Use double hashing to reimplement the hash table from Figure 11.5. FIGURE 11.5 Implementation of the Table
Question:
Use double hashing to reimplement the hash table from Figure 11.5.
![FIGURE 11.5 Implementation of the Table Class Implementation // FILE: Table.java from the package edu.colorado.collections // Documentation is available starting on page 584 or from the Table link at // http://www.cs.colorado.edu/~main/docs/. package edu.colorado.collections; public class Table { private int manyItems; private Object[ ] keys; private Object[ ] data; private boolean[](https://dsd5zvtm8ll6.cloudfront.net/si.question.images/images/question_images/1605/8/5/5/5505fb7693e5eeed1605855548802.jpg)
Transcribed Image Text:
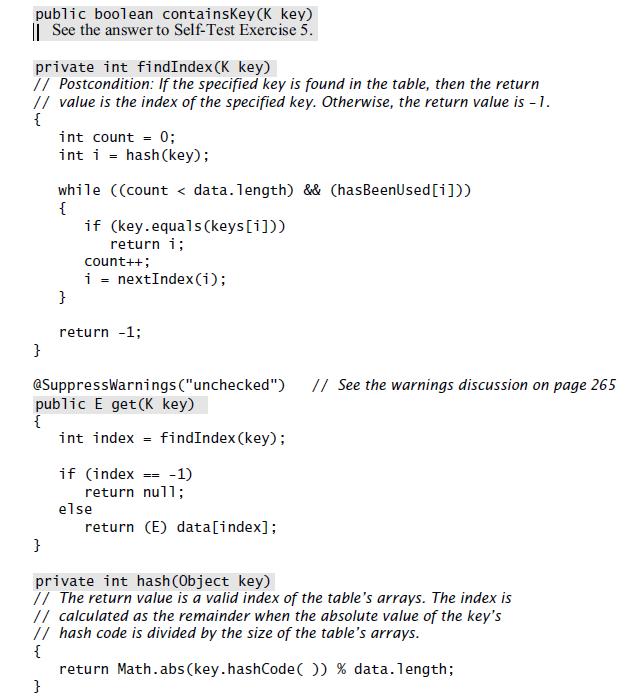
FIGURE 11.5 Implementation of the Table Class Implementation // FILE: Table.java from the package edu.colorado.collections // Documentation is available starting on page 584 or from the Table link at // http://www.cs.colorado.edu/~main/docs/. package edu.colorado.collections; public class Table
FIGURE 11.5 Implementation of the Table Class Implementation // FILE: Table.java from the package edu.colorado.collections // Documentation is available starting on page 584 or from the Table link at // http://www.cs.colorado.edu/~main/docs/. package edu.colorado.collections; public class Table { private int manyItems; private Object[ ] keys; private Object[ ] data; private boolean[ ] hasBeenUsed; public Table(int capacity) { if (capacity <= 0) throw new IllegalArgumentException ("Capacity is negative."); keys = new Object[capacity]; data = new Object[capacity]; hasBeenUsed new boolean [capacity]; }
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 50% (8 reviews)
Double hashing implementation of the hash table public class HashTable private int size private int ...View the full answer

Answered By

Beerendra Kumar Seela
An innovative and knowledgeable professional having years of experience as a Tutor.
Proficient in developing new lessons and activities to expand learning opportunities.
Extensive participation on committees and extra-curricular activities.
Excellent knowledge of the subject and also has great practical knowledge.
Proficient in giving conceptual knowledge.
0.00
0 Reviews
10+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
In our open-address hash tables, we have used linear probing or double hashing. Another probing method, which avoids some clustering, is called quadratic probing. The simplest version of quadratic...
-
Hash 8 randomly generated int values (in the range [ 099] inclusive). The random number generator is initially seeded to value 97. Each generated value is stored in a hash table size 11. The first...
-
Suppose that we use double hashing to resolve collisionsthat is, we use the hash function h(k, i) = (h 1 (k) + ih 2 (k)) mod m. Show that if m and h 2 (k) have greatest common divisor d 1 for some...
-
1. Underline the word at right that best describes the client's: 2. Discuss appropriate client objectives: A. Risk B. Return Case Facts Type of mvestorInstututional; endowment Purpose Asset base...
-
Identify the class width, class midpoints, and class boundaries for the given frequency table. Mass (kg) | Frequency 0.0-4.9 5.0-9.9 10.0-14.9 15.0-19.9 20.0-24.9 60 58 61 62 59
-
Journalize the following transaction in correct form: 201X Apr. 1 Sold merchandise on account, $1,230. The merchandise cost $680.
-
Derive the third of Equation 2.40 for the off-axis shear modulus, \(G_{x y}\). 2V12 E-[1 + (1-2)+1] Ex = Ey E E 1 2V12 + 1 1 G12 E2 1 E2 2V12 - E 2G12 1 1 sc E E1 E2 E2 G12 Gxy = 1 G12 Vxy = Ex ($4...
-
Emily Stansbury is a licensed dentist. During the first month of the operation of her business, the following events and transactions occurred. April 1 Invested 20,000 cash in her business. 1 Hired a...
-
How would you help employees build cultural intelligence in your fictional organization? Name and explain two specific actions you would take to help employees build cultural intelligence. Explain...
-
From the information below please calculate the the avoided tax effect on the sale of a Noise cancelling device using the formula Avoided Tax effect: -[(WDV Salvage Value) x tc] where tc is 30% 4....
-
For this project, you must first implement the Polynomial class from the Chapter 3 Programming Project 8 on page 170. Add a new method to the class with four parameters: a polynomial f and three...
-
Rewrite one of your hash tables so that it has additional methods to provide statistics. You should include methods to calculate the load factor, the average number of items examined during a...
-
There is no doubt that Johnson won the election, because an exit poll showed that she received 54% of the vote and the margin of error is only 3 percentage points. Decide whether the statement makes...
-
Given the following function: 1. Is there a constraint on the values that can be passed as a parameter for this function to answer the Smaller-Caller Question? 2. Is Func(7) a good call? If so, what...
-
Name three ways that classes can relate to each other.
-
The article "Characterization of Effects of Thermal Property of Aggregate on the Carbon Footprint of Asphalt Industries in China" (A. Jamshidi, K. Kkurumisawa, et al., Journal of Traffic and...
-
Read the code segment and fill in blank #20. 1. NULL 2. True 3. false 4. listData 5. answer not shown 4 Class Unsorted Type { public: //all the prototypes go here. private: int length; Node Type*...
-
1. The details of a private member can be seen by the user of a class. (True or False?) 2. The details of a private member may be accessed by a client program. (True or False?)
-
During 2016, Susan, age 49, incurred and paid the following expenses for Beth (her daughter), Ed (her father), and herself: Surgery for Beth...
-
Big Jim Company sponsored a picnic for employees and purchased a propane grill equipped with a standard-sized propane tank for the picnic. To make sure there was enough propane for all the cooking...
-
For a high-performance system such as a B-tree index for a database, the page size is determined mainly by the data size and disk performance. Assume that on average a B-tree index page is 70% full...
-
As described in Section 5.7, virtual memory uses a page table to track the mapping of virtual addresses to physical addresses. This exercise shows how this table must be updated as addresses are...
-
In this exercise, we will examine space/time optimizations for page tables. The following list provides parameters of a virtual memory system. 1. For a single-level page table, how many page table...
-
On Monday, April 5, 2010, just before 3:00 in the afternoon, miners at Massey Energy Corporation's Upper Big Branch coal mine in southern West Virginia were in the process of a routine shift change....
-
Ethics in Human Resource Practices HR teams will play vital roles in organizations to ensure ethical behavior and compliance. To be effective, they must first place an emphasis on ethical behavior...
-
Why do managers struggle with ethics when it comes to making strategic management decisions for their organization?

Study smarter with the SolutionInn App

