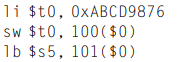
Explain how the following program can be used to determine whether a computer is big-endian or little-endian:?
Question:
Explain how the following program can be used to determine whether a computer is big-endian or little-endian:?
Transcribed Image Text:
li $t0, 0XABCD9876 Sw $t0, 100( $0) lb $s5, 101($0)
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 63% (19 reviews)
In bigendian format the bytes are numbered from 100 to 103 from left to right In l...View the full answer

Answered By

Muhammad Umair
I have done job as Embedded System Engineer for just four months but after it i have decided to open my own lab and to work on projects that i can launch my own product in market. I work on different softwares like Proteus, Mikroc to program Embedded Systems. My basic work is on Embedded Systems. I have skills in Autocad, Proteus, C++, C programming and i love to share these skills to other to enhance my knowledge too.
3.50+
1+ Reviews
10+ Question Solved
Related Book For 

Digital Design and Computer Architecture
ISBN: 978-0123944245
2nd edition
Authors: David Harris, Sarah Harris
Question Posted:
Students also viewed these Computer science questions
-
The Turing test is a hypothetical test to determine whether a computer system has reached the level of artificial intelligence. If the computer can fool a person into thinking it is another person,...
-
How can leverage analysis be used to determine whether a plant should be modified or not?
-
Explain how Theorem 2 can be used to determine whether a graph is connected
-
Design an application that declares two CheckingAccount objects and sets and displays their values. Write the pseudocode that defines the class from the class diagram & previous information...
-
Consider the research described in Exercise 11.4.6 in which 10 women in an aerobic exercise class, 10 women in a modern dance class, and a control group of 9 women were studied. One measurement made...
-
For the system presented in Example 21. 3 you are asked to appraise the effects of adding a second pump and impeller set identical to the current pump in the system. a. Prepare a performance diagram,...
-
In spring 1989, Michael Jordan and the Chicago Bulls were in Indianapolis, Indiana, to play against the Indiana Pacers. At the same time, Karla Knafel was singing with a band at a hotel in...
-
Steinborn Homes manufactures prefabricated chalets in Colorado. The company uses a perpetual inventory system and a job cost system in which each chalet is a job. The following events occurred during...
-
The accompanying tree diagram represents an experiment consisting of two trials. Use the diagram to find the given probability. P(Cn E) E 0.8 A 0.2 0.2 EC 0.5 E 0.5 B 0.5 EE EC 0.3 0.3 C 0.7 E
-
Table 1 shows Apple's online orders for the last week. When shoppers place an online order, several "recommended products" (upsells) are shown as at checkout an attempt to upsell See table 2 in cell...
-
Repeat Exercise 6.3 for memory storage of a 32-bit word stored at memory word 15 in a byte-addressable memory.? Data from problem 3 Consider memory storage of a 32-bit word stored at memory word 42...
-
Write the following strings using ASCII encoding. Write your final answers in hexadecimal. (a) SOS (b) Cool! (c) (your own name)
-
The Farr Quality Bathroom Tile Company has developed the following standards for one of its products: The company produced 1,200 units and sold all of the units at the budgeted sales price of $85....
-
NORMAL CRASH ACTIVITY TIME TIME NORMAL COST ($) A 3 2 1,000 Bowman Builders manufactures steel storage sheds for commercial use. Joe Bowman, president of Bowman Builders, is contemplating producing...
-
) Write a Java code for a method "makeMyList" which creates a singly linked list for PS) For example: makeMyList (3) represents a SLL contains F(3), F(2), F(1) and F(0), so it will return 2 10 You...
-
Sara focuses on helping her acquisition team do things the right way and to follow policies and procedures. At times, Sara must enforce team rules to make sure everyone meets their deliverable...
-
The goal of the Project is to - practice reading UML class diagram and working with interface - practice how to manage and provide sufficient operations on a doubly-linked circular list, for example,...
-
In this problem you will construct a "global leverage" factor. Assume you believe that history will repeat itself, and "expected" will be similar to historical averages. "Leverage" is computed as...
-
Glorietta Trust is an irrevocable discretionary trust that Grant Glorietta funded in 1999. The discretionary income beneficiary for life is Grant's son, Gordon Glorietta (single). Gordon is a partner...
-
a. What is meant by the term tax haven? b. What are the desired characteristics for a country if it expects to be used as a tax haven? c. What are the advantages leading an MNE to use a tax haven...
-
Why are acknowledgments used in 802.11 but not in wired Ethernet.
-
Suppose an 802.11 b station is configured to always reserve the channel with the RTS/CTS sequence. Suppose this station suddenly wants to transmit 1,000 bytes of data, and all other stations are idle...
-
True or false; Before an 802.11 station transmits a data frame, it must first send an RTS frame and receive a corresponding CTS frame.
-
Mr. and Mrs smith plan to open an RESP sinking fund for their child. They figure they need to have $121,000 till their son is 18 years old. if their sinking fund has a semiannual interest rate of...
-
Solve the equation. 180x3 +144x2-5x-4=0
-
2 0 1. a. Given A = compute the following, 4 1 i. A b. ii. A-3 iii. A 2A+I - If a polynomial p(x) can be factored as a product of two lower degree polynomials p1(x) and p2(x) as p(x) = P1(x)p2(x)...

Study smarter with the SolutionInn App