Use the accompanying figure to write each vector listed as a linear combination of u and v.
Question:
Use the accompanying figure to write each vector listed as a linear combination of u and v. Is every vector in R2 a linear combination of u and v?
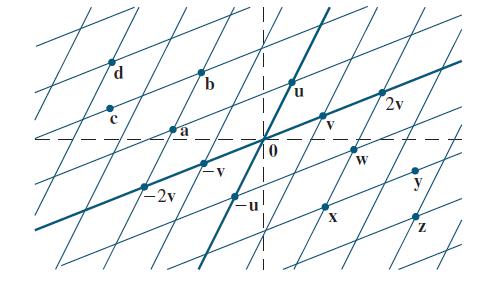
Vectors a, b, c, and d
Transcribed Image Text:
d -2v b = X 2v y 4 N
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 60% (5 reviews)
Since the grid can be extended in every direction the figure suggests that every vector in R 2 can b...View the full answer

Answered By

Sarfraz gull
have strong entrepreneurial and analytical skills which ensure quality tutoring and mentoring in your international business and management disciplines. Over last 3 years, I have expertise in the areas of Financial Planning, Business Management, Accounting, Finance, Corporate Finance, International Business, Human Resource Management, Entrepreneurship, Marketing, E-commerce, Social Media Marketing, and Supply Chain Management.
Over the years, I have been working as a business tutor and mentor for more than 3 years. Apart from tutoring online I have rich experience of working in multinational. I have worked on business management to project management.
5.00+
3+ Reviews
10+ Question Solved
Related Book For 

Linear Algebra And Its Applications
ISBN: 9781292351216
6th Global Edition
Authors: David Lay, Steven Lay, Judi McDonald
Question Posted:
Students also viewed these Mathematics questions
-
Use the accompanying figure to write each vector listed as a linear combination of u and v. Is every vector in R 2 a linear combination of u and v? Vectors w, x, y, and z d -2v b = X 2v y 4 N
-
Mark each statement True or False. Justify each answer. (If true, cite appropriate facts or theorems. If false, explain why or give a counterexample that shows why the statement is not true in every...
-
The figure shows vectors u, v, and w, along with the images T(u) and T(v) under the action of a linear transformation T :. Copy this figure carefully, and draw the image T(w) as accurately as...
-
Maggie, Bihun, and Mee decided to go into the landscaping business. The three orally declared that they would be partners in PPL Landscapers, sharing profits and losses equally. Maggie, Bihun, Mee...
-
The following information was drawn from the accounting records of Wyckoff Company as of December 31, 2016, before the temporary accounts had been closed. The Cash balance was $3,600, and Notes...
-
What are three potential flaws with the regular payback method? Does the discounted payback method correct all three flaws? Explain.
-
What might be the implications associated with a possible breakdown of the QMax computing system?
-
Bayani Bakerys most recent FCF was $48 million; the FCF is expected to grow at a constant rate of 6%. The firms WACC is 12% and it has 15 million shares of common stock outstanding. The firm has $30...
-
If Edward believes that he needs to get a bonus of $20,000 per year for the extra effort that he will be putting into the business, for what price should the first scenario option sell for at the end...
-
Times are slow for your company right now and with the rising costs of material and wages, your profits are at an all-time low. Because of this unfortunate situation, you will need to let some...
-
Find the general solutions of the systems whose augmented matrices are given. 2 4 7 0 0 7 11
-
Use the definition of Ax to write the matrix equation as a vector equation, or vice versa. Xx1 4 -1 7 -4 +x -5 3 -5 + x3 7 -8 0 2 || 6 -8 0
-
The closed-loop vehicle response in stopping a train depends on the trains dynamics and the driver, who is an integral part of the feedback loop. In Figure P8.3, let the input be R(s) = vr the...
-
A digital dashboard tracks, in a user-friendly way: a. automobile speed. b. critical business failures. c. critical business processes. d. critical business markets.
-
Which of the following frameworks could be used for SOC cybersecurity? a. NIST b. HIPPA c. PCI-DSS d. All of these options are correct. e. Two of these options are correct.
-
XBRL GL, or XBRL Global Ledger Taxonomy, is different from XBRL U.S. GAAP because it facilitates a. efficient communication between the firm and external parties. b. efficient communication within a...
-
Unauthorized alteration of records in a database system would impair which of the following components of the CIA (related to security)? a. Confidentiality b. Integrity c. Availability d....
-
The computer-based technique to accumulate and analyze data to learn about a competitor is called a. business intelligence. b. data warehouse. c. digital dashboard. d. XBRL.
-
Most married couples have two or three personality preferences in common. Myers used a random sample of 375 married couples and found that 132 had three preferences in common. Another random sample...
-
This problem continues the Draper Consulting, Inc., situation from Problem 12-45 of Chapter 12. In October, Draper has the following transactions related to its common shares: Oct 1 Draper...
-
In Exercises 9-18, construct the general solution of x' = Ax involving complex eigenfunctions and then obtain the general real solution. Describe the shapes of typical trajectories. 1. 2.
-
In Exercises 1-4, the matrix A is followed by a sequence {xk} produced by the power method. Use these data to estimate the largest eigenvalue of A, and give a corresponding eigenvector. 1. 2. 4 31...
-
Exercises 1 and 2 apply to a 3 x 3 matrix A whose eigenvalues are estimated to be 4, -4, and 3. 1. If the eigenvalues close to 4 and -4 are known to have different absolute values, will the power...
-
What challenges might organizations encounter during the implementation and sustenance of Lean Management practices, and what strategies can be employed to overcome these obstacles and ensure...
-
List six hazards you might encounter when cleaning the wet and dry areas.
-
Could you elaborate on the concept of "gemba" in Lean Management philosophy and its significance in promoting frontline employee engagement and problem-solving ?

Study smarter with the SolutionInn App