Fig. 5-4 lists some file attributes. Not listed in this table is parity. Would that be a
Question:
Fig. 5-4 lists some file attributes. Not listed in this table is parity. Would that be a useful file attribute? If so, how might it be used?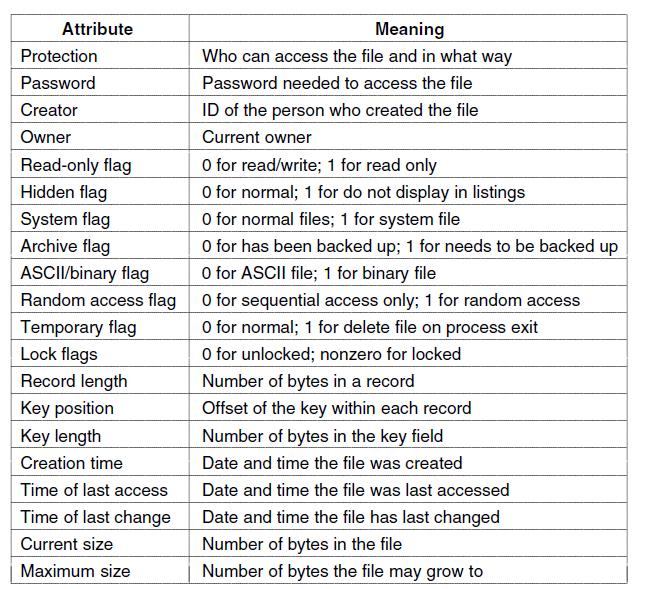
![]()
Transcribed Image Text:
Attribute Protection Password Creator Owner Read-only flag Hidden flag System flag Archive flag ASCII/binary flag Random access flag Temporary flag Lock flags Record length Key position Key length Creation time Time of last access Time of last change Current size Maximum size Meaning Who can access the file and in what way Password needed to access the file ID of the person who created the file Current owner O for read/write; 1 for read only O for normal; 1 for do not display in listings O for normal files; 1 for system file O for has been backed up; 1 for needs to be backed up O for ASCII file; 1 for binary file 0 for sequential access only; 1 for random access O for normal; 1 for delete file on process exit O for unlocked; nonzero for locked Number of bytes in a record Offset of the key within each record Number of bytes in the key field Date and time the file was created Date and time the file was last accessed Date and time the file has last changed Number of bytes in the file Number of bytes the file may grow to
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 80% (5 reviews)
Parity is a concept commonly used in digital data transmission and storage systems to detect errors ...View the full answer

Answered By

Utsab mitra
I have the expertise to deliver these subjects to college and higher-level students. The services would involve only solving assignments, homework help, and others.
I have experience in delivering these subjects for the last 6 years on a freelancing basis in different companies around the globe. I am CMA certified and CGMA UK. I have professional experience of 18 years in the industry involved in the manufacturing company and IT implementation experience of over 12 years.
I have delivered this help to students effortlessly, which is essential to give the students a good grade in their studies.
3.50+
2+ Reviews
10+ Question Solved
Related Book For 

Operating Systems Design And Implementation
ISBN: 9780131429383
3rd Edition
Authors: Andrew Tanenbaum, Albert Woodhull
Question Posted:
Students also viewed these Computer science questions
-
THIRD AVENUE SOFTWARE HEALTH-CARE APP PROJECT This case is new for the ninth edition of Information Technology Project Management . The case provides an opportunity to apply agile and Scrum...
-
Gord Moore, founder of Moore AI Machines (MAIM) sat at his desk awestruck by what was happening. After two years of sacrifice, sleeping on a cot in the office and eating No Name KD, the Ai Kaizen...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Carlberg Company has two manufacturing departments, Assembly and Painting. The Assembly department started 11,000 units during November. The following production activity in both units and costs...
-
This case is based on the consolidated financial statements of Foot Locker, Inc., given in Appendix B at the end of this book. In particular, this case uses Foot Locker, Inc.s consolidated statement...
-
In Problem 13.9 on page 532, an agent for a real estate company wanted to predict the monthly rent for apartments, based on the size of an apartment. The data are stored in Rent. a. Construct a 95%...
-
Table B. 11 presents data on the quality of Pinot Noir wine. a. Build a regression model relating quality \(y\) to flavor \(x_{4}\) that incorporates the region information given in the last column....
-
You are engaged by the owner of a small firm to recommend a one-year compensation contract for the firm's top manager. She is concerned about cash flow and feels that in previous years the manager...
-
# HT WT CHOL 1 16 57 94.3 2 Percentiles (Source: Dr. Diane Kiernan, APM 510 Reader Final Edition Fall Place functions to answer the questions in the yellow cells. AGE a. Find the percentile for...
-
Redesign adjust to avoid the problem of signaled processes being killed unnecessarily because of a too-strict test for stack space.
-
In the previous problem does it matter whether the boot monitor takes exactly as much memory as it needs or if it is rounded up to units of clicks? Data from previous problem IBM-compatible computers...
-
How many moles are in a 2.0 cm 2.0 cm 2.0 cm cube of copper?
-
What transferable skills can individuals trained in either game design or user experience (UX) design bring to the practice?
-
Which of the following best describes skimming? 1. Skimming involves the theft of cash after the cash is recorded in the companys accounting system. 2. Skimming involves the theft of cash prior to...
-
Which two adjustments are made to the fraud triangle to accommodate predators? 1. The fraud triangle is not meant to differentiate between accidental and predator raudsters. 2. Criminal mindset and...
-
Should gamified systems always be voluntary? Make an argument about if and when it is ever appropriate to make the use of a gamified system mandatory. Describe which scenarios may be fitting for such...
-
What created to opportunity for Enron to trade in this market?
-
Babbit, Inc., a multinational corporation based in the United States, owns an 80% interest in Nakima Company, which is located in Sydney, Australia. The acquisition occurred on January 1, 2008. The...
-
A parking lot charges $3 for the first hour (or part of an hour) and $2 for each succeeding hour (or part), up to a daily maximum of $10. (a) Sketch a graph of the cost of parking at this lot as a...
-
Provide the type and hexadecimal representation of following instruction: sw $t1, 32($t2)
-
Provide the type, assembly language instruction, and binary representation of instruction described by the following MIPS fields: op = 0, rs = 3, rt = 2, rd = 3, shamt = 0, funct = 34
-
Provide the type, assembly language instruction, and binary representation of instruction described by the following MIPS fields: op = 0 x 23, rs = 1, rt = 2, const = 0 x 4
-
As per the requirement from traffic authorities, you team manager has requested you to develop an algorithm or a program with features including INSERT, DELETE and RE- ENTER operations in FIFO...
-
datafile is an empty file opened into the file descriptor datafd. What will be the contents of datafile after the following code runs? write(datafile, "Hello", 6); if(fork() 0) ( } == {...
-
3. Write a program to sum elements of an array. Assign the variables. Define an array by asking the user for size. Take the elements of the array from user. Sum all the elements of the array and...

Study smarter with the SolutionInn App