Consider the following pseudocode: What does this programprint if the language uses static scoping? What does it
Question:
Consider the following pseudocode: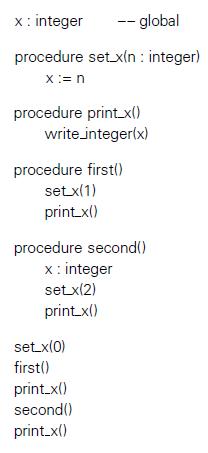 What does this programprint if the language uses static scoping? What does it print with dynamic scoping? Why?
What does this programprint if the language uses static scoping? What does it print with dynamic scoping? Why?
Transcribed Image Text:
x: integer -- global procedure set xln : integer) x:= n procedure print.x() write.integer(x) procedure firstl) setx(1) print xl) procedure second() x : integer setx(2) print x() setx(0) first() print.x() second() print.x()
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 62% (8 reviews)
With static scoping it prints 1 1 2 2 ...View the full answer

Answered By

Susan Juma
I'm available and reachable 24/7. I have high experience in helping students with their assignments, proposals, and dissertations. Most importantly, I'm a professional accountant and I can handle all kinds of accounting and finance problems.
4.40+
15+ Reviews
45+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
Show a trace of the contents of the referencing environment A-list during execution of the program in (a) Figure 3.9. Assume that a positive value is read at line 8. Figure 3.9: (b) Exercise 3.14....
-
Repeat the previous exercise for a central reference table. Data From Previous Exercises: Show a trace of the contents of the referencing environment A-list during execution of the program in (a)...
-
Consider the following pseudocode: x : integer := 1 y : integer := 2 procedure add() x := x + y procedure second(P : procedure) x : integer := 2 P() procedure first y : integer := 3 second(add)...
-
A bond has an expected return of 15.33%, sensitivity to the term factor of 1.95 and to the default factor of 0.65. The current term risk premium is 3.01%. The risk-free rate of return is 3%. What is...
-
(a) An activity to improve the well-being of some impoverished people will provide benefits of $1 million right now, but it will obliterate the earth in 200 years. The world's value in 200 years is...
-
Consider the following recurrence equation, defining a function T(n): Show, by induction, that T(n) = n(n + 1)/2. if n = 1 T(n) = 3 T(n 1) +n otherwise, 1
-
The following information has been extracted from the financial statements and notes thereto of Bass and Dide Ltd, consultants. Required (a) Calculate the following ratios for 2025: i. return on...
-
For the year ended December 31, 2012, the job cost sheets of Dosey Company contained the following data. Other data: 1. Raw materials inventory totaled $20,000 on January 1. During the year, $100,000...
-
Let r(t)=(5-t, 4t - 3, 7t) and P(4, 1, 7). (a) Find the arc length function s(t) for the curve measured from the point P in the direction of increasing t. (b) Reparametrize the curve with respect to...
-
Through Engineering, human achievement continues to advance. Write about your favorite example of engineering in action and what impresses you about it from an Engineering standpoint.
-
Consider the following program in Scheme: What does this programprint? What would it print if Scheme used dynamic scoping and shallow binding? Dynamic scoping and deep binding? Explain your answers....
-
The principal argument in favor of dynamic scoping is that it facilitates the customization of subroutines. Suppose, for example, that we have a library routine print integer that is capable of...
-
In 2013, the City of Coyote received a $320,000 cash grant from the state to stop air pollution. Assume that although a special revenue fund could have been set up, the money remained in the General...
-
Which statements about executing the following program are correct? (Choose two.) A. Line p1 makes the code susceptible to tainted inputs from the user. B. Line p2 makes the code susceptible to...
-
Which techniques best prevent sensitive objects from being manipulated by an attacker who wants to create a malicious subclass? (Choose three.) A. Add final to the class declaration. B. Set protected...
-
What are the best scenarios for customizing the serialization process? (Choose two.) A. To prevent SQL injection. B. To shuffle data among users. C. It is the only way to prevent a sensitive field...
-
Youve been hired by Charlie Sweets to perform a security audit of their login system. After reviewing the following code, what recommendations would best improve the security of their system? (Choose...
-
Which type of attack requires more than one source to initiate? A. Billion laughs attack B. Million frowns attack C. Distributed denial of service attack D. SQL injection E. Inclusion attack F....
-
Draiman, Inc., has sales of $795,000, costs of $345,000, depreciation expense of $76,000, interest expense of $41,000, and a tax rate of 35 percent. What is the net income for this firm? Suppose the...
-
When the concentration of a strong acid is not substantially higher than 1.0 10-7 M, the ionization of water must be taken into account in the calculation of the solution's pH. (a) Derive an...
-
Distinguish between composition and inheritance.
-
Name three ways that classes can relate to each other.
-
Why is it good practice to put a class declaration in one file and the implementation in another?
-
The Production Department of Hruska Corporation has submitted the following forecast of units to be produced by quarter for the upcoming fiscal year: Units to be produced 1st Quarter 2nd Quarter 3rd...
-
You go to the hardware store to buy a new 50 ft garden hose. You find you can choose between hoses of inch and inch inner diameter. Compare the rate at which water flows through the two types of...
-
Miller Company's contribution format income statement for the most recent month is shown below: Sales (32,000 units) Variable expenses Total $ 224,000 128,000 Contribution margin 96,000 Per Unit $...

Study smarter with the SolutionInn App