in the...
-
Cholla Company currently has 30,000 shares outstanding. Each share has a market value of $20. If the firm repurchases $150,000 worth of shares, then what will be the value of each share outstanding...
-
A certain gasoline engine has an efficiency of 30%; that is, it converts into useful work 30% of the heat generated by burning a fuel. If the engine consumes 0.80 L/h of a gasoline with a heating...
-
According to Rubenstein (1994: 3): For the first time in accountings sleepy history, there is a growing recognition among accountants and nonaccountants alike that accounting, the value-free,...
-
Managers are often concerned about the impact on reported profits of any actions recommended by the tax planning department. Explain why.
-
Your group owns a night club in downtown Toronto and for the 20th anniversary of your business your company decides to hire a famous Canadian singer to perform for two nights, during the weekend...
-
Repeat 4.24.4, but now your predictor should be able to eventually (after a warm-up period during which it can make wrong predictions) start perfectly predicting both this pattern and its opposite....
-
Calculate the CPI for the processor in the table using: 1) only a first level cache, 2) a second level direct-mapped cache, and 3) a second level eight way set associative cache. How do these numbers...
-
What is a parlay bet? a. A bookmaker makes a bet with another bookmaker. b. A bettor makes a bet on two or more teams which must win. c. A bettor makes a bet on two teams, one must win the other must...
-
Consider the following C++ code sequence void shift2 (int & A [10], int k)// k size of the array { A [0]; int sl A [1]; www for (int i = 0; i
-
First, review the Week 1 topics located in 1.1, 1.2, 1.3, and 1.4 and answer the following questions. You are a new business intelligence analyst for your organization in response to the marketing...
-
Let's solve the exponential equation 2e* = 30. (a) First, we isolate ex to get the equivalent equation (b) Next, we take In of each side to get the equivalent equation (c) Now we use a calculator to...
-
Total nonfarm payroll employment increased by 187,000 in August, and the unemployment rate rose to 3.8 percent, the U.S. Bureau of Labor Statistics reported today. Employment continued to trend up in...
-
For this week's discussion question, assume you are a business analyst for an ocean/rail shipping container manufacturer that sells products in over 70 countries. Obviously, the forecast for...
-
Consider each of these situations. Do you think the proposed sampling method is appropriate? Explain. a) We want to know if business leaders in the community support the development of an incubator...
-
Explain the buyers position in a typical negotiation for a business. Explain the sellers position. What tips would you offer a buyer about to begin negotiating the purchase of a business?
-
Point-of-sale terminals that use magnetic-stripe cards and PIN codes have a fatal flaw: a malicious merchant can modify his card reader to log all the information on the card and the PIN code in...
-
Is it possible to multicast a PGP message? What restrictions would apply?
-
Two users can establish a shared secret key using the Diffie-Hellman algorithm, even if they have never met, share no secrets, and have no certificates (a) Explain how this algorithm is susceptible...
-
One of the most essential things you can do as a speaker is to establish your credibility. In other words, it is important what makes you "qualified" to be giving your speech. Please watch this...
-
Effectiveness and efficiency are in a constant tug-of-war when it comes to process, organization, production, etc. Whether deciding how to organize your reporting structure, people flow, or...
-
Reflect on a leadership development program that you have been involved in. Give an overview of what kind of training it was and discuss whether or not it was a success. Was it a short workshop,...

Study smarter with the SolutionInn App