Consider the following variant of the findIndex method of the SortedTableMap class, originally given in Code Fragment
Question:
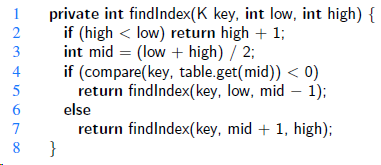
Does this always produce the same result as the original version? Justify your answer.
Transcribed Image Text:
private int findlndex(K key, int low, int high) { if (high < low) return high + 1; int mid = (low + high) / 2; if (compare(key, table.get(mid)) < 0) return findlndex(key, low, mid – 1); else 1 2 3 4 5 6. return findlndex(key, mid + 1, high); } 8.
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 66% (6 reviews)
This version is certainly wrong This can be seen by considering for exa...View the full answer

Answered By

Felix Onchweri
I have enough knowledge to handle different assignments and projects in the computing world. Besides, I can handle essays in different fields such as business and history. I can also handle both short and long research issues as per the requirements of the client. I believe in early delivery of orders so that the client has enough time to go through the work before submitting it. Am indeed the best option that any client that can think about.
4.50+
5+ Reviews
19+ Question Solved
Related Book For 

Data Structures and Algorithms in Java
ISBN: 978-1118771334
6th edition
Authors: Michael T. Goodrich, Roberto Tamassia, Michael H. Goldwasser
Question Posted:
Students also viewed these Computer science questions
-
Consider the following code fragment, taken from some package:
-
Although keys in a map are distinct, the binary search algorithm can be applied in a more general setting in which an array stores possibly duplicative elements in nondecreasing order. Consider the...
-
Consider a variant of the tree protocol called the forest protocol. The database is organized as a forest of rooted trees. Each transaction Ti must follow the following rules: The first lock in each...
-
Assume the following for the Howard Saks firm: Actual earnings of $28,000, beginning book value of $250,000, ending book value of $350,000, cost of capital of 6%. What are their abnormal earnings?
-
Selected financial statement data for Schmitzer Inc. is shown below: __________________________________________ 2018 _____________2017 Balance sheet:...
-
Explain the concept of database normalization. What are the different normal forms, and how do they contribute to a well-structured relational database? Describe a scenario where denormalization...
-
The cross-sectional area of a rectangular duct is divided into 16 equal rectangular areas, as shown in Fig. P5.23. The axial fluid velocity measured in feet per second in each smaller area is given...
-
A process stream flowing at 35k mol/h contains 15 mole% hydrogen and the remainder 1-butene. The stream pressure is 10.0 atm absolute, the temperature is 50C, and the velocity is 150m/min. Determine...
-
Explain how RTOS manage interrupt handling to minimize latency. What design considerations are typically employed to ensure low-latency interrupt processing ?
-
You are a senior auditor with Rodriguez & Jones, a small auditing firm located in Canterbury, an eastern suburb of Melbourne, Victoria. Your team has been assigned to the audit of a new client,...
-
What is the expected running time of the methods for maintaining a maxima set if we insert n pairs such that each pair has lower cost and performance than one before it? What is contained in the...
-
Implement the containKey(k) method, as described in Exercise R-10.3, for the SortedTableClass.
-
Marcy placed $3,000 each year into an investment returning 9 percent a year for her daughter's college education. She started when her daughter was two. How much had she accumulated by her daughter's...
-
What test does a court apply to determine if a privacy-invasive activity is reasonable?
-
What federal legislation protects personal information held in the private sector, and what does this statute require businesses to do?
-
____________ is the nonsexual harassment of a coworker by a group of other workers or other members of an organization designed to secure the removal from the organization of the one who is targeted.
-
What is the constitutional authority for declaring the right to privacy a human right?
-
What federal legislation protects privacy in the public sector, and how is compliance monitored?
-
What is a values statement? What is a vision statement? What is a mission statement? Why are they important? What do they contain?
-
What is the expected payoff of an investment that yields $5,000 with a probability of 0.15 and $500 with a probability of 0.85? Select one: O a. $325 O b. $5,500 O c. $2,750 O d. $1,175
-
Give a non recursive algorithm that performs an in order tree walk. An easy solution uses a stack as an auxiliary data structure. A more complicated, but elegant, solution uses no stack but assumes...
-
Show that the notion of a randomly chosen binary search tree on n keys, where each binary search tree of n keys is equally likely to be chosen, is different from the notion of a randomly built binary...
-
Give recursive algorithms that perform preorder and post-order tree walks in (n) time on a tree of n nodes.
-
Part 1 - Rent Calculation Assume the following for a floor in a multistory office building: total usable area: 62,500 sq ft; Total common area: 4,100 sq ft; total rentable area: 66,600 sq ft; Tenant...
-
14. Consider the following information on three stocks: Probability of State Rate of Return if State Occurs State of Economy of Economy Stock A Stock B Stock C Boom 0.45 0.55 0.35 0.65 Normal 0.50...
-
B2 ) Consider the following information on a portfolio of three stocks: State of Economy Probability of State of Economy Boom .15 Stock A Rate of Return .05 Stock B. Rate of Return 21 Stock C Rate of...

Study smarter with the SolutionInn App