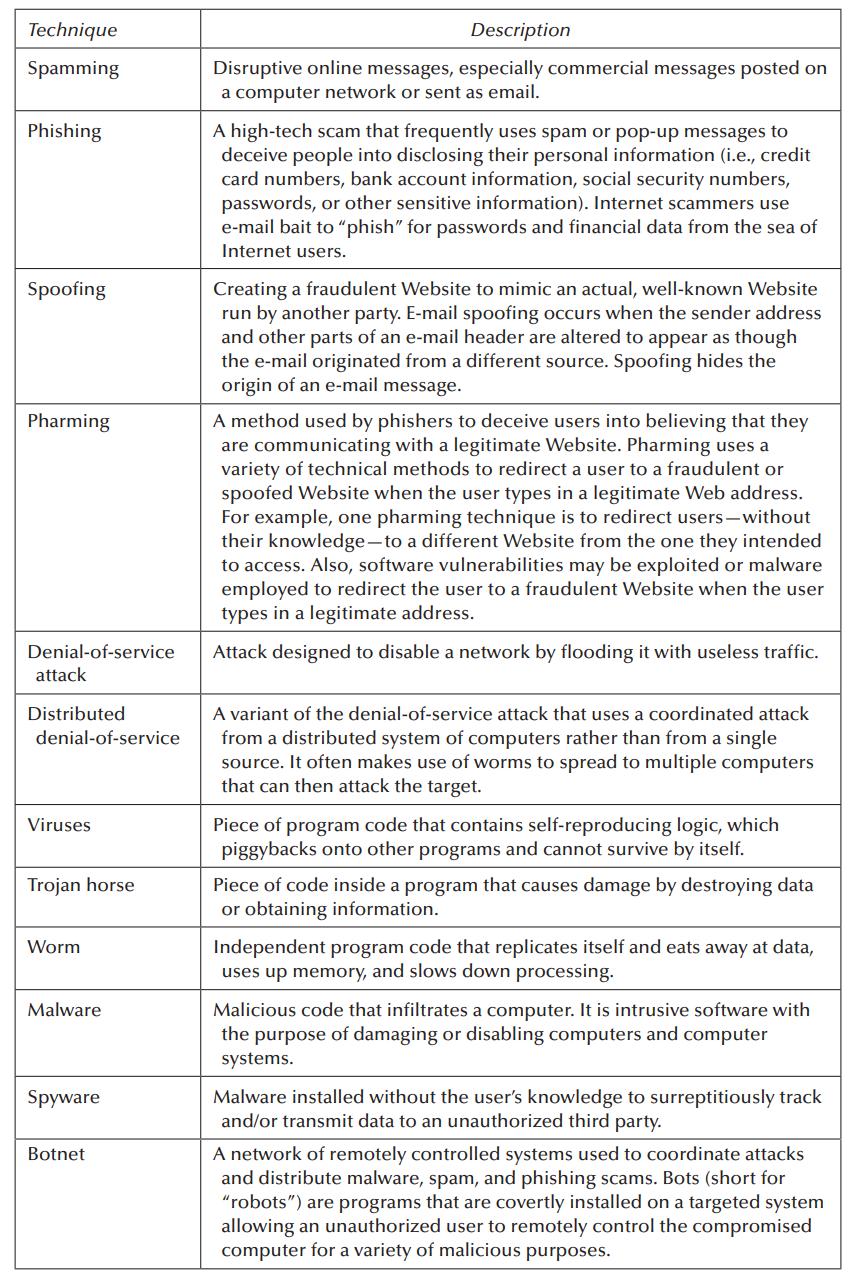
Exhibit 12.1 lists common techniques used to commit cybercrimes. For each of these techniques, research the Internet
Question:
Exhibit 12.1 lists common techniques used to commit cybercrimes. For each of these techniques, research the Internet and provide the names of one or two entities that have been impacted by such technique in the last 5–7 years. Briefly describe how the technique was used in the attack.
Exhibit 12.1
Transcribed Image Text:
Technique Spamming Phishing Spoofing Pharming Denial-of-service attack Distributed denial-of-service Viruses Trojan horse Worm Malware Spyware Botnet Description Disruptive online messages, especially commercial messages posted on a computer network or sent as email. A high-tech scam that frequently uses spam or pop-up messages to deceive people into disclosing their personal information (i.e., credit card numbers, bank account information, social security numbers, passwords, or other sensitive information). Internet scammers use e-mail bait to "phish" for passwords and financial data from the sea of Internet users. Creating a fraudulent Website to mimic an actual, well-known Website run by another party. E-mail spoofing occurs when the sender address and other parts of an e-mail header are altered to appear as though the e-mail originated from a different source. Spoofing hides the origin of an e-mail message. A method used by phishers to deceive users into believing that they are communicating with a legitimate Website. Pharming uses a variety of technical methods to redirect a user to a fraudulent or spoofed Website when the user types in a legitimate Web address. For example, one pharming technique is to redirect users - without their knowledge-to a different Website from the one they intended to access. Also, software vulnerabilities may be exploited or malware employed to redirect the user to a fraudulent Website when the user types in a legitimate address. Attack designed to disable a network by flooding it with useless traffic. A variant of the denial-of-service attack that uses a coordinated attack from a distributed system of computers rather than from a single source. It often makes use of worms to spread to multiple computers that can then attack the target. Piece of program code that contains self-reproducing logic, which piggybacks onto other programs and cannot survive by itself. Piece of code inside a program that causes damage by destroying data or obtaining information. Independent program code that replicates itself and eats away at data, uses up memory, and slows down processing. Malicious code that infiltrates a computer. It is intrusive software with the purpose of damaging or disabling computers and computer systems. Malware installed without the user's knowledge to surreptitiously track and/or transmit data to an unauthorized third party. A network of remotely controlled systems used to coordinate attacks and distribute malware, spam, and phishing scams. Bots (short for "robots") are programs that are covertly installed on a targeted system allowing an unauthorized user to remotely control the compromised computer for a variety of malicious purposes.
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 100% (2 reviews)

Answered By

Mugdha Sisodiya
My self Mugdha Sisodiya from Chhattisgarh India. I have completed my Bachelors degree in 2015 and My Master in Commerce degree in 2016. I am having expertise in Management, Cost and Finance Accounts. Further I have completed my Chartered Accountant and working as a Professional.
Since 2012 I am providing home tutions.
3.30+
2+ Reviews
10+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
On Tuesday, January 10, 2023, Stocks and Securities Limited notified the Financial Services Commission of the discovery of apparent fraud and of the immediate steps being taken. The letter...
-
The Crazy Eddie fraud may appear smaller and gentler than the massive billion-dollar frauds exposed in recent times, such as Bernie Madoffs Ponzi scheme, frauds in the subprime mortgage market, the...
-
THIRD AVENUE SOFTWARE HEALTH-CARE APP PROJECT This case is new for the ninth edition of Information Technology Project Management . The case provides an opportunity to apply agile and Scrum...
-
Economic crises tend to occur sporadically virtually every decade and in various countries ranging from Sweden to Argentina, from Russia to Korea, and from Japan to the United States. Each crisis is...
-
Describe the process of performing an external audit in an organization doing strategic planning for the first time.
-
Companies have the option of reporting some financial instruments at fair value and fair value reporting is required for some other financial instruments. IFRS 9 will retain mixed reporting. Discuss...
-
Why is it advisable to obtain a written confession from the subject of an investigation?
-
Becton Labs, Inc., produces various chemical compounds for industrial use. One compound, called Fludex, is prepared using an elaborate distilling process. The company has developed standard costs for...
-
Inflation Bonds (I Bonds) are safe investments issued by the U.S. Treasury to protect individual's money from loosing value due to inflation. Interest rates on I Bonds are adjusted regularly to keep...
-
What is the risk to organizations of not having a comprehensive business continuity plan in place in the event of an emergency?
-
List potential areas that backup policies, procedures, standards, and/or guidance should cover to ensure the availability of data significant to the operation of the organization.
-
What is the best-case runtime complexity of searching an Array?
-
uppose, instead, that in Question 5, above, the amounts were paid to specialists for appraisals. May Wee Works deduct such amounts currently on its tax return? a. No, because Wee Works capitalizes...
-
In Question 5, above, Wee Works assigned a large number of its highly paid staff to scout for future locations world-wide and paid them large bonuses when they were especially successful. These...
-
The National Association of Insurance Commissioners (NAIC) Risk Management and Own Risk and Solvency Assessment (ORSA) requires a Summary Report from individual insurers and insurance groups whose...
-
What information would you find when researching the labour market?
-
Identify and research a US public company in your pathway. It should be on the Fortune 500 list. Don't use a company that someone has already used. Access their most recent (less than 12 months)...
-
The dimensions of a rectangular building are 20 ft x 100 ft. The average outer wall temperature is 20F and the average inner wall temperature is 55F. Find the amount of heat conducted through the...
-
A horizontal annulus with inside and outside diameters of 8 and 10 cm, respectively, contains liquid water. The inside and outside surfaces are maintained at 40 and 20oC, respectively. Calculate the...
-
How should organizations develop a sound risk management program to determine the adequacy of their IT insurance coverage?
-
What are the key properties in a quality system?
-
List the control objectives related to process and quality and explain four of them.
-
Describe a company (that you are familiar with or that you research on the internet). Prepare a SWOT Analysis and then identify, based on your SWOT, a new organizational strategy. Focus on one...
-
1) What is bias-free language? Answer the question and provide an example. 2) What is paraphrasing? 3) How might send tactless messages affect someone's career? 4) What are 2 things you should do...
-
What should you, the writer, consider when selecting a topic for professional or technical writing?

Study smarter with the SolutionInn App


