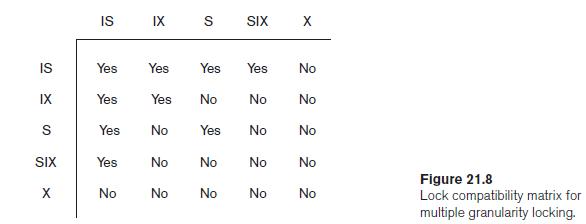
The compatibility matrix in Figure 21.8 shows that IS and IX locks are compatible. Explain why this
Question:
The compatibility matrix in Figure 21.8 shows that IS and IX locks are compatible. Explain why this is valid.
Transcribed Image Text:
IS IX S SIX IS Yes Yes Yes Yes No IX Yes Yes No No No S Yes No Yes No No SIX Yes No No No No Figure 21.8 Lock compatibility matrix for multiple granularity locking. X No No No No No
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 66% (12 reviews)
The compatibility matrix in Figure 218 illustrates the compatibility of various types of locks in a ...View the full answer

Answered By

Jackson Odari
Organized and reliable tutor recognized for excellence in developing rapport with students and establishing comfortable working environment with students and in small groups. Also have had a three year experience at the Corporate and Investment Banking sector in one of the top banks in Kenya.
0.00
0 Reviews
10+ Question Solved
Related Book For 

Fundamentals Of Database Systems
ISBN: 9780133970777
7th Edition
Authors: Ramez Elmasri, Shamkant Navathe
Question Posted:
Students also viewed these Computer science questions
-
Figure shows a probability-impact (or risk mapping) matrix that is frequently used as part of the risk analysis prioritization process. Here, ordinal probability-of-occurrence and...
-
Figure 2 . 1 8 shows a network of water pipes with flows measured in liters per minute. (a) Set up and solve a system of linear equations to find the possible flows. (b) If the flow through AB is...
-
In the circuit if Figure P8.66, if Ix = 645A, find Vo. 4 W112 1:2 4 2 42 2 Figure P8.66
-
Determine the largest force P that can be exerted at the jaws of the punch without exceeding a stress of 16 ksi on section m-n of the frame.
-
What strategies can be used to change the following components of an attitude?
-
Cassandra Corporations comparative balance sheets are presented below. Additional information: 1. Net income was $18,300. Dividends declared and paid were $14,600. 2. Equipment which cost $10,000 and...
-
Consider all 40 observations on the delivery time data. Delete \(10 \%\) (4) of the observations at random. Fit a model to the remaining 36 observations, predict the four deleted values, and...
-
On January 4, 2013, Runyan Bakery paid $324 million for 10 million shares of Lavery Labeling Company common stock . The investment represents a 30% interest in the net assets of Lavery and gave...
-
What ethical considerations arise in collaborative endeavors involving sensitive data sharing and knowledge exchange, and what governance mechanisms should be implemented to safeguard privacy and...
-
An Alabama lumberyard has four jobs on order, as shown in the following table. Today is day 205 on the yards schedule. In what sequence would the jobs be ranked according to the following decision...
-
Discuss two multiversion techniques for concurrency control. What is a certify lock? What are the advantages and disadvantages of using certify locks?
-
What type of lock is needed for insert and delete operations?
-
In Exercises 19 through 24, determine the domain of the given function. h(s) = -4
-
Think about a team conflict you had in the past. Or, if youre working as part of a team now, discuss a conflict you had. Identify whether it was a task, relationship, or values conflict. How did you...
-
Choose two countries and compare their cultures at https://www.hofstede-insights.com/ product/compare-countries. What similarities and differences do you notice? What, if anything, surprises you?
-
Youre a candidate for a new job and ask to meet your prospective team. Youre glad you did because no one on the team is like you; you are the only ______________. (Fill in the blank.) What is this...
-
Use the process described in Exercises 8 and 9 to plan and role-play another situation. Imagine that a coworkers behavior falls into the obnoxious aggression category of radical candor. Earlier in...
-
With a small group, select a keyword that interests you. Search for the word in any search engine and analyze the results. When you follow pages that rank highly, note how they use the word, for...
-
Suppose the graph of an electrical network is a tree, as in Exercise 2.6.8. Show that if one of the nodes in the tree is grounded, the system is statically determinate.
-
For the following exercises, find the area of the triangle. Round to the nearest hundredth. 22 50 36
-
In Figure 11.9, we show the packet path as a horizontal line, but the frame path as a diagonal line. Can you explain the reason? Figure 11.9 Sending node Receiving node Network Network Data-link...
-
Assume PPP is in the established phase; show payload encapsulated in the frame.
-
In Figure 11.12, explain why we need a timer at the sending site, but none at the receiving site. Figure 11.12 Receiving node Network Sending node Network Data-link Data-link Packet Frame Legend...
-
You will modify the add method in the LinkedBag class. The add method is the only thing you should modify in LinkedBag. Add a second parameter to the method header that will be a boolean variable:...
-
Generate Random Decals is primitive please fix that as well As a license plate number, integers are to be used. Positive numbers add a car, negative numbers remove a car, zero stops the...
-
Describe the competitive positions in the drone industry and assess the opportunities for at least three positions in the industry.

Study smarter with the SolutionInn App