Write a program that inserts 25 random integers from 0 to 100 in order into a linked-list
Question:
Write a program that inserts 25 random integers from 0 to 100 in order into a linked-list object. For this exercise, you’ll need to modify the List class (Fig. 21.3) to maintain an ordered list. Name the new version of the class SortedList.
Fig. 21.3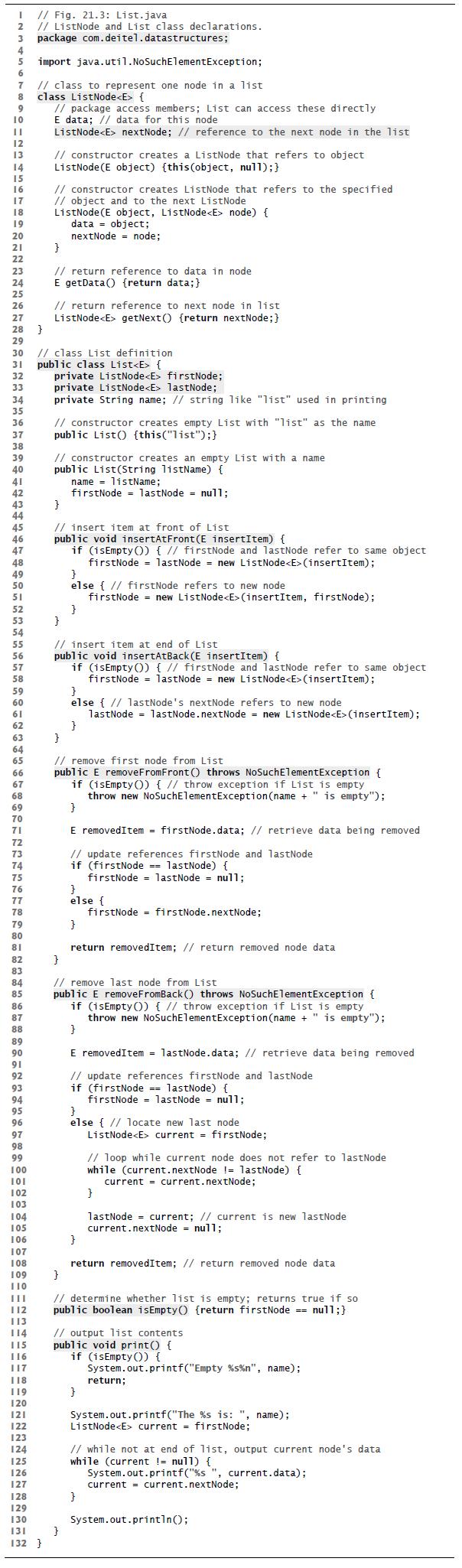
Transcribed Image Text:
I // Fig. 21.3: List.java 2 // ListNode and List class declarations. package com.deitel.datastructures; 3 4 5 6 7 8 9 10 II 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 27 28 } 29 30 // class List definition 31 public class List { 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 import java.util.NoSuchElementException; // class to represent one node in a list class ListNode { // package access members; List can access these directly E data; // data for this node ListNode nextNode; // reference to the next node in the list 126 127 // constructor creates a ListNode that refers to object ListNode(E object) {this (object, null);} 128 129 // constructor creates ListNode that refers to the specified // object and to the next ListNode ListNode(E object, ListNode node) { data object; nextNode node; } // return reference to data in node E getData() {return data; } // return reference to next node in list ListNode getNext() {return nextNode;} private ListNode firstNode; private ListNode lastNode; private String name; // string like "list" used in printing // constructor creates empty List with "list" as the name public List() {this("list");} // constructor creates an empty List with a name public List(String listName) { } // insert item at front of List public void insertAtFront (E insertItem) { if (isEmpty()) { // firstNode and lastNode refer to same object firstNode = lastNode = new ListNode (insertItem); } name listName; firstNode = lastNode = null; } } else { // firstNode refers to new node firstNode = new ListNode (insertItem, firstNode); // insert item at end of List public void insertAtBack(E insertItem) { if (isEmpty()) { // firstNode and lastNode refer to same object firstNode = lastNode = new ListNode (insertItem); } } else {//lastNode's nextNode refers to new node lastNode = lastNode.nextNode = new ListNode (insertItem); 130 131 } 132 } } // remove first node from List public E removeFromFront () throws NoSuchElementException { if (isEmpty() { // throw exception if List is empty throw new NoSuch ElementException (name + " is empty"); } E removedItem = firstNode.data; // retrieve data being removed // update references firstNode and lastNode if (firstNode == lastNode) { firstNode = lastNode= null; } else { } return removedItem; // return removed node data } // remove last node from List public E removeFromBack () throws NoSuchElementException { if (isEmpty() { // throw exception if List is empty throw new NoSuch ElementException (name + " is empty"); } E removedItem = lastNode.data; // retrieve data being removed // update references firstNode and lastNode if (firstNode == lastNode) { firstNode firstNode.nextNode; } } else { // locate new last node ListNode current = firstNode; firstNode = lastNode = null; 106 107 108 109 } 110 [[| // determine whether list is empty; returns true if so public boolean isEmpty() {return firstNode == null; } 112 113 114] 115 116 117 118 119 120 121 122 123 124 124 125 } // loop while current node does not refer to lastNode while (current.nextNode != lastNode) { current = current.nextNode; } lastNode = current; // current is new lastNode current.nextNode= null; return removedItem; // return removed node data // output list contents public void print() { if (isEmpty()) { } System.out.printf("Empty %s %n", name); return; System.out.printf("The %s is: ", name); ListNode current = firstNode; // while not at end of list, output current node's data while (current != null) { System.out.printf("%s", current.data); current current.nextNode; System.out.println();
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 100% (2 reviews)
To create a SortedList class that maintains an ordered list well first define the class that extends the capabilities of List Well need to override th...View the full answer

Answered By

JAPHETH KOGEI
Hi there. I'm here to assist you to score the highest marks on your assignments and homework. My areas of specialisation are:
Auditing, Financial Accounting, Macroeconomics, Monetary-economics, Business-administration, Advanced-accounting, Corporate Finance, Professional-accounting-ethics, Corporate governance, Financial-risk-analysis, Financial-budgeting, Corporate-social-responsibility, Statistics, Business management, logic, Critical thinking,
So, I look forward to helping you solve your academic problem.
I enjoy teaching and tutoring university and high school students. During my free time, I also read books on motivation, leadership, comedy, emotional intelligence, critical thinking, nature, human nature, innovation, persuasion, performance, negotiations, goals, power, time management, wealth, debates, sales, and finance. Additionally, I am a panellist on an FM radio program on Sunday mornings where we discuss current affairs.
I travel three times a year either to the USA, Europe and around Africa.
As a university student in the USA, I enjoyed interacting with people from different cultures and ethnic groups. Together with friends, we travelled widely in the USA and in Europe (UK, France, Denmark, Germany, Turkey, etc).
So, I look forward to tutoring you. I believe that it will be exciting to meet them.
3.00+
2+ Reviews
10+ Question Solved
Related Book For 

Java How To Program Late Objects Version
ISBN: 9780136123712
8th Edition
Authors: Paul Deitel, Deitel & Associates
Question Posted:
Students also viewed these Computer science questions
-
Modify the SortedList class from Exercise 21.7 to include a merge method that can merge the SortedList it receives as an argument with the SortedList that calls the method. Write an application to...
-
For this assignment you will write a program that inserts 20 random integers from 0 to 100 in order in a linked list object. The program will create another linked list, but with 15 random integers...
-
As presented in the text, linked lists must be searched sequentially. For large lists, this can result in poor performance. A common technique for improving list-searching performance is to create...
-
In Problems 5978, solve each equation in the complex number system. x 2 - 4 = 0
-
(a) The energy of the 28 state of lithium is -5.391eV. Calculate the value of Zeff for this state. (b) The energy of the 4s state of potassium is -4.339eV. Calculate the value of Zeff for this state....
-
Based on Kerzner, Harold. (2013) Project Management: A Systems Approach to Planning, Scheduling, and Controlling, 11th Ed. John Wiley & Sons. ISBN 978-1118022276.(Chapter 14-15) & Kerzner, Harold....
-
Show the variation of the transmission ratio, \(\frac{X_{1}}{\delta_{\mathrm{st}}}\), with \(\frac{\omega}{\omega_{1}}\) for an undamped dynamic vibration absorber for \(\omega_{2}=\omega_{1}\) and...
-
The payroll register for Robinson Company for the week ended November 18 indicated the following: Salaries .......... $1,300,000 Social security tax withheld ... 61,100 Medicare tax withheld .........
-
Daryl age 40 is leaving his company and has been offered to two options. First, is to take a deferred pension at age 65 equal to 25,000 a year. Second, take the commuted value of the deferred...
-
Write an application that reads a list of integers and stores them in a linked list. Write a method that identifies and prints the position at which the list is no longer sorted in an increasing...
-
Write a program that concatenates two linked-list objects of characters. Class ListConcatenate should include a static method concatenate that takes references to both list objects as arguments and...
-
Describe the nature of business angel funding. What types of people typically become business angels, and what is the unique role that business angels play in the process of funding entrepreneurial...
-
A binary option (also called digital option) is an exotic option for which the payoff at maturity to the holder of the option is either some US dollar amount or nothing at all. One example of a...
-
Problem 7. A card is drawn from a standard 52 card deck (a deck with 4 suits and 13 denominations per suit.) The card is noted and then replaced in the deck. The deck is shuffled and a second card is...
-
A company that produces yogurt has plants in four locations: 1) Preston, Idaho 2) New Ulm, Minnesota 3) Carthage, Texas 4) Coalwood, West Virginia. The annual capacity of each plant to produce yogurt...
-
The dataset Toyota Corolla.csv contains data on used cars on sale during the late summer of 2004 in the Netherlands. It has 1436 records containing details on 38 attributes, including Price, Age,...
-
Boys of a certain age in the nation have a mean weight of 86 with a variance of 86.49 lb. A complaint is made that boys are overfed fed in a municipal children's home. As evidence, a sample of 22...
-
Use the rules for subtraction of measurements to subtract each second measurement from the first. 1. 2876 kg 2400 kg 2. 14.73 m 9.378 m 3. 45.585 g 4.6 g 4. 34,500 kg 9,500 kg 5. 4200 km 975 km 6....
-
On October 1, 2014, the Dow Jones Industrial Average (DJIA) opened at 17,042 points. During that day it lost 237 points. On October 2 it lost 4 points. On October 3 it gained 209 points. Deter-mine...
-
How does a VLAN provide extra security for a network?
-
Find the spanning tree and the logical connection between the switches in Figure 17.14. Figure 17.14 Problem P17-7. Si LAN 1 LAN 2 LAN 3 S3
-
How does a VLAN reduce network traffic?
-
2) Write your own MATLAB function that calculates the trapezoidal estimate of an integral over a set of data points (that could be equally or unequally spaced). Your function should have two vector...
-
What are the challenges and solutions involved in implementing fault tolerance and high availability features in mission-critical operating systems, such as redundancy, failover mechanisms, and...
-
How do modern operating systems handle power management and energy efficiency, including techniques such as dynamic voltage and frequency scaling (DVFS), idle task optimization, and advanced...

Study smarter with the SolutionInn App


