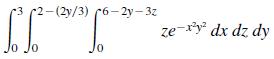
In Exercises 11 and 12, use a computer algebra system to evaluate the triple iterated integral. 3
Question:
In Exercises 11 and 12, use a computer algebra system to evaluate the triple iterated integral.
Transcribed Image Text:
3 2-(2y/3) 6-2y-3z -6573) "* CC 10 0 ze-x²y² dx dz dy
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 50% (4 reviews)
ANSWER To evaluate the triple iterated integral well use a computer algebra system The triple iterat...View the full answer

Answered By

Chandrasekhar Karri
I have tutored students in accounting at the high school and college levels. I have developed strong teaching methods, which allow me to effectively explain complex accounting concepts to students. Additionally, I am committed to helping students reach their academic goals and providing them with the necessary tools to succeed.
0.00
0 Reviews
10+ Question Solved
Related Book For 

Calculus Of A Single Variable
ISBN: 9781337275361
11th Edition
Authors: Ron Larson, Bruce H. Edwards
Question Posted:
Students also viewed these Mathematics questions
-
In Exercises 11 and 12, use a computer algebra system to evaluate the triple iterated integral. 9-y INI 9-yJo y dz dx dy
-
In Exercises 9 and 10, use a computer algebra system to evaluate the triple iterated integral. n/2 /2 (sin 8 0 0 2p cos o dp de do
-
In Exercises 9 and 10, use a computer algebra system to evaluate the triple iterated integral. */2 re" de dr dz
-
Linda has d dollars in an account that pays 1.4% interest, compounded weekly. She withdraws w dollars. Express her first weeks interest algebraically.
-
Software Plus Corporation produces flight and driving simulations and games for personal computers. The president has a complaint about the accounting for support department costs. He points to the...
-
Dougs Diner acquired a fast-food restaurant for $1,500,000. The fair market values of the assets acquired were as follows. No liabilities were assumed. Equipment ..........$380,000 Land ................
-
The vapour that is about to condense is called the (a) Superheated vapour (b) Compressed vapour (c) Saturated vapour (d) None of these.
-
To promote computer education, a leading computer manufacturer donates $4 million to the Kerrville Independent School District. The donor stipulates that the district is to establish an endowment,...
-
A circular ring is made of a material with uni- form density p (kg/m). The ring has a rectan- gular cross section, as shown in the figure. The outer radius of the ring is R. We would like to...
-
In Exercises 1318, set up a triple integral for the volume of the solid. Do not evaluate the integral. The solid in the first octant bounded by the coordinate planes and the plane z = 7 - x - 2y
-
In Exercises 310, evaluate the triple iterated integral. ^{2_1 + 3x 3.0 10 x cos y dz dy dx
-
The predicted mortality of cardiac surgery patients in an intensive care unit, based on their APACHE score, is found based on a logistic regression model applied to patients over a four-year period....
-
This week, you learned about secondary data. Secondary data is also known as "desk data" because it can be retrieved without leaving your desk. That quality makes it convenient, but also raises...
-
One bond has a coupon rate of 8%, another a coupon rate of 12%. Both bonds pay coupons semiannually, have 10-year maturities, and sell at a yield to maturity of 10%. If their yields to maturity next...
-
Should a country attempt to achieve IRP? What policy options the government has achieve IRP? Explain the steps in testing IRP with real data. With the growth of big data and the use of technology in...
-
China has accumulated massive savings during zero Covid. Some analysts hope the Chinese will spend these savings, much as Americans did after the lockdown, giving a much needed stimulus to the global...
-
Solve the following ledger, 1. We buy goods on credit for $30,000.00, we pay 50% in cash, and the rest on credit. 2. We buy goods on credit for $150,000.00, we pay 50% in cash, 30% on credit and for...
-
The Piedmont Investment Corporation has identified four small apartment buildings in which it would like to invest. The four banks generally used by Piedmont have provided quotes on the interest...
-
(a) What do data breach notification laws require? (b) Why has this caused companies to think more about security?
-
Use Stokes's Theorem c F . dr In each case, C is oriented counterclockwise as viewed from above. F(x, y, z) = 2yi + 3zj + xk C: triangle with vertices (2, 0, 0), (0, 2, 0), and (0, 0, 2)
-
Use Greens Theorem to evaluate the integral for the given path. C: boundary of the region lying inside the rectangle bounded by x = -5, x = 5, y = -3, and y = 3, and outside the square bounded by x =...
-
Determine whether the vector field is conservative. F(x, y, z) = yzi + 2xyzj + xyk
-
This is the JAVA Question. Exercise 1.22. Write a class that can generate random strings with characters in a given set. For example, RandomStringGenerator generator generator.addRange('a', 'z');...
-
1. Create and array of objects named movies. Each of the objects in the array will represent a movie. Each object should have properties for: movie title (string) release year (number) rating (your...
-
What methods are polymorphic in the Employee Hierarchy? How could we build a method like getRandShape() above but for use with Employees? If we built a getRandomEmployee() method that returns various...

Study smarter with the SolutionInn App