Implement the dictionary ADT of Figure 4.27 using an unsorted linked list as defined by class LList
Question:
Implement the dictionary ADT of Figure 4.27 using an unsorted linked list as defined by class LList in Figure 4.8.
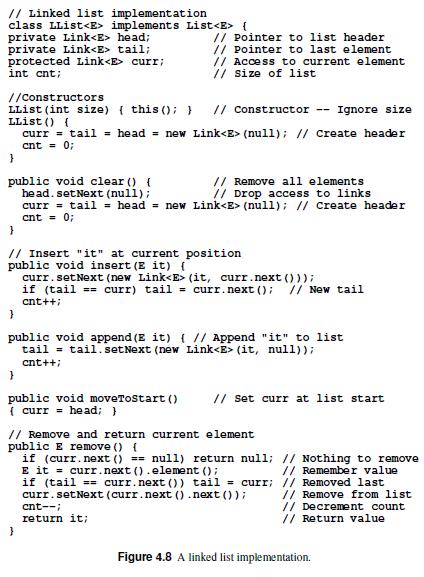
Make the implementation as efficient as you can, given the restriction that your implementation must use the unsorted linked list and its access operations to implement the dictionary.
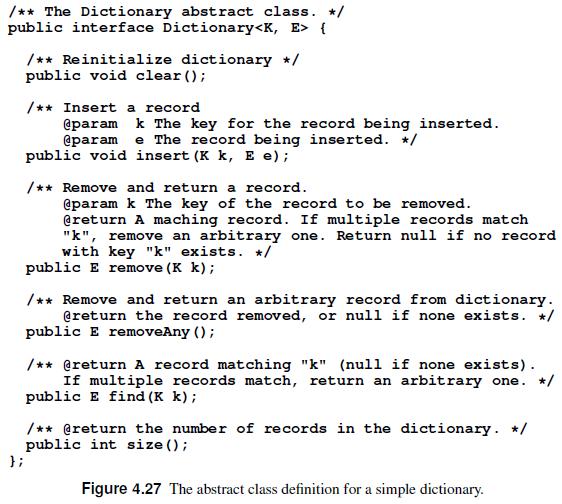
State the asymptotic time requirements for each function member of the dictionary ADT under your implementation.
Transcribed Image Text:
// Linked list implementation class LList implements List { private Link head; private Link tail; protected Link curr; int cnt; //Constructors LList (int size) { this(); } LList() { // Constructor -- Ignore size curr = tail = head = new Link (null); // Create header cnt = 0; } public void clear() { // Remove all elements. // Drop access to links. head.setNext (null); curr = tail = head = new Link (null); // Create header cnt = 0; // Pointer to list header // Pointer to last element // Access to current element // Size of list. } // Insert "it" at current position public void insert (E it) ( curr.setNext (new Link (it, curr.next())); if (tail == curr) tail = curr.next(); // New tail cnt++; } public void append (E it) { // Append "it" to list tail = tail.setNext (new Link (it, null)); cnt++; } public void moveToStart() {curr = head; } } // Set curr at list start // Remove and return current element public E remove() { if (curr.next() == null) return null; E it = curr.next().element (); if (tail == curr.next()) tail = curr; curr.setNext (curr.next() .next()); cnt--; return it; // Nothing to remove // Remember value // Removed last // Remove from list // Decrement count // Return value. Figure 4.8 A linked list implementation.
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 100% (QA)
Part 1 Part 2 Part 3 java public interface Dictionary void clear boolean containsK key voi...View the full answer

Answered By

Jayshree Rathi
Hello Students!
This is Jayshree Rathi. I work on a number of renowned student-centric channels such as Chegg, coursehero, as a certified private tutor.
If you are looking for relevant and original content to complete your assignments, essays, and homework, then contact me and within the promised time, I will deliver you your personalized academic work and help you score the best.
4.80+
1+ Reviews
10+ Question Solved
Related Book For 

Practical Introduction To Data Structures And Algorithm Analysis Java Edition
ISBN: 9780136609117
1st Edition
Authors: Clifford A. Shaffer
Question Posted:
Students also viewed these Computer science questions
-
Define an ADT for a bag (see Section 2.1 ) and create an array-based implementation for bags. Be sure that your bag ADT does not rely in any way on knowing or controlling the position of an element....
-
The following additional information is available for the Dr. Ivan and Irene Incisor family from Chapters 1-5. Ivan's grandfather died and left a portfolio of municipal bonds. In 2012, they pay Ivan...
-
List three specific parts of the Case Guide, Objectives and Strategy Section (See below) that you had the most difficulty understanding. Describe your current understanding of these parts. Provide...
-
Capital Inc. has prepared the operating budget for the first quarter of 2015. They forecast sales of $50,000 in January, $60,000 in February, and $70,000 in March. Variable and fixed expenses are as...
-
Helium gas enters a steady-flow expander at 800 kPa, 300C, and exits at 120 kPa. The mass flow rate is 0.2 kg/s, and the expansion process can be considered as a reversible polytropic process...
-
For the ladder network in Fig. 2.104 , find I and R eq . 82 62 15 V Rea
-
Assuming the same data as given in problem 9, was the well in each case profitable? Discuss your answer. Problem 9:- Property cost (acquisition cost). Drilling cost (one well). Estimated completion...
-
This problem is based on the 2008 annual report of Intel Corporation in the appendix. Required: a. Compute the following profitability measures for the year ended December 27, 2008: 1. Return on...
-
2. Two 2.5 kg masses are connected through a string as shown below. The magnitude of the force of friction on the ramp is 4.85 N. If the ramp is 5m long and mass 2 is already half way up the ramp,...
-
Implement the dictionary ADT of Figure 4.27 based on stacks. Your implementation should declare and use two stacks. /** The Dictionary abstract class. */ public interface Dictionary { }; /**...
-
Implement a collection of freelists for variable-length strings, as described at the end of Section 4.1.2. For each such freelist, you will need an access function to get it if it exists, and...
-
Fill in the blanks. Chemists will often say that a covalent bond is two electrons shared between two atoms. Technically, this is not correct. They should really say A covalent bond is...
-
Use the data for the fictitious countries of Adrienia Adrienia Cliffordstan and Cliffordstan to complete the following 8. Which country is experiencing a recessionary gap? Explain how you got your...
-
Recent technology and how it could affect TMT over the course of time. Be sure to integrate a Biblical worldview. Conclude your paper with a reflection on the increasing speed of technology,...
-
The pressure in a container is 52 kPa. If this pressure is measured using a manometer (U-tube) with one end exposed to atmospheric pressure (101.325 kPa), and is filled with a substance having...
-
1. What is the basic of aircraft structure 2. What are the different types of aircraft structure repair
-
A steel bar that has a rectangular cross-section of 0.4 inches by 0.5 inches. The bar is 3 inches long and subjected to a load of 45000 lbf that is parallel to its length. What is the resulting...
-
Place the number of the appropriate definition in the blank next to each concept. _________Period cost 1. Cost that varies with the volume of activity. _________Indirect cost 2. Sacrifice of...
-
a. Why does the Wi-Fi Alliance release compatibility testing profiles in waves instead of combining the entire standards features initially? 27a1.) An 802.11ac Wi-Fi compatibility testing profile...
-
Ten sources, six with a bit rate of 200 kbps and four with a bit rate of 400 kbps, are to be combined using multilevel TDM with no synchronizing bits. Answer the following questions about the final...
-
Which of the three multiplexing techniques is common for fiber-optic links? Explain the reason.
-
We have 14 sources, each creating 500 8-bit characters per second. Since only some of these sources are active at any moment, we use statistical TDM to combine these sources using character...
-
Etisalat Corporation had operating earnings of AED 600000 for the year just ended. They also sold some assets worth AED 200000 which they purchased before 1 year by AED 100000. The taxable income...
-
You are considering two assets with the following characteristics: E(R1)=0.10 St. Deviation--Q1=0.20 E(R2) = 0.20 St. Deviation--Q2=0.15 W1 = 0.4 W2=0.6 Compute the Standard Deviation of Portfolio...
-
Consider the embedded methods where x = x(to) +=(F1 + F2+4F3) 11 (F + F + 4F 3 ) 6 1 x = x(to))+(F + F) (F + F) If Fhf (to, x(to)) F2 = hf (to+h, x(to) + F) F3 = hf(to+h/2, x(to) + (F1 + F2)/4). x(t)...

Study smarter with the SolutionInn App


