1. In cybersecurity, a threat actor is an individual or an entity responsible for cyber incidents...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
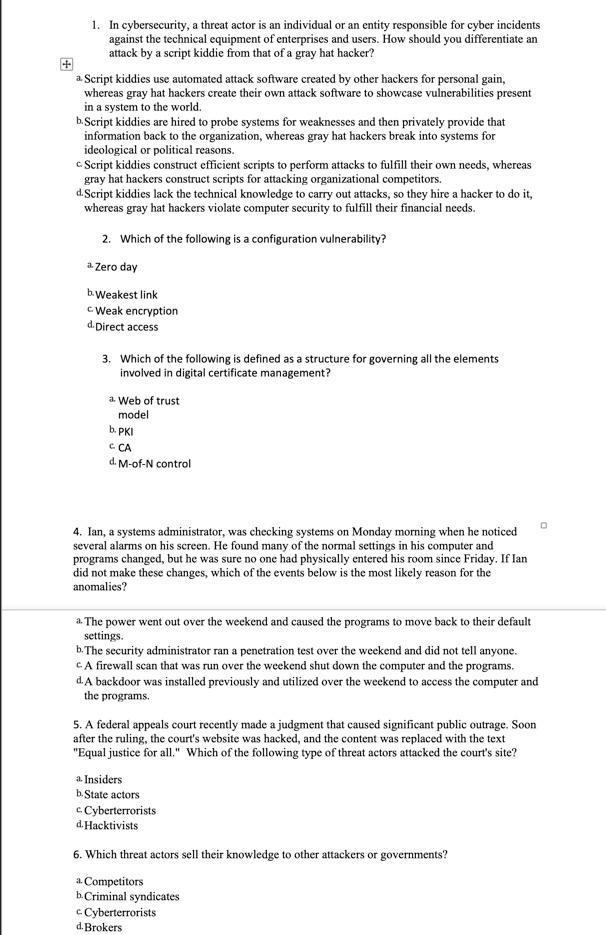
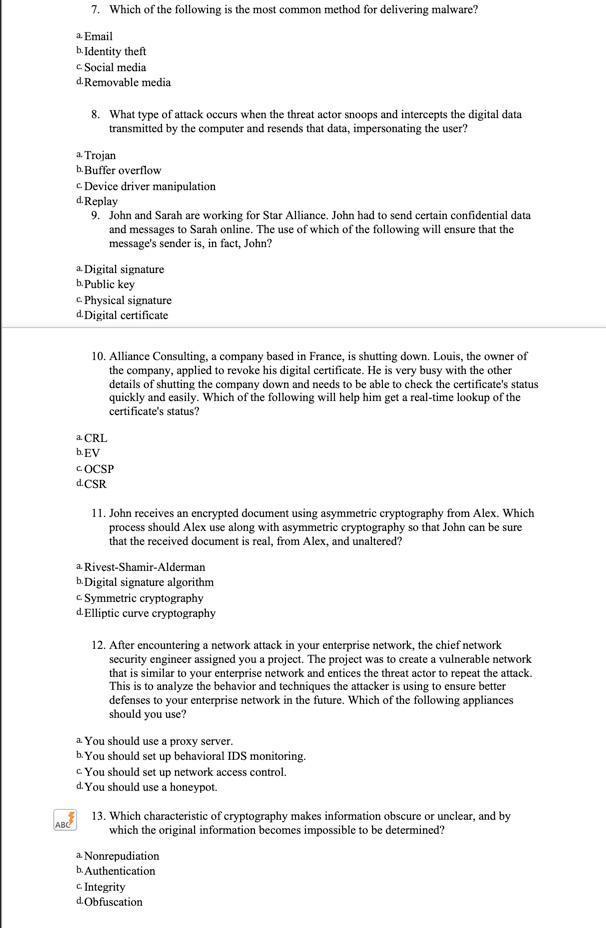
1. In cybersecurity, a threat actor is an individual or an entity responsible for cyber incidents against the technical equipment of enterprises and users. How should you differentiate an attack by a script kiddie from that of a gray hat hacker? a. Script kiddies use automated attack software created by other hackers for personal gain, whereas gray hat hackers create their own attack software to showcase vulnerabilities present in a system to the world. b. Script kiddies are hired to probe systems for weaknesses and then privately provide that information back to the organization, whereas gray hat hackers break into systems for ideological or political reasons. c Script kiddies construct efficient scripts to perform attacks to fulfill their own needs, whereas gray hat hackers construct scripts for attacking organizational competitors. d.Script kiddies lack the technical knowledge to carry out attacks, so they hire a hacker to do it, whereas gray hat hackers violate computer security to fulfill their financial needs. 2. Which of the following is a configuration vulnerability? a Zero day b. Weakest link cWeak encryption d.Direct access 3. Which of the following is defined as a structure for governing all the elements involved in digital certificate management? a. Web of trust model b. PKI C CA d. M-of-N control 4. Ian, a systems administrator, was checking systems on Monday morning when he noticed several alarms on his screen. He found many of the normal settings in his computer and programs changed, but he was sure no one had physically entered his room since Friday. If Ian did not make these changes, which of the events below is the most likely reason for the anomalies? a. The power went out over the weekend and caused the programs to move back to their default settings. b. The security administrator ran a penetration test over the weekend and did not tell anyone. CA firewall scan that was run over the weekend shut down the computer and the programs. d. A backdoor was installed previously and utilized over the weekend to access the computer and the programs. 5. A federal appeals court recently made a judgment that caused significant public outrage. Soon after the ruling, the court's website was hacked, and the content was replaced with the text "Equal justice for all." Which of the following type of threat actors attacked the court's site? a Insiders b. State actors cCyberterrorists d.Hacktivists 6. Which threat actors sell their knowledge to other attackers or governments? a. Competitors b. Criminal syndicates c Cyberterrorists d. Brokers ABC 7. Which of the following is the most common method for delivering malware? a Email b. Identity theft c Social media d.Removable media 8. What type of attack occurs when the threat actor snoops and intercepts the digital data transmitted by the computer and resends that data, impersonating the user? a Trojan b. Buffer overflow c Device driver manipulation d. Replay 9. John and Sarah are working for Star Alliance. John had to send certain confidential data and messages to Sarah online. The use of which of the following will ensure that the message's sender is, in fact, John? a Digital signature b. Public key C c. Physical signature d.Digital certificate 10. Alliance Consulting, a company based in France, is shutting down. Louis, the owner of the company, applied to revoke his digital certificate. He is very busy with the other details of shutting the company down and needs to be able to check the certificate's status quickly and easily. Which of the following will help him get a real-time lookup of the certificate's status? a CRL b. EV COCSP d.CSR 11. John receives an encrypted document using asymmetric cryptography from Alex. Which process should Alex use along with asymmetric cryptography so that John can be sure that the received document is real, from Alex, and unaltered? a Rivest-Shamir-Alderman b. Digital signature algorithm c Symmetric cryptography d.Elliptic curve cryptography 12. After encountering a network attack in your enterprise network, the chief network security engineer assigned you a project. The project was to create a vulnerable network that is similar to your enterprise network and entices the threat actor to repeat the attack. This is to analyze the behavior and techniques the attacker is using to ensure better defenses to your enterprise network in the future. Which of the following appliances should you use? a You should use a proxy server. b. You should set up behavioral IDS monitoring. c. You should set up network access control. d. You should use a honeypot. 13. Which characteristic of cryptography makes information obscure or unclear, and by which the original information becomes impossible to be determined? a Nonrepudiation b. Authentication c. Integrity d.Obfuscation 1. In cybersecurity, a threat actor is an individual or an entity responsible for cyber incidents against the technical equipment of enterprises and users. How should you differentiate an attack by a script kiddie from that of a gray hat hacker? a. Script kiddies use automated attack software created by other hackers for personal gain, whereas gray hat hackers create their own attack software to showcase vulnerabilities present in a system to the world. b. Script kiddies are hired to probe systems for weaknesses and then privately provide that information back to the organization, whereas gray hat hackers break into systems for ideological or political reasons. c Script kiddies construct efficient scripts to perform attacks to fulfill their own needs, whereas gray hat hackers construct scripts for attacking organizational competitors. d.Script kiddies lack the technical knowledge to carry out attacks, so they hire a hacker to do it, whereas gray hat hackers violate computer security to fulfill their financial needs. 2. Which of the following is a configuration vulnerability? a Zero day b. Weakest link cWeak encryption d.Direct access 3. Which of the following is defined as a structure for governing all the elements involved in digital certificate management? a. Web of trust model b. PKI C CA d. M-of-N control 4. Ian, a systems administrator, was checking systems on Monday morning when he noticed several alarms on his screen. He found many of the normal settings in his computer and programs changed, but he was sure no one had physically entered his room since Friday. If Ian did not make these changes, which of the events below is the most likely reason for the anomalies? a. The power went out over the weekend and caused the programs to move back to their default settings. b. The security administrator ran a penetration test over the weekend and did not tell anyone. CA firewall scan that was run over the weekend shut down the computer and the programs. d. A backdoor was installed previously and utilized over the weekend to access the computer and the programs. 5. A federal appeals court recently made a judgment that caused significant public outrage. Soon after the ruling, the court's website was hacked, and the content was replaced with the text "Equal justice for all." Which of the following type of threat actors attacked the court's site? a Insiders b. State actors cCyberterrorists d.Hacktivists 6. Which threat actors sell their knowledge to other attackers or governments? a. Competitors b. Criminal syndicates c Cyberterrorists d. Brokers ABC 7. Which of the following is the most common method for delivering malware? a Email b. Identity theft c Social media d.Removable media 8. What type of attack occurs when the threat actor snoops and intercepts the digital data transmitted by the computer and resends that data, impersonating the user? a Trojan b. Buffer overflow c Device driver manipulation d. Replay 9. John and Sarah are working for Star Alliance. John had to send certain confidential data and messages to Sarah online. The use of which of the following will ensure that the message's sender is, in fact, John? a Digital signature b. Public key C c. Physical signature d.Digital certificate 10. Alliance Consulting, a company based in France, is shutting down. Louis, the owner of the company, applied to revoke his digital certificate. He is very busy with the other details of shutting the company down and needs to be able to check the certificate's status quickly and easily. Which of the following will help him get a real-time lookup of the certificate's status? a CRL b. EV COCSP d.CSR 11. John receives an encrypted document using asymmetric cryptography from Alex. Which process should Alex use along with asymmetric cryptography so that John can be sure that the received document is real, from Alex, and unaltered? a Rivest-Shamir-Alderman b. Digital signature algorithm c Symmetric cryptography d.Elliptic curve cryptography 12. After encountering a network attack in your enterprise network, the chief network security engineer assigned you a project. The project was to create a vulnerable network that is similar to your enterprise network and entices the threat actor to repeat the attack. This is to analyze the behavior and techniques the attacker is using to ensure better defenses to your enterprise network in the future. Which of the following appliances should you use? a You should use a proxy server. b. You should set up behavioral IDS monitoring. c. You should set up network access control. d. You should use a honeypot. 13. Which characteristic of cryptography makes information obscure or unclear, and by which the original information becomes impossible to be determined? a Nonrepudiation b. Authentication c. Integrity d.Obfuscation
Expert Answer:
Answer rating: 100% (QA)
1 The correct answer is a Script kiddies use automated attack software created by other hackers for personal gain whereas gray hat hackers create their own attack software to showcase vulnerabilities ... View the full answer

Related Book For 

Auditing and Assurance services an integrated approach
ISBN: 978-0134065823
16th edition
Authors: Alvin A. Arens, Randal J. Elder, Mark S. Beasley, Chris E. Hogan
Posted Date:
Students also viewed these accounting questions
-
Managing Scope Changes Case Study Scope changes on a project can occur regardless of how well the project is planned or executed. Scope changes can be the result of something that was omitted during...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Googles ease of use and superior search results have propelled the search engine to its num- ber one status, ousting the early dominance of competitors such as WebCrawler and Infos- eek. Even later...
-
Describe the graphs of the equation. x 2 + y 2 3
-
In the discussion of motional emf (Sect. 7.1.3) I assumed that the wire loop (Fig. 7.10) has a resistance R; the current generated is then I = vBh/R. But what if the wire is made out of perfectly...
-
Convert the power spectra of Figure 9.57 to onesided equivalent spectra that are functions of cyclic frequency \((\mathrm{Hz})\). (a) Sxx(00) -We So (b) Sxx() So rad/s rad's 00002 -002-00 Figure...
-
Good Times Express Company had retained earnings of \(\$ 160\) million at December 31, 2006. The company reported these figures for 2007: Requirement Beginning with net income, prepare a combined...
-
Assume that Revolights was interested in working with strategic partners in order to enhance the firms success. What types of companies might Revolights partner with to become more successful?
-
In nonprofit organizations, leadership is critical for sustainable funding. The reputation of the organization, and often of the Executive Director can make a difference in the level of funding...
-
Enter a lookup function in cell E5 that returns the tax deduction amount for the number of dependents listed in the cell C5. Use the table in range H13:I17 to complete the function. The maximum...
-
What is meant by Open Source Software (OSS)? Explain some popular Open Source operating systems.
-
Why is a decreasing sales-to-PPE ratio a signal of possible overstatement of assets?
-
An increase in current liabilities as a percentage of current assets or of sales is a sign of an understatement of expenses. True/False
-
WorldCom is presented in this textbook as an illustration of overstating earnings by: (a) Holding books open after the close of a reporting period. (b) Misuse of multiple element contracts. (c)...
-
One mole of CO is initially contained on one-half of a well-insulated, rigid tank. Its temperature is 500 K. The other half of the tank is initially at vacuum. A diaphragm separates the two...
-
Lockheeds accounting tale is the classic case of misstating earnings by failing to write off an impaired asset. True/False
-
Why do you think the Google My Business listing is a popular tool for people who use Google to find a business? What are some ways that a medical administrator could optimize their Google My...
-
Consider a closed, rigid tank with a volume of 0.8L, filled with cold water initially at 27C. The tank is filled such that there are no voids (air pockets) within. The initial pressure within the...
-
Indicate the four phases of the audit process. In which phase does the auditor perform tests of controls?
-
Explain how the increased use of fair value accounting might increase information risk.
-
This problem requires you to research the disclosure requirements for fixed assets using the FASB Codification at www.fasb.org. Access to the FASB Codification requires that your educational...
-
Can we use any trial vector \(\vec{X}_{1}\) in the matrix iteration method to find the largest natural frequency?
-
Rayleigh's method a. Finds the natural frequencies and mode shapes of the system, one at a time, using several trial values for each frequency. b. Finds all the natural frequencies using trial...
-
Fill in the Blank. For a shaft carrying masses \(m_{1}, m_{2}, \ldots\), Rayleigh's method gives the natural frequency as \[\omega=\left\{\frac{g\left(m_{1} w_{1}+m_{2} w_{2}+\cdots ight)}{m_{1}...

Study smarter with the SolutionInn App