Read the following paragraph and decide which of the five statements are true. (More than one...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
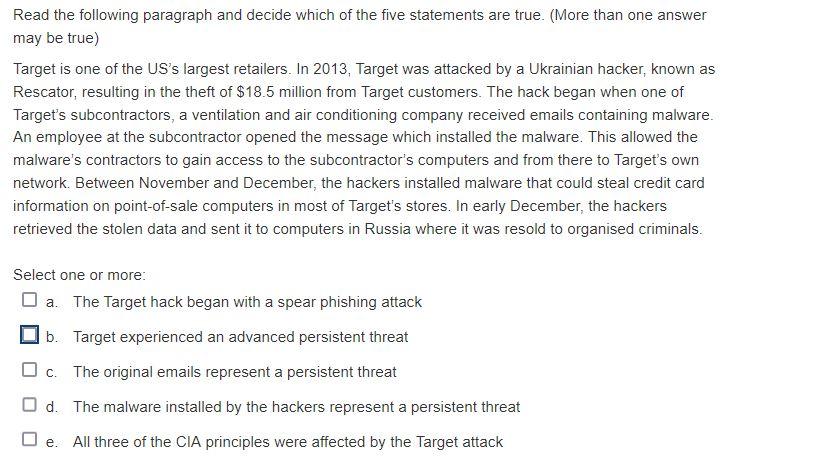
Read the following paragraph and decide which of the five statements are true. (More than one answer may be true) Target is one of the US's largest retailers. In 2013, Target was attacked by a Ukrainian hacker, known as Rescator, resulting in the theft of $18.5 million from Target customers. The hack began when one of Target's subcontractors, a ventilation and air conditioning company received emails containing malware. An employee at the subcontractor opened the message which installed the malware. This allowed the malware's contractors to gain access to the subcontractor's computers and from there to Target's own network. Between November and December, the hackers installed malware that could steal credit card information on point-of-sale computers in most of Target's stores. In early December, the hackers retrieved the stolen data and sent it to computers in Russia where it was resold to organised criminals. Select one or more: a. The Target hack began with a spear phishing attack b. Target experienced an advanced persistent threat ☐c. The original emails represent a persistent threat Od. The malware installed by the hackers represent a persistent threat □e. All three of the CIA principles were affected by the Target attack Read the following paragraph and decide which of the five statements are true. (More than one answer may be true) Target is one of the US's largest retailers. In 2013, Target was attacked by a Ukrainian hacker, known as Rescator, resulting in the theft of $18.5 million from Target customers. The hack began when one of Target's subcontractors, a ventilation and air conditioning company received emails containing malware. An employee at the subcontractor opened the message which installed the malware. This allowed the malware's contractors to gain access to the subcontractor's computers and from there to Target's own network. Between November and December, the hackers installed malware that could steal credit card information on point-of-sale computers in most of Target's stores. In early December, the hackers retrieved the stolen data and sent it to computers in Russia where it was resold to organised criminals. Select one or more: a. The Target hack began with a spear phishing attack b. Target experienced an advanced persistent threat ☐c. The original emails represent a persistent threat Od. The malware installed by the hackers represent a persistent threat □e. All three of the CIA principles were affected by the Target attack
Expert Answer:
Answer rating: 100% (QA)
option abd Explanation option A is True as attack was intiated as phising attack ... View the full answer

Related Book For 

Business Communication In Person, In Print, Online
ISBN: 978-1111533168
8th edition
Authors: Amy Newman, Scot Ober
Posted Date:
Students also viewed these programming questions
-
Read the following paragraph and give your response: 1. Leo, a biologically male employee of Delta Dismantlers, Inc., an auto salvage yard in California, planned to have a gender reassignment surgery...
-
Read the following paragraph and give your response after analyzing it: My industry of interest is Banking and Finance because Bank is the heart of any country's economy. It is essential for any...
-
Read the following paragraph and give response: I am doing internship at market central, which offers innovative products all around the world through the virtual platform. This company cannot work...
-
A stock is trading at $70. You believe there is a 70% chance the price of the stock will increase by 10% over the next 3 months. You believe there is a 10% chance the stock will drop by 10%, and you...
-
What is the relationship between the value of a firm and its capital structure, given the existence of a corporate income tax, bankruptcy costs, and agency costs?
-
Refer to the Development Psychology (Mar. 2003) study of the behavior of elementary school children, presented in Exercise. The researchers used a quadratic equation to model the level (y) of...
-
Interview someone in law enforcement or the legal field who has worked with forensic accountants and discuss the following: a. Describe your experiences with forensic accountants. b. What...
-
Little 6, Inc. an accounting firm, forecasts the following weekly workload during the tax season: Corporate tax returns each require 4 hours of an accountants time, and personal returns each require...
-
PREFERRED STOCKS PLEASE ANSWER WITH COMPLETE SOLUTION. BG CORPORATION ISSUED THE FOLLOWING 780 COMMON STOCKS PAR VALUE $100 680 PARTICIPATING PREFERRED STOCKS PAR VALUE $100 AT 7% BG CORPORATION...
-
Ethan is the leader of a team with N members. He has assigned an error score to each member in his team based on the bugs that he has found in that particular team member's task. Because the error...
-
Which QuickBooks Company file users can view the Cash flow hub? A Admin user B User with cash flow hub rights C Accountant user with full access rights D B and C E A and C
-
For each of the Bronsted-Lowery acid base reactions below, draw the conjugate acid and conjugate base pairs most likely to form. (b) Circle the set of arrows that best describe the equilibrium for...
-
Show that the set {5, 15, 25, 35} is a group under multiplication modulo 40. What is the identity element of this group? Can you see any relationship between this group and U(8)? Additionally, A...
-
6) An investor is considering a $25,000 investment in a start-up company. She estimates that she has a probability of 0.45 of a $60,000 loss, probability of 0.25 of a $40,000 profit, probability of...
-
How can a leader motivate their team to work towards the company\'s vision? Is having a vision in and of itself sufficient? Why or why not?
-
You have a bowling ball weighing 5 kg suspended by a spring that has a spring constant of 5 N/m. When you hold the bowling ball to the ground and then release it, it follows simple harmonic motion....
-
Check my work 3 Olympic Sports has two issues of debt outstanding. One is a 9% coupon bond with a face value of $29 million, a maturity of 10 years, and a yield to maturity of 10%. The coupons are...
-
Write the binomial probability in words. Then, use a continuity correction to convert the binomial probability to a normal distribution probability. P(x 110)
-
As part of your application for a one-semester internship at American Express, you are asked to include a letter of recommendation from one of your business professors. You earned a good grade in MGT...
-
Assume that you have evaluated two candidates for the position of sales assistant. This is what you have learned: Carl Barteolli has more sales experience. Elizabeth Larson has more appropriate...
-
Imagine that youre the CEO of a retail store such as Aggresshop this chapter and at.Lets say youre planning to redesign each of the 16 stores in the United States. As part of this effort, youll need...
-
What are the characteristics of closed-end mutual funds?
-
Noah is thinking about investing $1,000 in a global mutual fund. However, the fund is a load fund, which charges a commission of 8.5 percent. The investment company would deduct this fee from Noahs...
-
What are three ways in which you can receive income from your mutual fund investments?

Study smarter with the SolutionInn App