For each of the cybercrimes cited in Table 23.1, indicate whether it falls into the category of
Question:
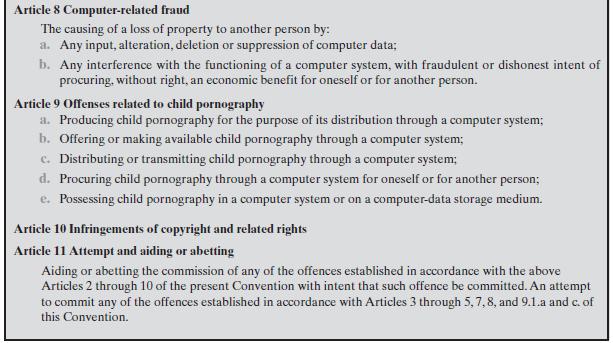
For each of the cybercrimes cited in Table 23.1, indicate whether it falls into the category of computer as target, computer as storage device, or computer as communications tool. In the first case, indicate whether the crime is primarily an attack on data integrity, system integrity, data confidentiality, privacy, or availability.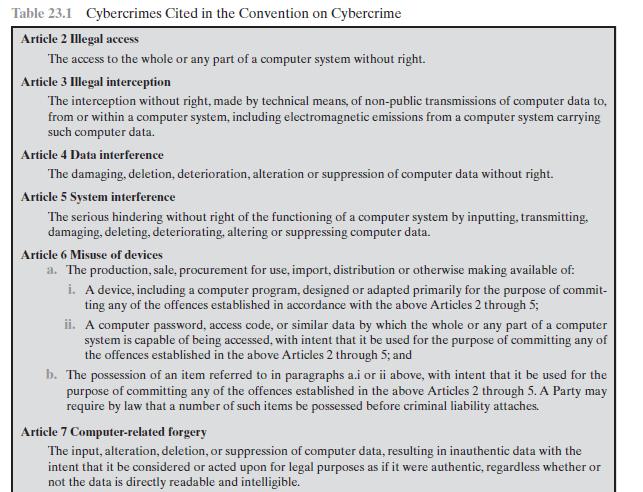
Transcribed Image Text:
Table 23.1 Cybercrimes Cited in the Convention on Cybercrime Article 2 Illegal access The access to the whole or any part of a computer system without right. Article 3 Illegal interception The interception without right, made by technical means, of non-public transmissions of computer data to, from or within a computer system, including electromagnetic emissions from a computer system carrying such computer data. Article 4 Data interference The damaging, deletion, deterioration, alteration or suppression of computer data without right. Article 5 System interference The serious hindering without right of the functioning of a computer system by inputting, transmitting, damaging, deleting, deteriorating, altering or suppressing computer data. Article 6 Misuse of devices a. The production, sale, procurement for use, import, distribution or otherwise making available of: i. A device, including a computer program, designed or adapted primarily for the purpose of commit- ting any of the offences established in accordance with the above Articles 2 through 5; ii. A computer password, access code, or similar data by which the whole or any part of a computer system is capable of being accessed, with intent that it be used for the purpose of committing any of the offences established in the above Articles 2 through 5; and b. The possession of an item referred to in paragraphs a.i or ii above, with intent that it be used for the purpose of committing any of the offences established in the above Articles 2 through 5. A Party may require by law that a number of such items be possessed before criminal liability attaches. Article 7 Computer-related forgery The input, alteration, deletion, or suppression of computer data, resulting in inauthentic data with the intent that it be considered or acted upon for legal purposes as if it were authentic, regardless whether or not the data is directly readable and intelligible.
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 100% (3 reviews)
Article 2 Illegal access This is a general threat the could fall into any of the t...View the full answer

Answered By

Felix Onchweri
I have enough knowledge to handle different assignments and projects in the computing world. Besides, I can handle essays in different fields such as business and history. I can also handle both short and long research issues as per the requirements of the client. I believe in early delivery of orders so that the client has enough time to go through the work before submitting it. Am indeed the best option that any client that can think about.
4.50+
5+ Reviews
19+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
List three specific parts of the Case Guide, Objectives and Strategy Section (See below) that you had the most difficulty understanding. Describe your current understanding of these parts. Provide...
-
1. How strong are the competitive forces confronting J. Crew in the market for specialty retail? Do a [Michael Porter] five-forces analysis to support your answer. (see chapter 3 in the textfor...
-
"I'm not sure we should lay out $300,000 for that automated welding machine," said Jim Alder, president of the Superior Equipment Company. "That's a lot of money, and it would cost us $84,000 for...
-
During one week, four production employees of Martinez Manufacturing Company worked the hours shown below. All these employees receive overtime pay at one and one-half times their regular hourly rate...
-
Liquid propane is burned with dry air. A volumetric analysis of the products of combustion yields the following volume percent composition on a dry basis: 8.6% CO2, 0.6% CO, 7.2% O2 and 83.6% N2....
-
Leo owned a one-story, one-family dwelling in a single-family residential zoning district in Detroit. He attempted to sell the house with its adjoining lot for $38,500. Houses in the neighborhood...
-
Which account does a merchandiser use that a service company does not use? a. Cost of goods sold b. Inventory C. Sales revenue d. All of the above
-
NPV and AARR, goal-congruence issues. Nate Stately, a manager of the Plate Division for the Great Slate Manufacturing Company, has the opportunity to expand the division by investing in additional...
-
In a competitive market, the demand is, QD = 476 - 1.2P. The supply of beef is Qs-142 +3.2P, if P > 142/3.2. Without any price controls, what is the equilibrium price? Without any price controls,...
-
Repeat Problem 23.1 for Table 23.2. Table 23.2 CERT 2006 E-Crime Watch Survey Results Theft of intellectual property Theft of other (proprietary) info including customer records, financial records,...
-
What functions can a professional code of conduct serve to fulfill?
-
For the data in Exercise 17.45, and using total nonrenewable energy production as the dependent variable, perform conventional multiple regression and stepwise regression analyses on the data, then...
-
Chrystal borrowed $1,000,000 from MQ Bank for one year at simple interest rate of 6.4% p.a. Unfortunately, she misread the documentation for the loan, and has misunderstood the interest charge. In...
-
What are the implications of technological advancements, such as social media and digital surveillance, on the identification and control of deviant behavior ?
-
The data shown were obtained from the financial records of Italian Exports, Inc., for March: Estimated Sales, $560,000, Sales 567,923, Purchases 294,823, Ending Inventory of next month's sales 10%,...
-
Provide ? differintial ? equation ? or ? the equation of motion ? of the ? below system with ? specific steps , , ? if you can make ? it ? more specific with free ? body ? diagram . . ? take ?...
-
According to Chavravety (2020), often, academically strong students lose confidence in their abilities and past achievements because of the pressure associated with doctoral education and...
-
Electronics Store acquired inventory on credit from TV Manufacturer, which retained and perfected a security interest in the TV sets until they were paid for. At some point thereafter Electronics...
-
Provide a draft/outline of legal research involving an indigenous Canadian woman charged with assault causing bodily harm under (Sec 267b) of the Criminal Code, where the crown wants a 12-month jail...
-
An example of a host-based intrusion detection tool is the tripwire program. This is a file integrity checking tool that scans files and directories on the system on a regular basis and notifies the...
-
Test the vulnerability of a machine at the following site: grc.com/default.htm. Follow the ShieldsUP! link for a series of free tests listed midway down the page.
-
The tiny fragment attack is a form of firewall attack. The intruder uses the IP fragmentation option to create extremely small fragments and force the TCP header information into a separate packet...
-
The first production department of Stone Incorporated reports the following for April. Direct Materials Units Beginning work in process inventory 73,000 Percent Complete 75% Conversion Percent...
-
Mauro Products distributes a single product, a woven basket whose selling price is $25 per unit and whose variable expense is $21 per unit. The company's monthly fixed expense is $4,000. Required: 1....
-
Using the rules for adding capacitors in series and parallel, compare the measurements of the individual capacitors to the capacitors in series and in parallel for both methods (for the time constant...

Study smarter with the SolutionInn App


