2. Consider the following certificate mechanism. X.509 Certificate Structures Version Serial Number Algorithm identifier: Algorithm Parameters...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
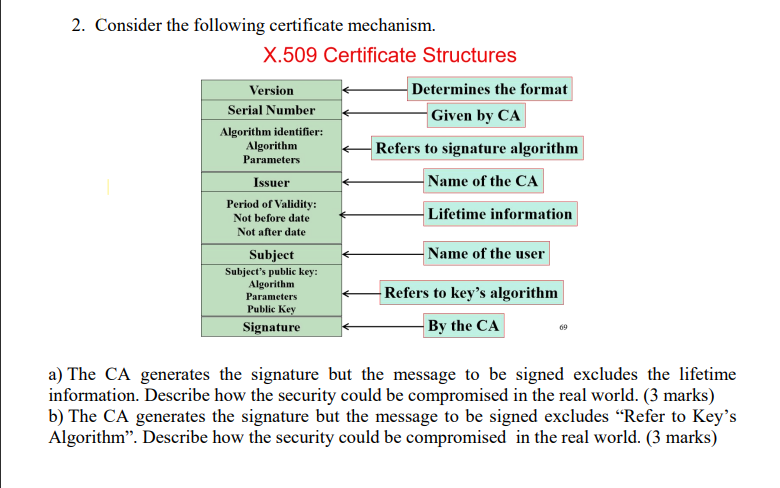
2. Consider the following certificate mechanism. X.509 Certificate Structures Version Serial Number Algorithm identifier: Algorithm Parameters Issuer Period of Validity: Not before date Not after date Subject Subject's public key: Algorithm Parameters Public Key Signature Determines the format Given by CA Refers to signature algorithm Name of the CA Lifetime information Name of the user -Refers to key's algorithm By the CA 69 a) The CA generates the signature but the message to be signed excludes the lifetime information. Describe how the security could be compromised in the real world. (3 marks) b) The CA generates the signature but the message to be signed excludes "Refer to Key's Algorithm". Describe how the security could be compromised in the real world. (3 marks) 2. Consider the following certificate mechanism. X.509 Certificate Structures Version Serial Number Algorithm identifier: Algorithm Parameters Issuer Period of Validity: Not before date Not after date Subject Subject's public key: Algorithm Parameters Public Key Signature Determines the format Given by CA Refers to signature algorithm Name of the CA Lifetime information Name of the user -Refers to key's algorithm By the CA 69 a) The CA generates the signature but the message to be signed excludes the lifetime information. Describe how the security could be compromised in the real world. (3 marks) b) The CA generates the signature but the message to be signed excludes "Refer to Key's Algorithm". Describe how the security could be compromised in the real world. (3 marks)
Expert Answer:

Related Book For 

Income Tax Fundamentals 2013
ISBN: 9781285586618
31st Edition
Authors: Gerald E. Whittenburg, Martha Altus Buller, Steven L Gill
Posted Date:
Students also viewed these computer network questions
-
can someone solve this Modern workstations typically have memory systems that incorporate two or three levels of caching. Explain why they are designed like this. [4 marks] In order to investigate...
-
"internet radios" for streaming audio, and personal video recorders and players. Describe design and evaluation processes that could be used by a start-up company to improve the usability of such...
-
You use the following data to calculate your stock value. Assume you use the historical geometric average growth rate (rounded to 2 decimals) for initial growth rate for 4 years. Then you believe it...
-
Describe the product life cycle. How do unit-level costs behave in relation to the product life cycle? Batch-level costs? Product-level costs? Facility-level costs?
-
In the ChiliToGo program in Exercise 12, the costs to produce an adult meal and a childs meal are $4.35 and $3.10, respectively. Modify the ChiliToGo program to display the total profit for each type...
-
In 2014, Barker contacted Price about a van Price had advertised for sale. The advertisement described the van as a 1994 Ford E350. Barker and Price agreed to meet, and, on April 9, Barker inspected...
-
Gammaro Company uses normal costing. It allocates manufacturing overhead costs using a budgeted rate per machine-hour. The following data are available for 2011: Budgeted manufacturing overhead costs...
-
Knowing the specific heat of ice and water is 2.05KJ/kg o C and 4.18kJ/kgC. What is the heat needed to change 2kg of ice at -20 C into 100 C water?
-
1. Write Java statements for following. (a) Declared a variable named d and assigned the value of 35. (b) Declared a constant named f and assigned the value of 3.14.
-
A random sample of 75 observations from a population yielded the following summary statistics: Construct a 95 % confidence interval for the population mean m. x=1,270 x = 21,520
-
From time to time, managers may be faced with the need to change the internal rules of the game within their MNE. What skills and capabilities may be useful in achieving this?
-
The data entry operation in a large computer department claims that it gives its customers a turnaround time of 6.0 h or less. To test this claim, one of the customers took a sample of 36 jobs and...
-
Find the probability that an exponentially distributed random variable X with mean 1/ = 8 will take on the values: (a) Between 2 and 7 (b) Less than 9 (c) Greater than 6 (d) Between 1 and 15
-
A survey of low-income families in New Jersey was designed to determine the average heating costs for a family of 4 during January and February. Heating costs are known to have a standard deviation...
-
Implement the same Playfair Cipher from P1. Both encryption and decryption are required. This implementation is required to work on letters only. (You can use numbers, e.g., ASCII for the actual...
-
"Standard-cost procedures are particularly applicable to process-costing situations." Do you agree? Why?
-
Jenny earns $34,500 in 2012. Calculate the FICA tax that must be paid by: Jenny: ..............................Soc,Sec. ..................$______________...
-
In 2012, Lou has a salary of $54,000 from her job. She also has interest income of $1,700. Lou is single and has no dependents. During the year, Lou sold silver coins held as an investment for a...
-
Sophie is a single taxpayer. For the first payroll period in October 2012, she is paid wages of $3,250 monthly. Sophie claims three allowances on her Form W-4. a. Use the percentage method to...
-
A surface with \(N_{0}\) adsorption centers has \(N\left(\leq N_{0}ight)\) gas molecules adsorbed on it. Show that the chemical potential of the adsorbed molecules is given by \[ \mu=k T \ln...
-
Assuming that the latent heat of vaporization of water \(L_{\mathrm{V}}=2260 \mathrm{~kJ} / \mathrm{kg}\) is independent of temperature and the specific volume of the liquid phase is negligible...
-
Define a quantity \(J\) as \[ J=E-N \mu=T S-P V \] Show that for a system in the grand canonical ensemble \[ \overline{(\Delta J)^{2}}=k T^{2} C_{V}+\left\{\left(\frac{\partial U}{\partial...

Study smarter with the SolutionInn App


