(1) Consider the extension of the One-time Pad cipher, where a ciphertext c is possibly longer...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
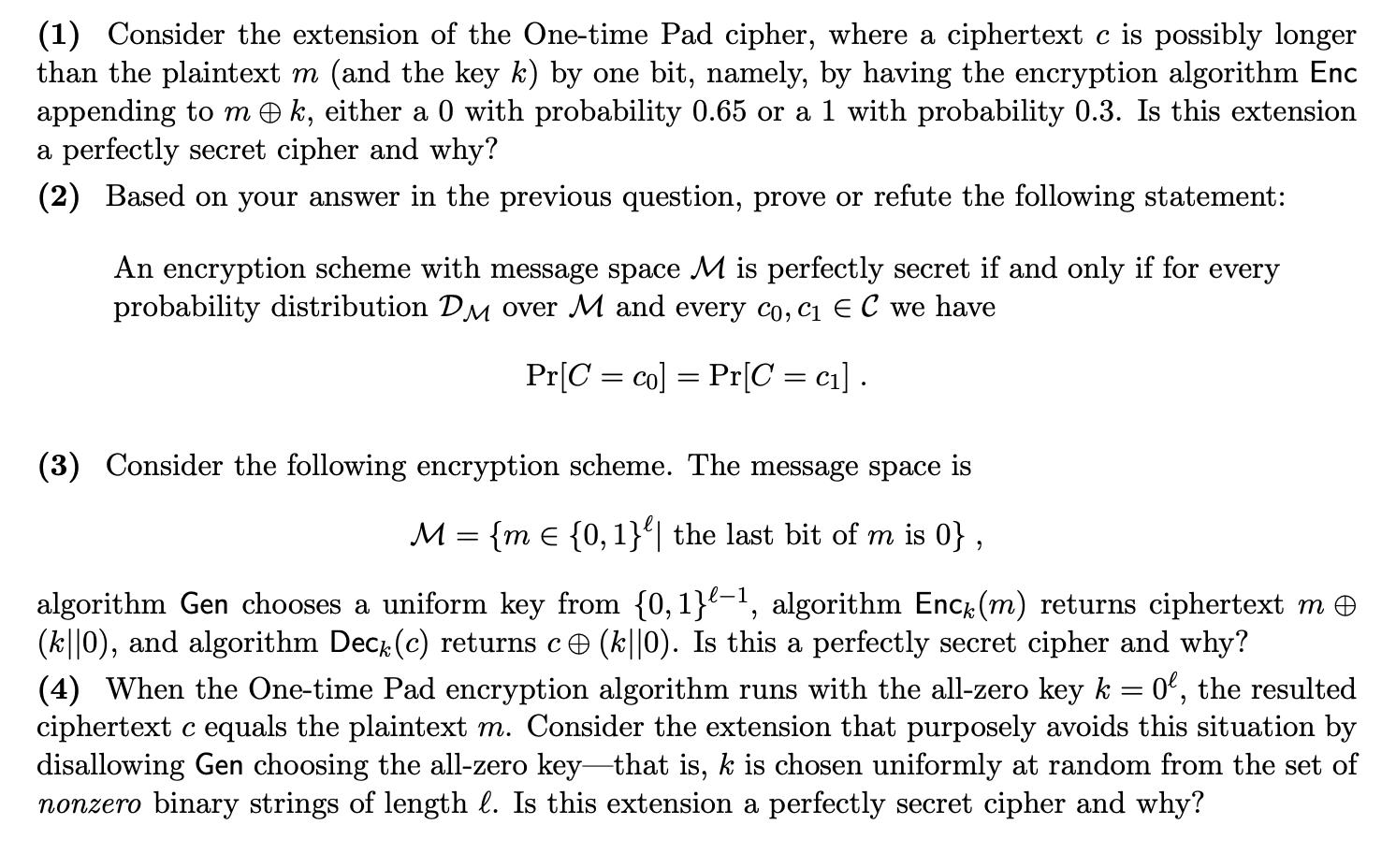
(1) Consider the extension of the One-time Pad cipher, where a ciphertext c is possibly longer than the plaintext m (and the key k) by one bit, namely, by having the encryption algorithm Enc appending to mk, either a 0 with probability 0.65 or a 1 with probability 0.3. Is this extension a perfectly secret cipher and why? (2) Based on your answer in the previous question, prove or refute the following statement: An encryption scheme with message space M is perfectly secret if and only if for every probability distribution DM over M and every co, c₁ E C we have Pr[C= co] Pr[C = c₁]. = (3) Consider the following encryption scheme. The message space is M = {m = {0, 1}| the last bit of m is 0}, algorithm Gen chooses a uniform key from {0,1}-¹, algorithm Enck (m) returns ciphertext m © (k||0), and algorithm Decê (c) returns c ℗ (k||0). Is this a perfectly secret cipher and why? (4) When the One-time Pad encryption algorithm runs with the all-zero key k = 0, the resulted ciphertext c equals the plaintext m. Consider the extension that purposely avoids this situation by disallowing Gen choosing the all-zero key-that is, k is chosen uniformly at random from the set of nonzero binary strings of length l. Is this extension a perfectly secret cipher and why? (1) Consider the extension of the One-time Pad cipher, where a ciphertext c is possibly longer than the plaintext m (and the key k) by one bit, namely, by having the encryption algorithm Enc appending to mk, either a 0 with probability 0.65 or a 1 with probability 0.3. Is this extension a perfectly secret cipher and why? (2) Based on your answer in the previous question, prove or refute the following statement: An encryption scheme with message space M is perfectly secret if and only if for every probability distribution DM over M and every co, c₁ E C we have Pr[C= co] Pr[C = c₁]. = (3) Consider the following encryption scheme. The message space is M = {m = {0, 1}| the last bit of m is 0}, algorithm Gen chooses a uniform key from {0,1}-¹, algorithm Enck (m) returns ciphertext m © (k||0), and algorithm Decê (c) returns c ℗ (k||0). Is this a perfectly secret cipher and why? (4) When the One-time Pad encryption algorithm runs with the all-zero key k = 0, the resulted ciphertext c equals the plaintext m. Consider the extension that purposely avoids this situation by disallowing Gen choosing the all-zero key-that is, k is chosen uniformly at random from the set of nonzero binary strings of length l. Is this extension a perfectly secret cipher and why?
Expert Answer:
Answer rating: 100% (QA)
Extension of Onetime Pad This extension is not a perfectly secret cipher In a perfectly secret ciphe... View the full answer

Related Book For 

Posted Date:
Students also viewed these computer network questions
-
In 1999, GLSEN identified that little was known about the school experiences of lesbian, gay, bisexual, transgender, and queer (LGBTQ+) youth and that LGBTQ+ youth were nearly absent from national...
-
The article notes that the hospital did not fully understand how its electronic health record system would estimate expected revenue. This was obviously happening at the hospital for some time. How...
-
Consider a repeated version of the game in exercise 24.5. In this version, we do not give all the proposal power to one person but rather imagine that the players are bargaining by making different...
-
Someone offered the investment options to Hendry on January 1, 2023: 1. Hendry has to save up to 5 times the initial deposit of US $ 150,000/year. 2. The savings cannot be taken for 20 years until...
-
(a) Find the slope of the tangent to the graph of f(x) at any point, (b) Find the slope of the tangent at the given point, (c) Write the equation of the line tangent to the graph of f(x) at the given...
-
From the following balance sheet accounts: a. Construct a balance sheet for 2010 and 2011 b. List all the working capital accounts c. Find the net working capital for the years ending 2010 and 2011...
-
Jerome Paper Company engaged you to review its internal control system. Jerome does not prelist cash receipts before they are recorded and has other weaknesses in processing collections of trade...
-
Derrald Pearl Company has two divisions, Computer Consulting and Construction. During the most recent year, the two divisions had the following operating data: Required: 1. Prepare a segment margin...
-
Consider a flywheel that is a solid cylindrical disk 0.2 meters in radius with a mass of 40 kg. The flywheel turns at 700 rpm until acceleration is applied by an external torque; in 6 seconds the...
-
Amadeus Corporation is considering the issue of a new product to be added to its product mix. They hired you, a recent business graduate from MacEwan, for conducting the analysis. The production line...
-
(a) What is horizontal communication? (6 marks) (b) How is the horizontal form of communication more prominent in Intermountain Healthcare? (4 marks)
-
(LO2) Sasha owns eight profitable rental properties and would like to shift some of this income to her children, Darius, age 17, and Delilah, age 11. Darius would be responsible for yard maintenance,...
-
(LO5) Theo, single, is the sole shareholder of Theo's Tool and Dye, Inc., a tool and dye manufacturing company operating as an \(S\) corporation. Theo reports qualified business income of \(\( \$ \)...
-
(LO2) a. Damian owns several stock investments that typically pay out dividend income quarterly. He uses direct deposit and receives a \(\( \$ \) 1,000\) payment in his account on December 31, Year...
-
(LO3) Janessa sold a rental apartment building for \(\( \$ \) 1.2\) million that had an adjusted basis of \(\( \$ \) 600,000\). The purchaser agreed to pay her \(\( \$ \) 300,000\) cash now and make...
-
(LO3) In late November, Year 4, Javi received \(\( \$ \) 4,050\) in advance from a customer for monthly painting lessons that were to begin in December, Year 4 and run through May, Year 6. When must...
-
Find an equation of the tangent plane and an equation of the normal line to the level surface of f(x, y, z) = x - y + e passing through the point ((1,1,0)
-
How can a promoter avoid personal liability for pre-incorporation contracts?
-
In the ring topology in Figure 1.7, what happens if one of the stations is unplugged? Figure 1.7 Repeater Repeater Repeater |Repeater Repeater Repeater
-
Referring to the CRC-8 in Table 5.4, answer the following questions: a. Does it detect a single error? Defend your answer. b. Does it detect a burst error of size 6? Defend your answer. c. What is...
-
Write a statement in Java to create a socket address bound to the local host and the HTTP server process.
-
A healthy diet is becoming increasingly important for consumers, especially women aged 2535. As a result, they are taking active steps to ensure they are eating healthy but are also looking for other...
-
Lael was just hired by Best East Motels into their manager training program and was excited about the potential benefits after her graduation from Florida State University. Working part-time and...
-
Sophie just completed a sales training course with one of the firms most productive sales representatives, Emma. At the end of the first week, Sophie and Emma sat in a motel room filling out their...

Study smarter with the SolutionInn App


