2. Suppose David has the secret inverse function g(x) corresponding to the hash function h(x) and...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
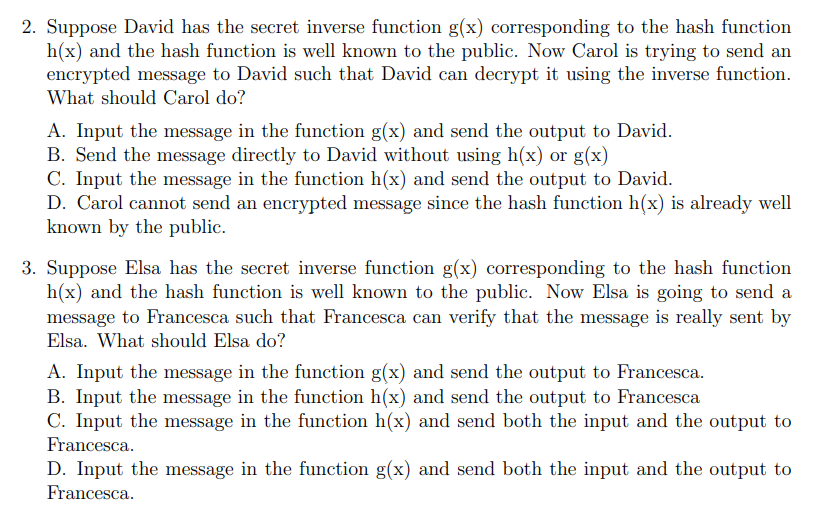
2. Suppose David has the secret inverse function g(x) corresponding to the hash function h(x) and the hash function is well known to the public. Now Carol is trying to send an encrypted message to David such that David can decrypt it using the inverse function. What should Carol do? A. Input the message in the function g(x) and send the output to David. B. Send the message directly to David without using h(x) or g(x) C. Input the message in the function h(x) and send the output to David. D. Carol cannot send an encrypted message since the hash function h(x) is already well known by the public. 3. Suppose Elsa has the secret inverse function g(x) corresponding to the hash function h(x) and the hash function is well known to the public. Now Elsa is going to send a message to Francesca such that Francesca can verify that the message is really sent by Elsa. What should Elsa do? A. Input the message in the function g(x) and send the output to Francesca. B. Input the message in the function h(x) and send the output to Francesca C. Input the message in the function h(x) and send both the input and the output to Francesca. D. Input the message in the function g(x) and send both the input and the output to Francesca. 2. Suppose David has the secret inverse function g(x) corresponding to the hash function h(x) and the hash function is well known to the public. Now Carol is trying to send an encrypted message to David such that David can decrypt it using the inverse function. What should Carol do? A. Input the message in the function g(x) and send the output to David. B. Send the message directly to David without using h(x) or g(x) C. Input the message in the function h(x) and send the output to David. D. Carol cannot send an encrypted message since the hash function h(x) is already well known by the public. 3. Suppose Elsa has the secret inverse function g(x) corresponding to the hash function h(x) and the hash function is well known to the public. Now Elsa is going to send a message to Francesca such that Francesca can verify that the message is really sent by Elsa. What should Elsa do? A. Input the message in the function g(x) and send the output to Francesca. B. Input the message in the function h(x) and send the output to Francesca C. Input the message in the function h(x) and send both the input and the output to Francesca. D. Input the message in the function g(x) and send both the input and the output to Francesca.
Expert Answer:
Answer rating: 100% (QA)
The detailed answer for the above question is provided below 2 The correct option for Carol to send ... View the full answer

Related Book For 

Posted Date:
Students also viewed these economics questions
-
Let A, B be sets. Define: (a) the Cartesian product (A B) (b) the set of relations R between A and B (c) the identity relation A on the set A [3 marks] Suppose S, T are relations between A and B, and...
-
QUIZ... Let D be a poset and let f : D D be a monotone function. (i) Give the definition of the least pre-fixed point, fix (f), of f. Show that fix (f) is a fixed point of f. [5 marks] (ii) Show that...
-
Why are process control systems necessary? Give TWO examples of their usefulness within the plant.
-
In Exercises 1-4, determine whether the lines are parallel, perpendicular, or neither. 1. L1 : y = -2/3x -3 L2 : y = -2/3x + 4 2. L1 : = y 1/4x - 1 L2 : y = 4x + 7 3. L1 : y 1/2x -3 L2 : y = -1/2x +1...
-
Complete the following EPS/EBIT analysis for a company whose stock price is $20, interest rate on funds is 5 percent, tax rate is 20 percent, number of shares outstanding is 500 million, and EBIT...
-
Accounting with sales journal and purchases journal Non-GST version Tobys Traders Ltd uses sales and purchases journals in its accounting system. The following transactions occurred during April...
-
Dr. Heidi Black is the managing partner of the Crestwood Dental Clinic. Dr. Black is trying to determine whether or not the clinic should move patient files and other items out of a spare room in the...
-
In the video below, critique the introduction and conclusion that was delivered in a speech on "Cyber Security." What are the speaker's weaknesses?
-
In Figure 6.5, what rate of output (a) Maximizes total revenue? (b) Maximizes profit per unit? (c) Maximizes total profit? (Choose the higher level of output.) $18 Marginal cost 16 p = MC Profits...
-
The expected EBIT of XYZ Corporation is P 1,500,000. The interest cost is P150,000. The capital structure of the company consists of 15% equity and 10% debt. Using the traditional approach, calculate...
-
For the block diagram shown below, find the transfer function Y(s) U(s) answer. Step U(s) Answer: Y(s) U(s) Use proper form to represent the transfer function in your 1 S+2 Y(s) Transfer Fcn Scope...
-
(a) The following information on credit and advances are found in the book of Jack and Jane bank: i. Letter of credit GHC40000.00 ii. iii. iv. Mortgage GHC23000.00 Personal loan GHC2400 Bankers'...
-
Part A What is the bubble's diameter just as it reaches the surface of the lake, where the water temperature is 20 C? Assume that the air bubble is always in thermal equilibrium with the surrounding...
-
Suppose you are the Director of Finance at a multinational corporation (MNC) thats headquartered in the U.S. The cost of capital for this MNC is 12.2%. You are examining this data that you received...
-
Following are some key balance sheet and income statement figures for Canadian Oil Sands Limited from year end 2015. All figures are in $ millions. Canadian Oil Sands Ratios Table - 2015 Total Debt $...
-
Freedom Tents Ltd was founded over 10 years ago with the principal aim of supplying economical single use tents for musical festival attendees. Events organisers suggested that many tents were...
-
Discrete sample spaces: suppose there are N cable cars in San Francisco, numbered sequentially from 1 to N. You see a cable car at random; it is numbered 203. You wish to estimate N. (See Goodman,...
-
Briefly explain the concept of the mean and standard deviation of a discrete random variable.
-
According to a Gallup poll, 92% of Americans believe in God (Time, June 20, 2011). Suppose that this result is true for the current population of adult Americans. What is the probability that the...
-
A sample was selected of 506 workers who currently receive two weeks of paid vacation per year. These workers were asked if they were willing to accept a small pay cut to get an additional week of...
-
Sophie, the editor of the student newspaper, is going to conduct a survey of students to determine the level of support for the current president of the students' association. She needs to determine...
-
The same study found that \(y=10\) out of \(n=174\) samples identified as having a heavy environmental impact from pastoral (sheep) farms contained Giardia cysts. (a) What is the distribution of...
-
In a research program on human health risk from recreational contact with water contaminated with pathogenic microbiological material, the National Institute of Water and Atmospheric Research (NIWA)...

Study smarter with the SolutionInn App