What is the new PC address after this instruction is executed? Highlight the path through which this
Question:
What is the new PC address after this instruction is executed? Highlight the path through which this value is determined.
In this exercise we examine in detail how an instruction is executed in a single-cycle datapath. Problems in this exercise refer to a clock cycle in which the processor fetches the following instruction word: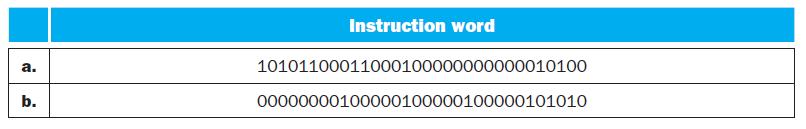
Transcribed Image Text:
a. b. Instruction word 10101100011000100000000000010100 00000000100000100000100000101010
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 100% (2 reviews)
In a singlecycle datapath the execution of an instruction involves several stages typical...View the full answer

Answered By

Ali Khawaja
my expertise are as follows: financial accounting : - journal entries - financial statements including balance sheet, profit & loss account, cash flow statement & statement of changes in equity -consolidated statement of financial position. -ratio analysis -depreciation methods -accounting concepts -understanding and application of all international financial reporting standards (ifrs) -international accounting standards (ias) -etc business analysis : -business strategy -strategic choices -business processes -e-business -e-marketing -project management -finance -hrm financial management : -project appraisal -capital budgeting -net present value (npv) -internal rate of return (irr) -net present value(npv) -payback period -strategic position -strategic choices -information technology -project management -finance -human resource management auditing: -internal audit -external audit -substantive procedures -analytic procedures -designing and assessment of internal controls -developing the flow charts & data flow diagrams -audit reports -engagement letter -materiality economics: -micro -macro -game theory -econometric -mathematical application in economics -empirical macroeconomics -international trade -international political economy -monetary theory and policy -public economics ,business law, and all regarding commerce
4.00+
1+ Reviews
10+ Question Solved
Related Book For 

Computer Organization And Design The Hardware Software Interface
ISBN: 9780123747501
4th Revised Edition
Authors: David A. Patterson, John L. Hennessy
Question Posted:
Students also viewed these Computer science questions
-
In this exercise we examine in detail how an instruction is executed in a single-cycle datapath. Problems in this exercise refer to a clock cycle in which the processor fetches the following...
-
In this exercise, we examine how pipelining affects the clock cycle time of the processor. Problems in this exercise assume that individual stages of the datapath have the following latencies: Also,...
-
In this exercise, we examine how resource hazards, control hazards, and Instruction Set Architecture (ISA) design can affect pipelined execution. Problems in this exercise refer to the following...
-
Suppose that in a wave of pessimism, housing prices fall by 10% across the entire economy. a. Has the stock of real assets of the economy changed? b. Are individuals less wealthy? c. Can you...
-
Elsee, Inc., has net sales of $13 million, and 75 percent of these are credit sales. Its cost of goods sold is 65 percent of annual sales. The firms cash conversion cycle is 41.3 days. The inventory...
-
Explain why each of the following integrals is improper. a. b. c. 1 0 tan x dx d. "4 4dx -3
-
Estimate the energy that a runner expends to overcome aerodynamic drag while running a complete marathon race. This expenditure of energy is equivalent to climbing a hill of what height? List all...
-
Sippy was thinking of buying Christichs house. He noticed watermarks on the ceiling, but the agent showing the house stated that the roof had been repaired and was in good condition. Sippy was not...
-
1. For each of the product strategies: First-to-market, Follow-the-leader, Me-too, and Application engineering, identify the characteristics of each and discuss how concurrent engineering fits or...
-
Assume that we already have a single-cycle design. How many bits in total do we need for pipeline registers to implement the pipelined design? This exercise explores some of the tradeoffs involved in...
-
Rearrange your code from 4.28.1 to achieve better performance on a 2-issue statically scheduled processor from Figure 4.69. Exercise 4.28.1 Translate this C code into MIPS instructions. Your...
-
Winterborn Manufacturing Co. completed the following transactions during 2016: Jan. 16 Declared a cash dividend on the 4%, $100 par noncumulative preferred stock (950 shares outstanding). Declared a...
-
Humber Bakery needs to decide how many units of its new Rexdough bread (nicknamed Rex) to bake at the start of each day.Because the bakery prides itself on being the maker of the freshest premium...
-
What are the five classification criteria that a lessee must consider to classify a non cancelable lease as a financing lease versus an operating lease. Why do you think these are important...
-
What type of Operating System would you use if you were asked to develop a system that processed 250 million credit card transactions each night? Why? 2. List two metrics, explain what they measure,...
-
Draw the modulated signals for the sample signal below? Signal ASK FSK
-
A firm sells three products. Product 1 : $ 6 1 sales price per unit; $ 4 4 variable cost per unit. Product 2 : $ 2 2 sales price per unit; $ 1 2 variable cost per unit. Product 3 : $ 1 0 7 sales...
-
In 150 words or fewer, explain the difference between horizontal and vertical analysis. Be sure to include in your answer how each might be used.
-
Pearson Education, a publisher of college textbooks, would like to know if students prefer traditional textbooks or digital textbooks. A random sample of students was asked their preference and the...
-
Modify, compile, and test the client program in Table 25.17 and the server program in Table 25.16 to simulate a local DNS client and server. The server has a short table made of two columns, domain...
-
Which of the following can be a source of data? a. A keyboard b. A monitor c. A socket
-
Write a method in Java to add a given prefix (as an integer) at the end of an IP address to create a string representing the CIDR notation (x.y.z.t/n).
-
"Vulnerabilities have the potential for loss. The potential loss is called Risk. Risk can be in many forms, like monetary due to loss of revenue, equipment, infrastructure, market factors".
-
Option A: Building a New Wing 1. One-Time Costs: Land & site preparation: $10 million (Year 0) Construction: $100 million ($50 million in Year 0 and $50 million in Year 1) Medical equipment: $25...
-
Now that the SEC has approved a Bitcoin ETF based on CME Bitcoin Futures symbol BTIO: Do you think it is more likely or less likely that they will approve an ETF in the near future based on the spot...

Study smarter with the SolutionInn App