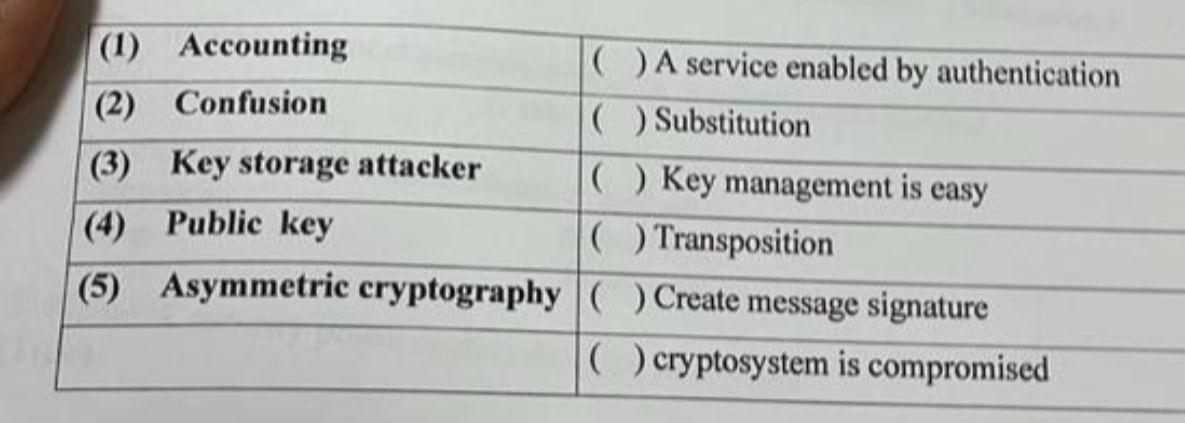
( ) A service enabled by authentication (1) Accounting (2) Confusion ( ) Substitution (3) Key...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
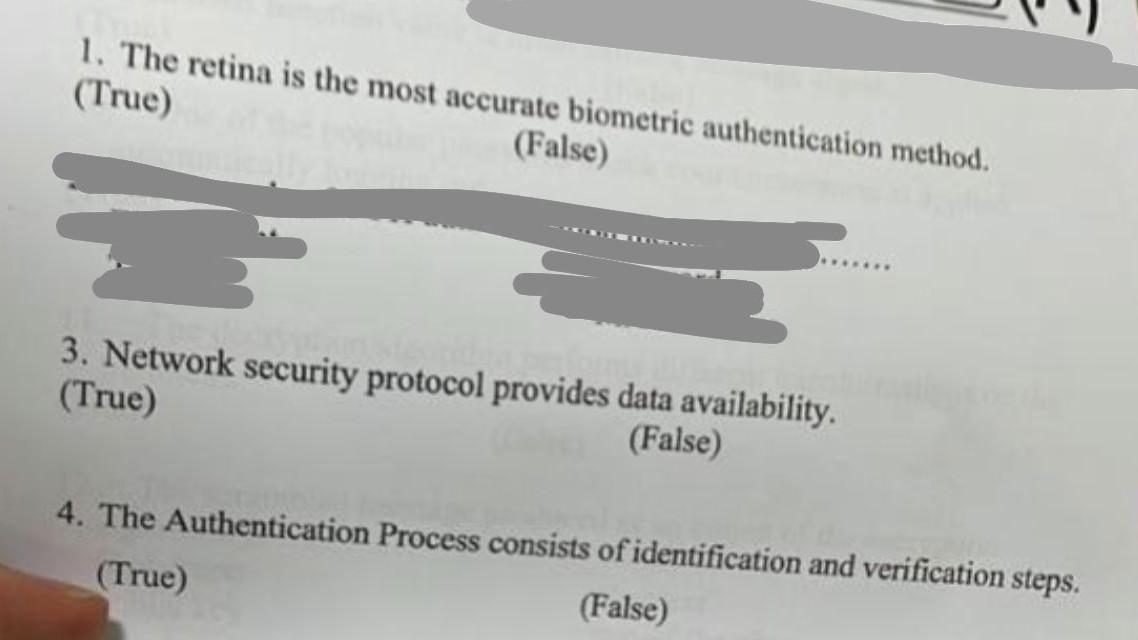
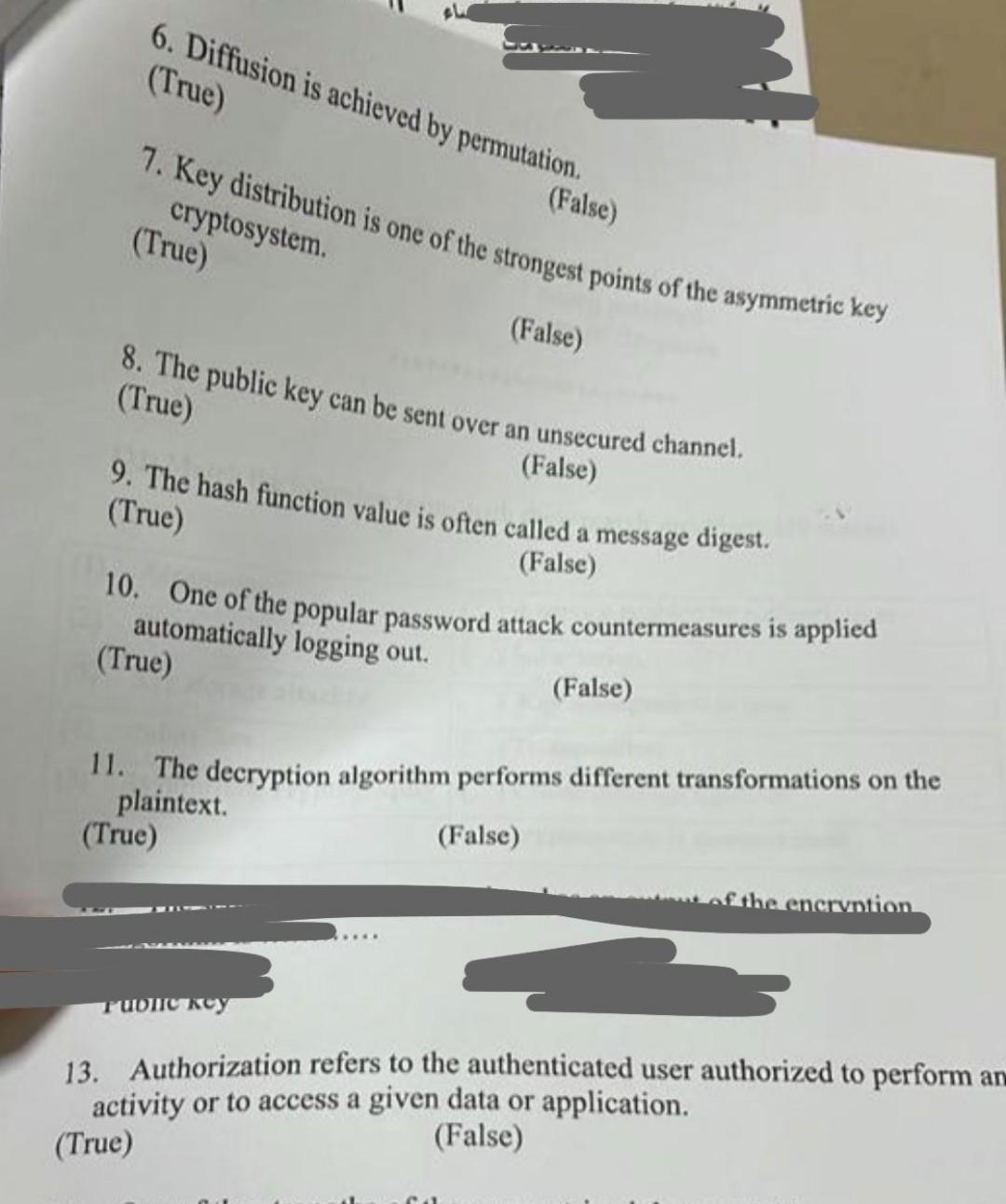
( ) A service enabled by authentication (1) Accounting (2) Confusion ( ) Substitution (3) Key storage attacker ( ) Key management is easy (4) Public key ( ) Transposition (5) Asymmetric cryptography ( ) Create message signature () cryptosystem is compromised 1. The retina is the most accurate biometric authentication method. (True) (False) 3. Network security protocol provides data availability. (True) (False) 4. The Authentication Process consists of identification and verification steps. (True) (False) 6. Diffusion is achieved by permutation. (True) 7. Key distribution is one of the strongest points of the asymmetric key cryptosystem. (True) (False) (False) 8. The public key can be sent over an unsecured channel. (True) (False) 9. The hash function value is often called a message digest. (True) (False) 10. One of the popular password attack countermeasures is applied automatically logging out. (True) Tublic key (False) 11. The decryption algorithm performs different transformations on the plaintext. (True) (False) encryption 13. Authorization refers to the authenticated user authorized to perform and activity or to access a given data or application. (True) (False) ( ) A service enabled by authentication (1) Accounting (2) Confusion ( ) Substitution (3) Key storage attacker ( ) Key management is easy (4) Public key ( ) Transposition (5) Asymmetric cryptography ( ) Create message signature () cryptosystem is compromised 1. The retina is the most accurate biometric authentication method. (True) (False) 3. Network security protocol provides data availability. (True) (False) 4. The Authentication Process consists of identification and verification steps. (True) (False) 6. Diffusion is achieved by permutation. (True) 7. Key distribution is one of the strongest points of the asymmetric key cryptosystem. (True) (False) (False) 8. The public key can be sent over an unsecured channel. (True) (False) 9. The hash function value is often called a message digest. (True) (False) 10. One of the popular password attack countermeasures is applied automatically logging out. (True) Tublic key (False) 11. The decryption algorithm performs different transformations on the plaintext. (True) (False) encryption 13. Authorization refers to the authenticated user authorized to perform and activity or to access a given data or application. (True) (False)
Expert Answer:
Answer rating: 100% (QA)
There i am providing the answer for all True and False The retina is the most accurate biometric authentication method Explanation False While the retina is considered a highly accurate biometric auth... View the full answer

Related Book For 

Accounting Information Systems The Crossroads of Accounting & IT
ISBN: 978-0132991322
2nd Edition
Authors: Donna Kay, Ali Ovlia
Posted Date:
Students also viewed these programming questions
-
1. Public keys are shared, usually by using _____ certificates A. public key B. private key C. symmetric D. root 2. _____ is a type of certificate that starts with an asterisk (*). It...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
In the late 1980s, various states and the US Congress debated placing limits on sulfur emissions to reduce the impact of acid rain. Utilities that generated electricity using coal-powered plants felt...
-
Atwater Corporation, a public corporation, reported a gain on fair value adjustment of $46,000 net of tax on its strategic investment reported at fair value, and a loss on fair value adjustment of...
-
Your comparison of the gross margin percent for Jones Drugs for the years 2016 through 2019 indicates a significant decline. This is shown by the following information: A discussion with Tanvi Anand,...
-
What specific methods did Europeans use to control and extract wealth from their colonies?
-
The actual and planned data for Underwater University for the Fall term 2014 were as follows: Registration, records, and marketing costs vary by the number of enrolled students, while instructional...
-
for the company Sedgwick What diagnostic model(s) might most closely relate to the organizational problem? Why? How will data about the problem be collected? One could use processes, statistics,...
-
AAA sold shares of a qualified small business corporation on August 29, 2021. He realized a capital gain of $64,000 on the sale. AAA has never claimed a capital gains deduction, he has never realized...
-
Regina and Greg adopted a baby boy in January 2023, and the total cost was $19,000 for qualified adoption costs (agency fees, attorney fees, etc.). Regina and Greg paid most of the expenses during...
-
Standard Investments Limited share repurchase - simultaneous and staggered. Standard Investments Limited has 42,000 ordinary shares which are held by the following shareholders: Roger Hampton ...
-
Moving to another question will save this response. Question 6
-
How did the three internal corporate governance mechanisms workor fail to workat Wells Fargo? Describe the organizational structure used by Wells Fargo. Do you think this structure could have...
-
A technician does maintenance work near the top of a communication tower, 88 m above the ground. The technician throws a screwdriver, giving it an initial downward velocity of 2.4 m/s. Neglect the...
-
Limited makes car parts for major car brands in Germany. They have a net operating income of 1.5 million. They have issued bonds worth 2 million paying 10 percent every year. They plan to borrow an...
-
A heat engine has a heat input of 3 Ã 104 Btu/h and a thermal efficiency of 40 percent. Calculate the power it will produce, in hp. Source 3 x 10 Btu/h 40% HE Sink
-
Discuss the role of accounting systems and business intelligence in assisting organizations to improve sustainability.
-
What are the three objectives of COSOs Internal ControlIntegrated Framework? Why are these important for internal control?
-
Why is knowledge of XBRL important to accounting professionals? Explain.
-
What is the pressure drop associated with water at \(27^{\circ} \mathrm{C}\) flowing with a mean velocity of \(0.1 \mathrm{~m} / \mathrm{s}\) through an \(800-\mathrm{m}-\) long cast iron pipe of...
-
Fully developed conditions are known to exist for water flowing through a \(50-\mathrm{mm}\)-diameter tube at \(0.02 \mathrm{~kg} / \mathrm{s}\) and \(27^{\circ} \mathrm{C}\). What is the maximum...
-
Water at \(35^{\circ} \mathrm{C}\) is pumped through a horizontal, \(200-\mathrm{m}\)-long, \(30-\mathrm{mm}\)-diameter tube at \(0.25 \mathrm{~kg} / \mathrm{s}\). Over time, a 2-mm-thick layer of...

Study smarter with the SolutionInn App