1. Read the initial configuration of the network to implement Access Control List. Initial Configuration Configure...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
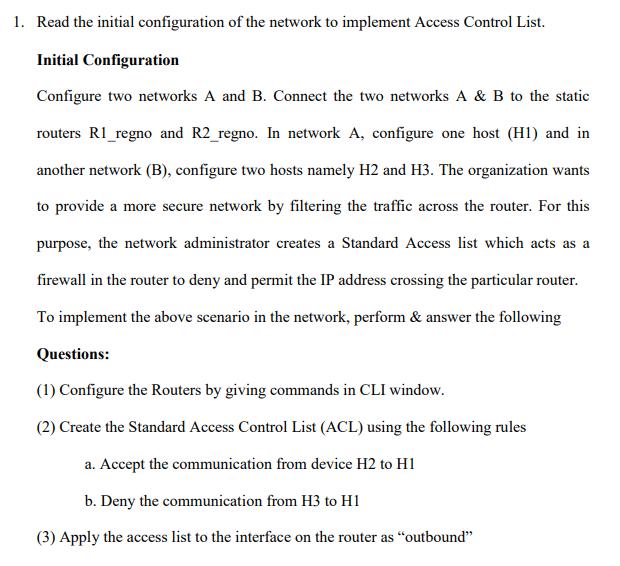
1. Read the initial configuration of the network to implement Access Control List. Initial Configuration Configure two networks A and B. Connect the two networks A & B to the static routers R1_regno and R2_regno. In network A, configure one host (H1) and in another network (B), configure two hosts namely H2 and H3. The organization wants to provide a more secure network by filtering the traffic across the router. For this purpose, the network administrator creates a Standard Access list which acts as a firewall in the router to deny and permit the IP address crossing the particular router. To implement the above scenario in the network, perform & answer the following Questions: (1) Configure the Routers by giving commands in CLI window. (2) Create the Standard Access Control List (ACL) using the following rules a. Accept the communication from device H2 to H1 b. Deny the communication from H3 to H1 (3) Apply the access list to the interface on the router as "outbound" 1. Read the initial configuration of the network to implement Access Control List. Initial Configuration Configure two networks A and B. Connect the two networks A & B to the static routers R1_regno and R2_regno. In network A, configure one host (H1) and in another network (B), configure two hosts namely H2 and H3. The organization wants to provide a more secure network by filtering the traffic across the router. For this purpose, the network administrator creates a Standard Access list which acts as a firewall in the router to deny and permit the IP address crossing the particular router. To implement the above scenario in the network, perform & answer the following Questions: (1) Configure the Routers by giving commands in CLI window. (2) Create the Standard Access Control List (ACL) using the following rules a. Accept the communication from device H2 to H1 b. Deny the communication from H3 to H1 (3) Apply the access list to the interface on the router as "outbound"
Expert Answer:
Answer rating: 100% (QA)
To implement the access control list ACL rules in the network scenario you provided you can configur... View the full answer

Related Book For 

Principles of Information Systems
ISBN: 978-0324665284
9th edition
Authors: Ralph M. Stair, George W. Reynolds
Posted Date:
Students also viewed these computer network questions
-
Laval produces lighting fixtures. Budgeted information for its two production departments follows. The departments use machine hours (MH) and direct labor hours (DLH). Overhead cost Fabricating $...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Case Study: Quick Fix Dental Practice Technology requirements Application must be built using Visual Studio 2019 or Visual Studio 2017, professional or enterprise. The community edition is not...
-
For OEM & Aftermarket Parts Distribution Companies (reference an example company) Describe the sales presentation method: Salesperson to buyer? Salesperson to buyer to group? Sales team to buyer...
-
The beam of light from a laser on a rotating turntable casts into space. At some distance, the beam moves across space faster than c. Why doesn't this contradict relativity?
-
A 15° wedge is forced under a 50-kg pipe as shown. Knowing that the coefficient of static friction at both surfaces of the wedge is 0.20, determine the largest coefficient of static friction...
-
I think there should be no back-up to prevent a bank from failing or to protect depositors if it does fail. Let the market decide these things. People should be careful about where they deposit their...
-
Your employer engages in numerous joint processes that produce significant quantities and types of by-product. You have been asked to give a report to management on the best way to account for...
-
Ben and Eileen went on a field trip with some freinds, some of whom had a cold. The probability that Ben will catch the cold is 0 . 0 9 and the probability that Eileen will catch the cold is 0 . 2 1...
-
Research the Internet for recent litigation, censures, and fines involving national public accounting firms. Examples of litigation cases against national public accounting firms include fines by...
-
one day 104 teachers were sick with the flu. if this was 52% of the total number of teachers how many teachers were there altogether
-
What are the emerging trends and challenges in the field of structural engineering, particularly in the context of designing resilient and adaptive structures capable of withstanding extreme...
-
Five Star Corporation will pay a dividend of $ 2 . 9 0 per share next year. The company pledges to increase its dividend by 4 percent per year indefinitely. If you require a return of 1 1 percent on...
-
Stock A's beta is 0.92. Stock B's expected return is 8.8%. The risk free rate is 4% and the market risk premium is 6%. What are the beta and expected return of a portfolio that invests 25% of its...
-
Can you elaborate on the principles and methodologies employed in the design and optimization of transportation networks to improve efficiency, safety, and environmental sustainability ?
-
Suppose that the only competing suppliers of Internet services are NewServices and RealWest. At present, they each have 50% of the market share in their community. However, NewServices is upgrading...
-
Stuart Company has provided the following for the year. Budget Sales $502,000 Variable product costs 187,000 Variable selling expense 49,000 Other variable expenses 3,200 Fixed product costs Fixed...
-
Explain the Hawthorne effect.
-
How could you use creative analysis to help you develop a better information system for your college or university?
-
Based in Ankara, Turkey, Aselsan is the largest military electronics manufacturer in Turkey. The company is divided into four divisions: Communications (HC), Radar, Electronic Warfare and...
-
How does the JAD technique support the RAD systems development life cycle?
-
Perkins Appliance & Furniture Company has two departments, appliances and furniture. Operating information for 2016 appears below. Common operating expenses of the firm were \($180,000\) . Required...
-
The cutting department of Liberty Manufacturing Company operated during September 2016 with the following manufacturing overhead cost budget based on 6,000 hours of monthly productive capacity: The...
-
The following information was obtained from the ledger of Stillwell Emporium, Inc., at the end of 2016: Stillwell analyzes its operating expenses at the end of each period in order to prepare an...

Study smarter with the SolutionInn App