List ways in which secret keys can be distributed to two communicating parties. (2) IDA, E(Ka, Na),
Question:
List ways in which secret keys can be distributed to two communicating parties.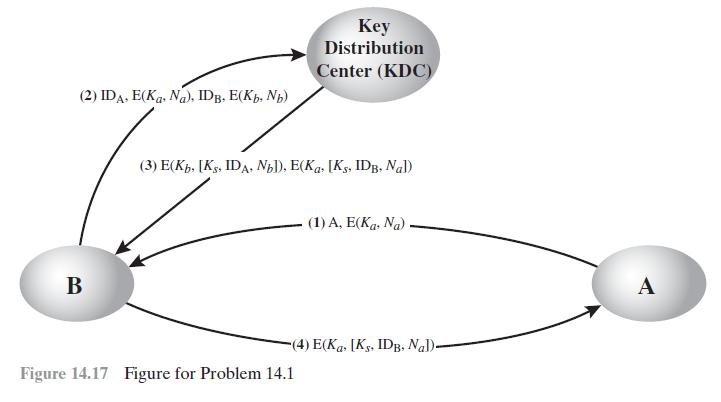
Transcribed Image Text:
(2) IDA, E(Ka, Na), IDB, E(Kb, N) B Key Distribution Center (KDC) (3) E(Kb. [KS, IDA, Nb]), E(Kas [KS, IDB, Nal) Figure 14.17 Figure for Problem 14.1 (1) A, E(Ka, Na) (4) E(Kas [Ks. IDB, Nal)- A
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 100% (QA)
For two parties A and B key distribution can be achieved in a number of ways as follows 1 A ...View the full answer

Answered By

David Ngaruiya
i am a smart worker who concentrates on the content according to my clients' specifications and requirements.
4.50+
7+ Reviews
19+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
Answer the following questions QUESTION 1. 1. List ways in which secret keys can be distributed to two communicating parties. 2. What is the difference between a session key and a master key? 3. What...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
The Crazy Eddie fraud may appear smaller and gentler than the massive billion-dollar frauds exposed in recent times, such as Bernie Madoffs Ponzi scheme, frauds in the subprime mortgage market, the...
-
Implement the queue data structure using arrays of size 10 with the following functions Enqueue () - add {2,3,4,5,6,7,8} to the queue Dequeue() - remove 2 elements isFull() - check if the queue is...
-
A steady flow of 0.01 k mol/s of 50% carbon dioxide and 50% water at 1200K and 200 kPa is used in a heat exchanger where 300 kW is extracted from the flow. Find the flow exit temperature and the rate...
-
The minimum speed for vehicles on a highway is 40 mph, and the maximum speed is 55 mph. If Philip has been driving nonstop along the highway for 4 hr, what range in miles could he have legally...
-
Describe the six categories of early warning signs of potential fraud.
-
This is the trial balance of Solis Company on September 30. The October transactions were as follows. Oct.5.Received $1,300 in cash from customers for accounts receivable due. 10 Billed customers for...
-
What are some practical advantages to using a star schema data model over a relational model in healthcare?
-
What is the difference between a session key and a master key?
-
An early proposal for a digital signature scheme using symmetric encryption is based on the following. To sign an \(n\)-bit message, the sender randomly generates in advance \(2 n\) 56-bit...
-
Discuss brand equity and brand value. How do marketers use these concepts to build powerful brands?
-
Some analysts believe that the term structure of interest rates is determined by the behavior of various types of financial institutions. This theory is called the expectations hypothesis. ( market )...
-
Problem 1 You are going to buy a car. The asking price is $ 2 8 , 8 0 0 , you put $ 2 , 2 0 0 down, and your trade - in is worth $ 1 , 7 0 0 . The balance you finance with a 6 % APR, 4 8 - month...
-
During the month of March 2022 the company John Services, Ltd. realized the following transactions March 1, Paid a 12 month insurance policy for $36,000 March 2: Paid the employee $44,000 for their...
-
Q 1 . Prepare a project on Growth of Derivatives Market in India: A Detailed Study including both Equity and Currency Derivatives? It should be minimum 1 0 pages and max 1 5 pages.
-
One major airlines consolidation history that is currently operating today
-
A credit sale is made on July 10 for $900, terms 2/10, n/30. On July 12, the purchaser returns $100 of goods for credit. Give the journal entry on July 19 to record the receipt of the balance due...
-
Economic feasibility is an important guideline in designing cost accounting systems. Do you agree? Explain.
-
What are the motivations for preemptive and nonpreemptive process migration?
-
How is the process address space handled during process migration?
-
Discuss some of the reasons for implementing process migration.
-
Connect the principles of electricity, magnetism, and light to modern applications of physics. Identify the classical physics principles including identification of a strong majority of elements with...
-
Discuss at least three ways a speaker can manage anxiety and nervousness before beginning a presentation.
-
Compromisers approach conflict with the goal of compromise. They tend to think about what they are willing to give up and what they are willing to hold on to, and try to gear communication to focus...

Study smarter with the SolutionInn App


