1. 2. The Student Loan Application Office (SLAO) of Country A's Government has decided to build...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
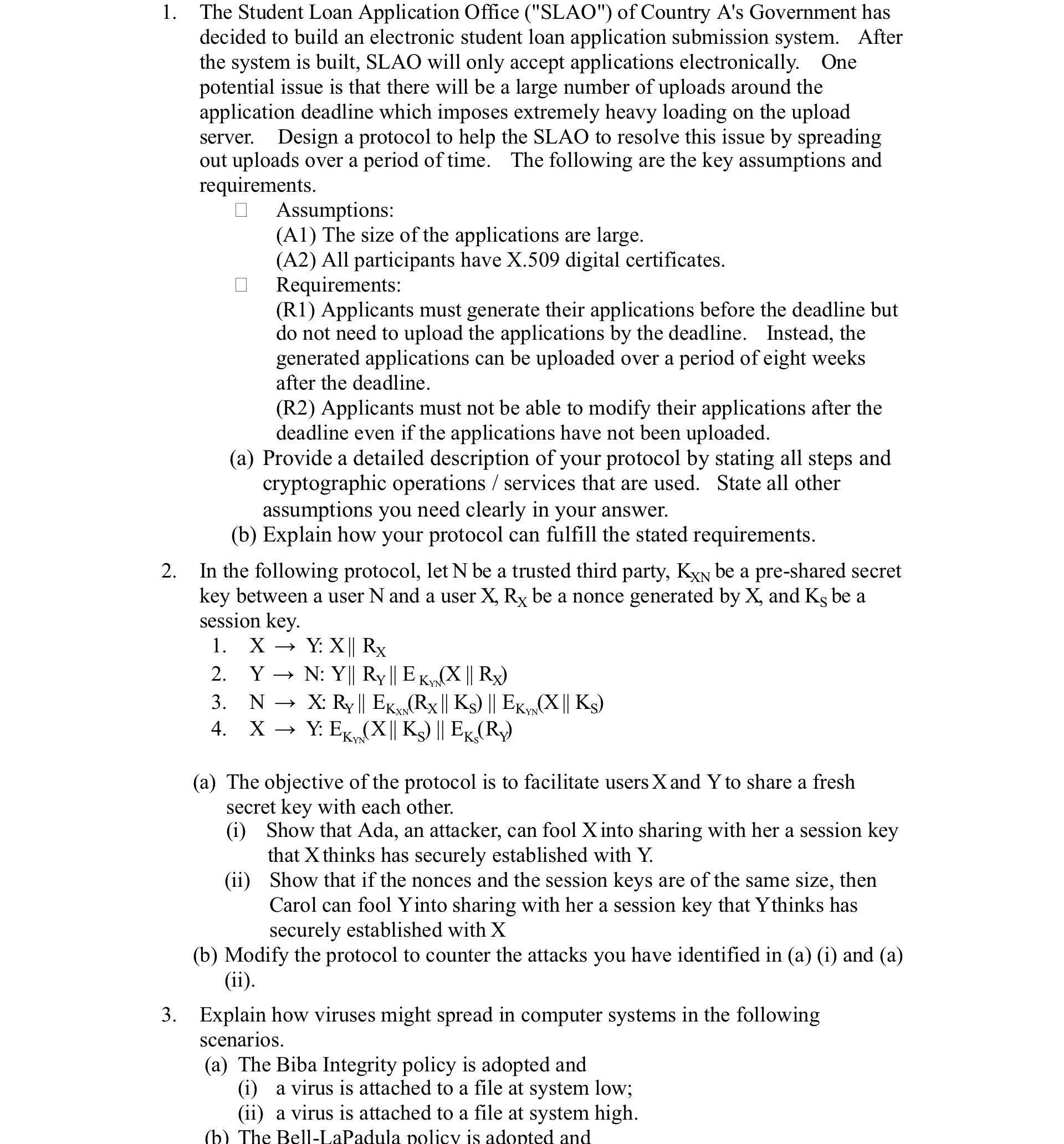
1. 2. The Student Loan Application Office ("SLAO") of Country A's Government has decided to build an electronic student loan application submission system. After the system is built, SLAO will only accept applications electronically. One potential issue is that there will be a large number of uploads around the application deadline which imposes extremely heavy loading on the upload server. Design a protocol to help the SLAO to resolve this issue by spreading out uploads over a period of time. The following are the key assumptions and requirements. Assumptions: (A1) The size of the applications are large. (A2) All participants have X.509 digital certificates. Requirements: (R1) Applicants must generate their applications before the deadline but do not need to upload the applications by the deadline. Instead, the generated applications can be uploaded over a period of eight weeks after the deadline. (R2) Applicants must not be able to modify their applications after the deadline even if the applications have not been uploaded. (a) Provide a detailed description of your protocol by stating all steps and cryptographic operations/services that are used. State all other assumptions you need clearly in your answer. (b) Explain how your protocol can fulfill the stated requirements. In the following protocol, let N be a trusted third party, KXN be a pre-shared secret key between a user N and a user X, Rx be a nonce generated by X, and Ks be a session key. 1. XY: X|| Rx 2. Y N: Y|| Ry || EK (X || Rx) 3. 4. XY: EK NX: Ry || EK (Rx || Ks) || EK, (X|| Ks) XN Y: EK (X|| Ks) || EK, (Ry) YN (a) The objective of the protocol is to facilitate users X and Y to share a fresh secret key with each other. (i) Show that Ada, an attacker, can fool X into sharing with her a session key that X thinks has securely established with Y. (ii) Show that if the nonces and the session keys are of the same size, then Carol can fool Yinto sharing with her a session key that Ythinks has securely established with X (b) Modify the protocol to counter the attacks you have identified in (a) (i) and (a) (ii). 3. Explain how viruses might spread in computer systems in the following scenarios. (a) The Biba Integrity policy is adopted and (i) a virus is attached to a file at system low; (ii) a virus is attached to a file at system high. (b) The Bell-LaPadula policy is adopted and 1. 2. The Student Loan Application Office ("SLAO") of Country A's Government has decided to build an electronic student loan application submission system. After the system is built, SLAO will only accept applications electronically. One potential issue is that there will be a large number of uploads around the application deadline which imposes extremely heavy loading on the upload server. Design a protocol to help the SLAO to resolve this issue by spreading out uploads over a period of time. The following are the key assumptions and requirements. Assumptions: (A1) The size of the applications are large. (A2) All participants have X.509 digital certificates. Requirements: (R1) Applicants must generate their applications before the deadline but do not need to upload the applications by the deadline. Instead, the generated applications can be uploaded over a period of eight weeks after the deadline. (R2) Applicants must not be able to modify their applications after the deadline even if the applications have not been uploaded. (a) Provide a detailed description of your protocol by stating all steps and cryptographic operations/services that are used. State all other assumptions you need clearly in your answer. (b) Explain how your protocol can fulfill the stated requirements. In the following protocol, let N be a trusted third party, KXN be a pre-shared secret key between a user N and a user X, Rx be a nonce generated by X, and Ks be a session key. 1. XY: X|| Rx 2. Y N: Y|| Ry || EK (X || Rx) 3. 4. XY: EK NX: Ry || EK (Rx || Ks) || EK, (X|| Ks) XN Y: EK (X|| Ks) || EK, (Ry) YN (a) The objective of the protocol is to facilitate users X and Y to share a fresh secret key with each other. (i) Show that Ada, an attacker, can fool X into sharing with her a session key that X thinks has securely established with Y. (ii) Show that if the nonces and the session keys are of the same size, then Carol can fool Yinto sharing with her a session key that Ythinks has securely established with X (b) Modify the protocol to counter the attacks you have identified in (a) (i) and (a) (ii). 3. Explain how viruses might spread in computer systems in the following scenarios. (a) The Biba Integrity policy is adopted and (i) a virus is attached to a file at system low; (ii) a virus is attached to a file at system high. (b) The Bell-LaPadula policy is adopted and
Expert Answer:
Answer rating: 100% (QA)
The detailed answer for the above question is provided below Answer 1 Protocol for Spreading out Student Loan Application Uploads a Detailed Protocol Description Assumptions A1 Large application sizes ... View the full answer

Related Book For 

Posted Date:
Students also viewed these operating system questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Managing Scope Changes Case Study Scope changes on a project can occur regardless of how well the project is planned or executed. Scope changes can be the result of something that was omitted during...
-
Kenny operates a store, where he sells feed and other supplies to farmers. Heather purchases a $20,000 tractor from Kenny and pays Kenny with $18,000 in cash and $2,000 in corn. How much gross income...
-
On April 1, Adventures Travel Agency, Inc. began operations. The following transactions were completed during the month. 1. Issued common stock for $24,000 cash. 2. Obtained a bank loan for $7,000 by...
-
Save As a result of several mergers and acquisitions, stock in four companies has been distributed among the companies. Each row of the following table gives the percentage of stock in the four...
-
The cash flows associated with a project are shown below. The interest rate varies from year to year as shown. Determine an equivalent uniform annual series of cash flows. EOY Cash Flow Interest...
-
Knockoffs Unlimited, a nationwide distributor of low-cost imitation designer necklaces, has an exclusive franchise on the distribution of the necklaces, and sales have grown so rapidly over the past...
-
Let us consider a two-link mechanism shown in figure below. Assume that 91=0 and 92 = 45; a = a = 1; -(x,y) a. Determine the Jacobian matrix for this configuration. b. Calculate the Yoshikawa's...
-
Find the bond values or yields. Assume that the face value of the bonds is $1,000. (a) Consider a bond paying a coupon rate of 6% per year semiannually when the market interest rate is only 2.5% per...
-
prepare a relevant cost schedule showing the benefits of keeping the old lathe or buying the new one. Information about the old lathe: Cost $57,000 Estimated useful life 8 years Estimated residual...
-
Discuss the assumption that regular eye check-up, regular dental check-up and regular blood pleasure check-up are merit goods.?
-
What is GOD like, Not whether GOD is a deity, but how many and which one(s). How many, and which one(s). How do you know GOD? Does God care? And is God good? According to Kelly M. Kapic
-
Visa 1. Explain how partnership changes could impact progress in blockchain-related innovation for Visa. 2. How should Visa approach blockchain implementation? Should it focus on developing its...
-
Based of economics: 4 differences of characteristics each with examples difference between Ecommerce platform and accommodation difference between Healthcare and airlines
-
What energy levels are occupied in a complex such as hexacarbonylchromium (0)? Are any electrons placed into antibonding orbitals that are derived from the chromium d orbitals?
-
What are bounds and what do companies do with them?
-
All transactions involving Notes Payable and related accounts of Pearl Company during 2010 are as follows: Determine the amount of the transactions affecting financing activities and show how they...
-
Annas, Inc., has a $350,000, 4 percent bond issue that was issued a number of years ago at face value. There are now 10 years left on the bond issue, and the market increase rate is 8 percent....
-
Daize Corp. is analyzing a proposal to switch its factory over to a lights-out operation similar to the one discussed in this chapters Decision Point. To do so, it must acquire a fully automated...
-
On 1 April 2013 a business purchased a machine costing 112,000. The machine can be used for a total of 20,000 hours over an estimated life of 48 months. At the end of that time the machine is...
-
(a) The following trial balance was extracted from the books of M. Jackson on 30 April 2017. From it, and the note below it, prepare his statement of profit or loss for the year ending 30 April 2017,...
-
On 1 January 2015 a business purchased a laser printer costing 1,800. The printer has an estimated life of four years after which it will have no residual value. It is expected that the output from...

Study smarter with the SolutionInn App