The following problems deal with translating from MIPS to C. Assume that the variables g, h, i,
Question:
The following problems deal with translating from MIPS to C. Assume that the variables g, h, i, and j are given and could be considered 32-bit integers as declared in a C program.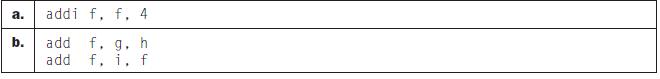
If the variables f, g, h, and i have values 1, 2, 3, and 4, respectively, what is the end value of f?
Transcribed Image Text:
a. b. addi f, f. 4 add f, g. h f. i. f add
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 75% (4 reviews)
To find the end value of f we need to translate the given MIPS instructions into their equivalent C ...View the full answer

Answered By

Sandhya Sharma
I hold M.Sc and M.Phil degrees in mathematics from CCS University, India and also have a MS degree in information management from Asian institute of technology, Bangkok, Thailand. I have worked at a international school in Bangkok as a IT teacher. Presently, I am working from home as a online Math/Statistics tutor. I have more than 10 years of online tutoring experience. My students have always excelled in their studies.
4.90+
119+ Reviews
214+ Question Solved
Related Book For 

Computer Organization And Design The Hardware Software Interface
ISBN: 9780123747501
4th Revised Edition
Authors: David A. Patterson, John L. Hennessy
Question Posted:
Students also viewed these Computer science questions
-
The following problems deal with translating from MIPS to C. Assume that the variables g, h, i, and j are given and could be considered 32-bit integers as declared in a C program. If the variables f,...
-
The following problems deal with translating from MIPS to C. Assume that the variables g, h, i, and j are given and could be considered 32-bit integers as declared in a C program. For the MIPS...
-
The following problems deal with translating from MIPS to C. Assume that the variables g, h, i, and j are given and could be considered 32-bit integers as declared in a C program. For the MIPS...
-
In Exercises 1114, graph each equation in a rectangular coordinate system. If two functions are indicated, graph both in the same system. Then use your graphs to identify each relations domain and...
-
Paladin Enterprises manufactures printing presses for small-town newspapers that are often short of cash. To accommodate these customers, Paladin offers the following payment terms. 1/3 on delivery...
-
a. An asset has a beta of 1.4. Given a market return of 15% and a risk-free rate of 3%, calculate the required rate of return for this asset. b. Due to recent geopolitical events, investors have...
-
Determine the torsional strain energy in the A-36 steel shaft. The shaft has a radius of \(40 \mathrm{~mm}\). 8 kNm 6 kNm 12 kNm 0.6 m 0.4 m 0.5 m
-
One position expressed in the financial literature is that firms set their dividends as a residual after using income to support new investment. a. Explain what a residual policy implies (assuming...
-
Analyze the challenges and best practices associated with kernel upgrades and patch management in production environments. How does the kernel community ensure backward compatibility and minimize...
-
The following three problems in this Exercise refer to a function f that calls another function func. The code for C function func is already compiled in another module using the MIPS calling...
-
For these problems, the table holds MIPS assembly code fragments. You will be asked to evaluate each of the code fragments, familiarizing you with the different MIPS branch instructions. Translate...
-
Find the Maclaurin series for f(x) using the definition of a Maclaurin series. [Assume that f has a power series expansion. Do not show that R n (x) 0.] Also find the associated radius of...
-
Explain how convergence differs from harmonization. In your opinion, what are the two most important arguments in favor of international convergence for US public companies? In your opinion, what are...
-
Assume the discount rate is 10%. An FI originates a pool of real estate loans worth $2 million with maturities of 5 years and paying interest rates of 10% APR per year. Calculate the yearly payments...
-
5. In an arithmetic sequence, the 5th term is 2 and the 9th term is -10. Show all work for each of the following: a) Determine the common difference of the sequence. b) Find the first term of the...
-
Consider a 10 year bond with face value $1000. Pays 6% coupon semi annual and has a yeild to maruryity of 7%. How much would the approximate percentagechange in the price of bond if interest rate in...
-
Discuss the following issues relating to business risk and financial risk. a. What is the difference between business risk and financial risk? Explain some of the factors that contribute to each....
-
Acetic acid is responsible for the sour taste of vinegar. It can be manufactured using the following reaction: Use tabulated values of bond energies (Table 13.6) to estimate DH for this reaction....
-
A company produces earbuds. The revenue from the sale of x units of these earbuds is R = 8x. The cost to produce x units of earbuds is C = 3x + 1500. In what interval will the company at least break...
-
Provide the type and hexadecimal representation of following instruction: sw $t1, 32($t2)
-
Provide the type, assembly language instruction, and binary representation of instruction described by the following MIPS fields: op = 0, rs = 3, rt = 2, rd = 3, shamt = 0, funct = 34
-
Provide the type, assembly language instruction, and binary representation of instruction described by the following MIPS fields: op = 0 x 23, rs = 1, rt = 2, const = 0 x 4
-
Trapdoors/backdoors is categorized as one of a malicious code. But sometimes, it is desirable in software development. Explain 'good' and 'bad' of trapdoors/backdoors. (2 marks) You are working as a...
-
Find the exact values of the trigonometric functions. The ordered pair is the terminal side of an angle in standard position. 1) (-1,-2) sin. cos. tan. csc. sec. cot. Find the exact values of the...
-
1. Enter the correct network address and subnet mask for the required number of hosts. You have a network address of 192.168.1.0 /24 You have 120 hosts on a network. What is the correct subnet mask...

Study smarter with the SolutionInn App