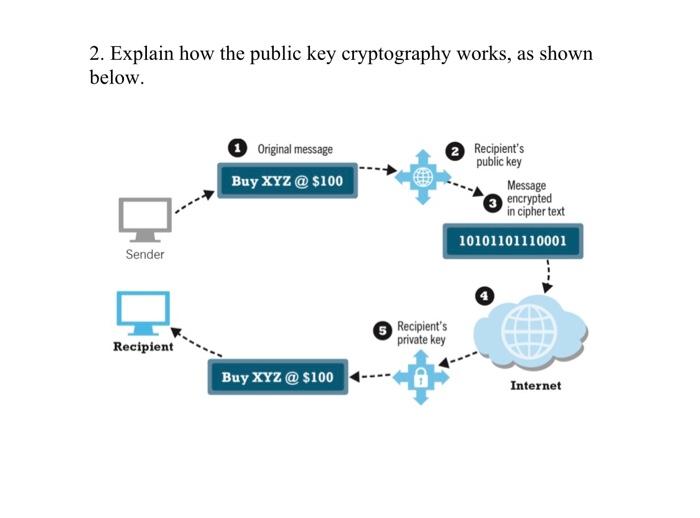
2. Explain how the public key cryptography works, as shown below. Sender Recipient Original message Buy...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
2. Explain how the public key cryptography works, as shown below. Sender Recipient Original message Buy XYZ @ $100 Buy XYZ @ $100 Recipient's private key Recipient's public key Message encrypted in cipher text 10101101110001 Internet 2. Explain how the public key cryptography works, as shown below. Sender Recipient Original message Buy XYZ @ $100 Buy XYZ @ $100 Recipient's private key Recipient's public key Message encrypted in cipher text 10101101110001 Internet
Expert Answer:
Answer rating: 100% (QA)
Public key cryptography also known as asymmetric cryptography is a method of encrypting and decrypti... View the full answer

Related Book For 

Posted Date:
Students also viewed these operating system questions
-
can someone solve this Modern workstations typically have memory systems that incorporate two or three levels of caching. Explain why they are designed like this. [4 marks] In order to investigate...
-
1. Unlike a Certification Authority (CA), a/an _____ does not issue certificates. A. Web of trust B. Key escrow C. Registration Authority (RA) D. Public key 2. _____ contains the...
-
Given, R = 192 R = 22 C=2F C=4F (1) V www R www R R R C The time constants (in S) for the circuits I, II, III are respectively (A) 18, 8/9, 4 (C) 4, 8/9, 18 (II) (B) 18, 4, 8/9 (D) 8/9, 18, 4 R3 (III)
-
Describe the five major formats used for reports. Be prepared to discuss each.
-
You can obtain the pH of a 0.100 M HCl solution by assuming that all of the H3O+ ion comes from the HCl, in which case the pH equals log 0.100 = 1.00. But if you want the pH of a solution that is...
-
Water is flowing through a long pipe of diameter \(15 \mathrm{~cm}\) at \(300 \mathrm{~K}\). The pressure gradient is \(500 \mathrm{~Pa} / \mathrm{m}\). Using the Blasius equation for the friction...
-
Minelli Enterprises uses large amounts of copper in the manufacture of ceiling fans. The firm has been very concerned about the detrimental impact of rising copper prices on its earnings and has...
-
Lowe's is a leading retailer in the home improvement field. Complete the component percentage analysis on the company's income statement that follows. (Enter your answer as a percentage rounded to 2...
-
The Sally Coffee Shop is considering closing one hour earlier in the evening through the week. Sally obtained the following data from a study taken last week of the number of customers between the...
-
Quote a sentence from the link below that stood out to you. Be sure to properly punctuate it and cite it. Tell why this quote stood out to you. in one or more sentences. link:...
-
Taking a sip of coffee one day, you start thinking about the effort it takes to do so. Your forearm is a type of lever. As shown in Figure P9.79, the biceps muscle is attached to the forearm bone...
-
H a : 877, n = 90, x = 921, = 52. Find the value of the standard score, z, and determine whether the alternative hypothesis is supported at a 0.05 significance level.
-
A \(0.075-\mathrm{kg}\) disk initially at rest in the Earth reference frame is free to move parallel to a horizontal bar through a hole at the disk's center. The disk is struck face-on by a...
-
H 0 : The defendant is not guilty. Ha: The defendant is guilty. Without using the terms null hypothesis and alternative hypothesis, identify the type I error and identify the type II error.
-
Using a search engine such as Google, search for power of a hypothesis test. Describe what the power of a hypothesis test is.
-
A.BREAK EVEN POINT: a.Calcular el COSTO FIJO de la empresa si las unidades producidas y vendidas son 300,000, el costo variable es de $60.00 y se vende a $.80.00. b.Cuntas unidades debe producir la...
-
Comptech Ltd is a manufacturer of optical equipment. In September 2019, Ed Thompson the Chief Research Officer, attended a conference in Switzerland that focused on optical developments for the 21st...
-
What entities constitute a full-service Kerberos environment?
-
a. What is {01} -1 in GF(2 8 )? b. Verify the entry for {01} in the S-box.
-
Consider the threat of theft/breach of proprietary or confidential information held in key data files on the system. One method by which such a breach might occur is the accidental/deliberate...
-
See Table 2.5 showing financial statement data and stock price data for Mydeco Corp. a. How did Mydecos book debt-equity ratio change from 2019 to 2023? b. How did Mydecos market debt-equity ratio...
-
See Table 2.5 showing financial statement data and stock price data for Mydeco Corp. a. Compute Mydecos PE ratio each year from 2019 to 2023. In which year was it the highest? b. What was Mydecos...
-
See Table 2.5 showing financial statement data and stock price data for Mydeco Corp. a. Compute Mydecos ROE each year from 2019 to 2023. b. Compute Mydecos ROA each year from 2019 to 2023. c. Which...

Study smarter with the SolutionInn App


