Consider a one-way authentication technique based on asymmetric encryption: a. Explain the protocol. b. What type of
Question:
Consider a one-way authentication technique based on asymmetric encryption: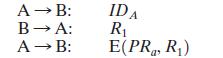
a. Explain the protocol.
b. What type of attack is this protocol susceptible to?
Transcribed Image Text:
A B: B A: A B: IDA R E(PR, R)
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 100% (QA)
a This is a means of authenticating A to B R 1 serves as a challenge and only ...View the full answer

Answered By

PALASH JHANWAR
I am a Chartered Accountant with AIR 45 in CA - IPCC. I am a Merit Holder ( B.Com ). The following is my educational details.
PLEASE ACCESS MY RESUME FROM THE FOLLOWING LINK: https://drive.google.com/file/d/1hYR1uch-ff6MRC_cDB07K6VqY9kQ3SFL/view?usp=sharing
3.80+
3+ Reviews
10+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
Consider a one-way authentication technique based on asymmetric encryption: a. Explain the protocol. b. What type of attack is this protocol susceptible to? A B: B A: A B: IDA E(PUa, R) R
-
1. Describe each of the following four kinds of access control mechanisms in terms of (a) ease of determining authorized access during execution, (b) ease of adding access for a new subject, (c) ease...
-
1- Describe each of the following four kinds of access control mechanisms in terms of a- Ease of determining authorized access during execution, b- Ease of adding access for a new subject, c- Ease of...
-
What is the square root of 3 to the square root of 2 power times the square root of 3 to the negative square root of 2 power?
-
To refresh air in a room, a counter flow heat exchanger, is mounted in the wall, drawing in outside air at 0.5C, 80% relative humidity and pushing out room air, 40C, 50% relative...
-
Fill in the blank with an appropriate word, phrase, or symbols(s). An illustration of all the points whose coordinates satisfy an equation is called a(n) ________ .
-
Consider the following cash flow profile, and assume MARR is 10 percent/year. a. What does Descartes' rule of signs tell us about the IRR(s) of this project? b. What does Norstrom's criterion tell us...
-
Nayak Company has recorded the following items in its financial records. Cash in bank ............ $ 41,000 Cash in plant expansion fund ...... 100,000 Cash on hand ............ 8,000 Highly liquid...
-
Two blocks are fastened to the ceiling of an elevator as in Figure. The elevator accelerates upward at 2.00 m/s. Find the tension in each rope. T 10.0 kg T 10.0 kg
-
In Kerberos, when Bob receives a Ticket from Alice, how does he know it is genuine?
-
In addition to providing a standard for public-key certificate formats, X.509 specifies an authentication protocol.The original version of X.509 contains a security flaw.The essence of the protocol...
-
In Fig. 6-10(a) let T = 1 s and call the waveform s 1 (t). Express s 1 (t) and its first two derivatives ds 1 /dt and d 2 s 1 dt 2 , using step and impulse functions. ST (1) T
-
Based on the above calculations, your estimated 3 month expenses will be $4,200. If this is more than the total amount that Welcome Corps requires for your selected family size, $7,275, what is your...
-
After this project, you get hired as the CEO of Advancement Corporation. Provide the next project manager with a written report, including the following: Document the activities and accomplishments...
-
What would you do to assess which of the two companies is most successful? 1) Compare companies' overall performance to their peers 2) Check online to see what the analysts say 3) Compare profits to...
-
As an operations manager, explore what changes you can bring to Supply Chain Analyze and express through a presentation how effective communications enabled powerful negotiations to succeed Explain...
-
A company believes it can sell 5,500,000 of its proposed new optical mouse at a price of $10.00 each. There will be $8,000,000 in fixed costs associated with the mouse. If the company desires to make...
-
At the beginning of the current season on April 1, the ledger of Wichita Pro Shop showed Cash $2,500; Merchandise Inventory $3,500; and Common Stock $6,000. The following transactions were completed...
-
Write an SQL statement to display all data on products having a QuantityOnHand greater than 0.
-
Consider the following NAMS instruction: cmp vleft, vright For signed integers, there are three status flags that are relevant. If vleft = vright, then ZF is set. If vleft > vright, ZF is unset (set...
-
Consider the following C program: /* a simple C program to average 3 integers */ main ( ) { int avg; int i1 = 20; int i2 = 13; int i3 = 82; avg = (i1 + i2 + i3)/3; } Write an NASM version of this...
-
Consider the following C code fragment: if (EAX == 0) EBX = 1; else EBX = 2; Write an equivalent NASM code fragment.
-
Assume that interest is calculated based on the debt outstanding at the beginning of the year. However, after you finish your forecast, can you please tell me what would happen to the amount of...
-
How might the stages of group development, recommendations on how to avoid getting stuck in the storming phase and how to create cohesion help to improve the performance of your team?
-
In developing a budget, what type of expenditures should be budgeted before other line items are added?

Study smarter with the SolutionInn App


