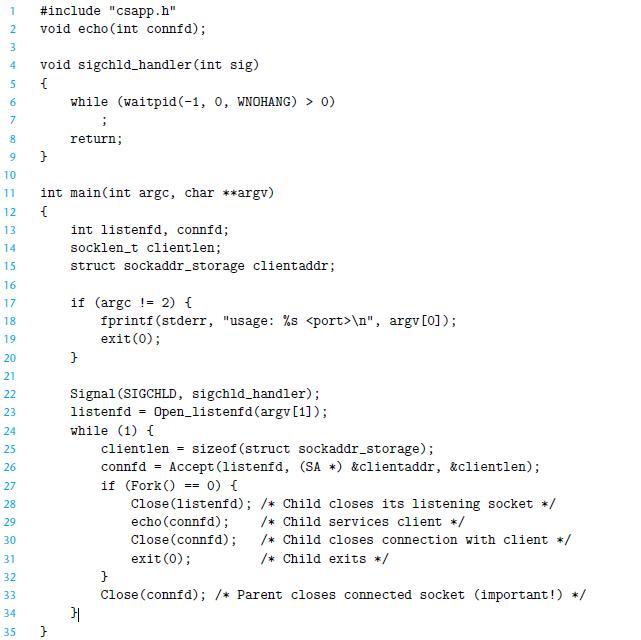
If we were to delete line 33 of Figure12.5, which closes the connected descriptor, the code would
Question:
If we were to delete line 33 of Figure12.5, which closes the connected descriptor, the code would still be correct, in the sense that there would be no memory leak. Why?
Figure12.5
Transcribed Image Text:
1
2
3
4
5
6
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
#include "csapp.h"
void echo(int connfd);
void sigchld_handler (int sig)
{
}
while (waitpid (-1, 0, WNOHANG) > 0)
;
return;
int main(int argc, char **argv)
{
}
int listenfd, connfd;
socklen_t clientlen;
struct sockaddr_storage clientaddr;
if (argc ! 2) {
fprintf(stderr, "usage: %s
1
2
3
4
5
6
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
#include "csapp.h"
void echo(int connfd);
void sigchld_handler (int sig)
{
}
while (waitpid (-1, 0, WNOHANG) > 0)
;
return;
int main(int argc, char **argv)
{
}
int listenfd, connfd;
socklen_t clientlen;
struct sockaddr_storage clientaddr;
if (argc ! 2) {
fprintf(stderr, "usage: %s \n", argv[0]);
exit(0);
}
Signal (SIGCHLD, sigchld_handler);
listenfd =
Open_listenfd (argv[1]);
while (1) {
clientlen sizeof (struct sockaddr_storage);
}|
connfd = Accept (listenfd, (SA) &clientaddr, &clientlen);
== 0) {
if (Fork ()
Close (listenfd); /* Child closes its listening socket */
echo (connfd);
/* Child services client */
Close (connfd);
/* Child closes connection with client */
/* Child exits */
exit(0);
==
}
Close (connfd); /* Parent closes connected socket (important!) */
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 33% (6 reviews)
When a process terminates for any rea...View the full answer

Answered By

Chiranjib Thakur
I have no tutoring experience yet, but I can share my skills and knowledge gained from my education and work experiences. I have been a CPA since 2012 with 6 years of work experience in internal auditing and 4 years of work experience in accounting at the supervisory level.
5.00+
1+ Reviews
10+ Question Solved
Related Book For 

Computer Systems A Programmers Perspective
ISBN: 9781292101767
3rd Global Edition
Authors: Randal E. Bryant, David R. O'Hallaron
Question Posted:
Students also viewed these Computer science questions
-
The Eastclock Corporation (EC) manufactures timing devices that are used in industrial settings. Recently, profits have fallen, and management is seeking your advice as an outside consultant on...
-
In the process-based server in Figure 12.5, we observed that there is no memory leak and the code remains correct even when line 33 is deleted. In the threads based server in Figure 12.14, are there...
-
If we were to look at two new plant locations, where would they be? (See JPMS.zip on the book Web site for the model and more information.) 2. If we were to look at two new plant locations, where...
-
Describe a procedure for solving a first-degree inequality.
-
The Haverly Company expects to finish the current year with the following financial results, and is developing its annual plan for next year. The following facts are available. FACTS Payables are...
-
Graces Art Shop, Inc., sells vintage books. The firms comparative income statement and balance sheet for the years 2018 and 2019 follow: INSTRUCTIONS 1. Prepare both a horizontal and a vertical...
-
The air removal from the surface condenser leads to (a) fall in condenser pressure (b) rise in condenser pressure (c) no change in condenser pressure (d) rise in condenser temperature
-
Turnaround LLC was formed several years ago. It incurred losses for several years, reducing many of its members bases in their interests to zero. However, the business has recently obtained some new...
-
Please review the code below and answer the following questions: 1) What type of attack is the code vulnerable to? 2) Where in the code snippet is the vulnerability? Please provide line number(s). 3)...
-
Consider three processes with the following starting and ending times: For each pair of processes, indicate whether they run concurrently (Y) or not (N): Process A BC Start time 1 2 4 End time 3 5...
-
In Linux systems, typing Ctrl+D indicates EOF on standard input. What happens if you type Ctrl+D to the program in Figure 12.6 while it is echoing each line of the client? Figure 12.6 1 #include...
-
Which of the following statements is NOT correct? a. Application logic changes may be made directly to the load module. b. As a practical matter, programs in their compiled state are secure and free...
-
What are Porters five forces?
-
Why do Amazon Alexa-based products improve over time? What scale- and time-derived advantage does Amazon leverage in realizing this improvement?
-
How does technology help in improving the firms fulfillment network? What is the role of data in these efforts? How do apps and websites help the firm roll out a UPS-rivaling fulfillment network in...
-
What is an instance? What is a virtual server?
-
What did the Splunk tool provide for the FreshDirect team?
-
Alex Corporation acquired a 40% interest in Calvin Company on June 1, 20X8, for $ 425,000. The management of Alex Corporation is now preparing the first set of financial statements since the...
-
Q:1 Take any product or service offered in Pakistan and apply all determinents of customer Perceived value ?
-
Write down the binary representation of the decimal number 63.25 assuming it was stored using the single precision IBM format (base 16, instead of base 2, with 7 bits of exponent).
-
Write down the binary bit pattern to represent -1.5625 10 -1 assuming a format similar to that employed by the DEC PDP-8 (the left most 12 bits are the exponent stored as a twos complement number,...
-
IEEE 754-2008 contains a half precision that is only 16 bits wide. The left most bit is still the sign bit, the exponent is 5 bits wide and has a bias of 15, and the mantissa is 10 bits long. A...
-
Shep Company's records show the following information for the current year: Total assets Total liabilities Beginning of year $ 57,200 End of year $ 89,000 $ 25,600 $ 38,600 Determine net income...
-
S Tiger Trade has the following cash transactions for the period. Accounts Cash received from sale of products to customers Cash received from the Bank for long-term loan Cash paid to purchase...
-
Suppose the 2's complement representation of x is (a 32-bit word is used): 11111111111111111111111111101001 What is the value of x? Give your answer in decimal representation. Explain why your method...

Study smarter with the SolutionInn App


