Consider the following fragment of code in C: (a) Assume that each integer variable occupies four bytes.
Question:
Consider the following fragment of code in C: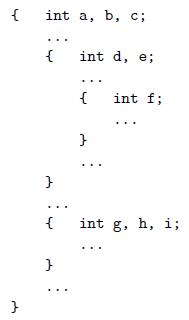 (a) Assume that each integer variable occupies four bytes. How much total space is required for the variables in this code?
(a) Assume that each integer variable occupies four bytes. How much total space is required for the variables in this code?
(b) Describe an algorithm that a compiler could use to assign stack frame offsets to the variables of arbitrary nested blocks, in a way that minimizes the total space required.
Transcribed Image Text:
{ int a, b, C; { int d, e; { int f; int g, h, i;
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 60% (10 reviews)
a Variables a b and c are live throughout the execution of the o...View the full answer

Answered By

Benard Ndini Mwendwa
I am a graduate from Kenya. I managed to score one of the highest levels in my BS. I have experience in academic writing since I have been working as a freelancer in most of my time. I am willing to help other students attain better grades in their academic portfolio. Thank you.
4.90+
107+ Reviews
240+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
In this exercise, we examine how resource hazards, control hazards, and Instruction Set Architecture (ISA) design can affect pipelined execution. Problems in this exercise refer to the following...
-
Consider the following code fragment in a high-level language: Assume that Q is an array of 32-byte records and the VAL field is in the first 4 bytes of each record. Using x86 code, we can compile...
-
This part of our case study will focus on the amount of instruction-level parallelism available to the run time hardware scheduler under the most favorable execution scenarios (the ideal case)....
-
Consider X[k] be the N-point DFT of an N-point sequence x[n]. (20 %) x [n] = {1, -2, 1, 3} x [n] = {0, 2, -1,0,0,4} (a) Determine the linear convolution x [n] * x [n] (5%) (b) Determine the...
-
In the early 2000s, as a way to diversify risk, financial institutions bundled mortgages from many people into one investment. The underlying concept was that, if one person defaulted on a mortgage,...
-
Hanks Hotel opened for business on May 1, 2020. Its trial balance before adjustment on May 31 is as follows. In addition to those accounts listed on the trial balance, the chart of accounts for Hanks...
-
The Principles for Responsible Investment (PRI) in their ESG integration in listed equity: A technical guide (2023) defines ESG integration as the process of including ESG factors in investment...
-
M. M. Sprout, a catalog mail order retailer, has one customer service representative (CSR) to take orders at an 800 telephone number. If the CSR is busy, the next caller is put on hold. For...
-
5. Find the following vector integrals (a) [ [(sint cost)i + (tlnt)j + (te')k] dt - t i+ 1 [(7) + (12 + 3 + 2 ) j + (cos t)k] dt t2 (c) / \(sinht)i+(cosht)j + (arctan 2t)k at dt
-
Allie has bought a new apple orchard. The orchard has a single file of trees, numbered from 1 to N. Each tree has a certail number of ripe apples. Allie has a rule she wants to follow. She wants to...
-
Rewrite Figures 3.6 and 3.7 in C. You will need to use separate compilation for name hiding. Figures 3.6 Figures 3.7 #include namespace rand_mod { unsigned int seed = time (0); // initialize from...
-
Consider the design of a Fortran 77 compiler that uses static allocation for the local variables of subroutines. Expanding on the solution to the previous question, describe an algorithm to minimize...
-
In Problem find the intervals on which f(x) is increasing, the intervals on which f(x) is decreasing, and the local extrema. f(x) = -3x 3 - 9x 2 + 72x + 20
-
In which scenario is it appropriate for confidential information to be used? A. Writing to a log file B. Printing a stack trace C. Outputting to System.err D. Storing in a String E. Writing an...
-
Which statements about the clone() method are correct? (Choose two.) A. Calling clone() on a class that does not implement Cloneable results in a compiler error. B. Calling clone() on a class that...
-
The following code prints false. Which statements best describe the Fruit class? (Choose three.) A. It does not implement Cloneable. B. It performs a deep copy. C. It performs a shallow copy. D. It...
-
Fill in the blanks with the proper method names to serialize an object. (Choose two.) A. readResolve in the first blank B. writeReplace in the first blank C. writeObject in the first blank D....
-
Which statement best describes the following method? A. It is not susceptible to any common attacks. B. It is at risk of SQL injection attack only. C. It is at risk of a denial of service attack...
-
Graffiti Advertising, Inc., reported the following financial statements for the last two years. Construct the cash flow identity for the company. Explain what each number means. 2014 Income Statement...
-
Could a set of three vectors in span all of? Explain. What about n vectors in when n is less than m? R4
-
The order of an algorithm that increments every element in a twodimensional table of N rows. 1. O(1) 2. O(logN) 3. O(N) 4. O(N logN) 5. O(N*N) 6. O(N*N*N)
-
The order of an algorithm that decrements every element in a three-dimensional table of N rows. 1. O(1) 2. O(logN) 3. O(N) 4. O(N logN) 5. O(N*N) 6. O(N*N*N)
-
The order of sorting an array of N items using one of the slower sorting algorithms such as SelectionSort. 1. O(1) 2. O(logN) 3. O(N) 4. O(N logN) 5. O(N*N) 6. O(N*N*N)
-
On January 1, 2023, Bertrand, Incorporated, paid $86,900 for a 40 percent interest in Chestnut Corporation's common stock. This investee had assets with a book value of $229,500 and liabilities of...
-
Landen Corporation uses a job-order costing system. At the beginning of the year, the company made the following estimates: Direct labor-hours required to support estimated production Machine-hours...
-
Explain the concept of gene-environment interactions, and how these interactions influence the expression of complex traits and the risk of developing multifactorial diseases ?

Study smarter with the SolutionInn App