2) Given: A MIPS computer system with 1 GB of main memory. It has a 4K-Byte...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
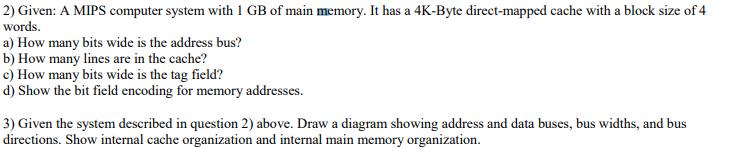
2) Given: A MIPS computer system with 1 GB of main memory. It has a 4K-Byte direct-mapped cache with a block size of 4 words. a) How many bits wide is the address bus? b) How many lines are in the cache? c) How many bits wide is the tag field? d) Show the bit field encoding for memory addresses. 3) Given the system described in question 2) above. Draw a diagram showing address and data buses, bus widths, and bus directions. Show internal cache organization and internal main memory organization. 2) Given: A MIPS computer system with 1 GB of main memory. It has a 4K-Byte direct-mapped cache with a block size of 4 words. a) How many bits wide is the address bus? b) How many lines are in the cache? c) How many bits wide is the tag field? d) Show the bit field encoding for memory addresses. 3) Given the system described in question 2) above. Draw a diagram showing address and data buses, bus widths, and bus directions. Show internal cache organization and internal main memory organization.
Expert Answer:

Related Book For 

Computer Architecture A Quantitative Approach
ISBN: 978-0123704900
4th edition
Authors: John L. Hennessy, David A. Patterson
Posted Date:
Students also viewed these programming questions
-
Q1. You have identified a market opportunity for home media players that would cater for older members of the population. Many older people have difficulty in understanding the operating principles...
-
Portray in words what transforms you would have to make to your execution to some degree (a) to accomplish this and remark on the benefits and detriments of this thought.You are approached to compose...
-
a. Show that if the position x of a moving point is given by a quadratic function of t, x = At 2 + Bt + C, then the average velocity over any time interval [t 1 , t 2 ] is equal to the instantaneous...
-
Franca and Naheed are transferring $8,000 of accounts receivable from each of their sole proprietorships into a partnership. They have agreed that $7,000 of Franca's receivables is collectible but it...
-
Consider the topology shown in Figure 4.44. Suppose that all links have unit cost and that node E is the broadcast source. Using arrows like those shown in Figure 4.44) indicate links over which...
-
How practical is the workload approach to sales force size determination?
-
Accounting for Patents during 2007, Thompson Corporation spent $170,000 in research and development costs. As a result, a new product called the New Age Piano was patented. The patent was obtained on...
-
You're an associate at GreenTech Ventures, and you've been tasked with estimating the Total Addressable Market (TAM) for EV charging stations in the state of New York for the year 2025. You have the...
-
How can bash shell scripting improve resource utilization and process management in Unix systems?
-
A lake contains fishes of n different species. A fisheries biologist catches fishes from the lake until she has caught one example from each species. Assuming that the probability of being caught is...
-
Journalize the following December transactions. Dec. 2 Dec. 5 Dec. 6 Dec. 7 Dec. 10 Dec. 12 Dec. 14 Dec. 17 Dec. 21 Dec. 24 Dec. 28 Dec. 30 Dec. 30 Dec. 31 C. d. e f. Received $275 as advance...
-
A survey was taken on how much trust people place in the information they read on the Internet. The data was shown as follows M S M A M M M M M H M M H M A M A M M M H M H M M M M (ii) Construct a...
-
Let G be a graph which is connected (so you can go from any vertex to any other along the edges). Assume that G has no double edges (there is at most one edge between any two vertices) and no edge...
-
Often in the financial media, you will hear people make reference to specific times of the week, month, or year that typically provide bullish or bearish conditions. One of the historical realities...
-
Perpetual inventory record Electronic Equipment and Much More had an inventory of computers. Using the LIFO method and the perpetual inventory system the company recorded the initial inventory,...
-
2. In the circuit given in Figure 2, i,(t) = 5.67cos(5t)A and v (t) = 70.71 cos(5t 60) V a) Find the equivalent load impedance. State whether the load is inductive or capacitive. b) Calculate the...
-
Let's consider what dynamic scheduling might achieve here. Assume a microarchitecture as shown in Figure 2.42. Assume that the ALUs can do all arithmetic ops (MULTD, DIVD, ADDD, ADDI, SUB) and...
-
In the case of a cache miss, both the switched snooping protocol described earlier and the directory protocol in this case study perform the read or write operation as soon as possible. In...
-
The switched interconnect increases the performance of a snooping cache-coherent multiprocessor by allowing multiple requests to be overlapped. Because the controllers and the networks are pipelined,...
-
a. Using Experiment 3A, what is the gain margin with the default settings? What is this on the linear scale? b. What gain of KP would cause instability? c. What gain of KP will yield 3 dB of GM?...
-
a. Using Experiment 3A, what is the gain margin with the default settings? What is this on the linear scale? b. What gain of G would cause instability? c. What gain of G will yield 3 dB of GM?...
-
Using Experiment 3A, follow the zone-based tuning procedure of Section 3.5 using a square wave command with the following criteria: For KP, allow no overshoot. For KI, allow about 10% overshoot. a....

Study smarter with the SolutionInn App