2. The need for database security is due to the fact that organisational databases concentrate sensitive...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
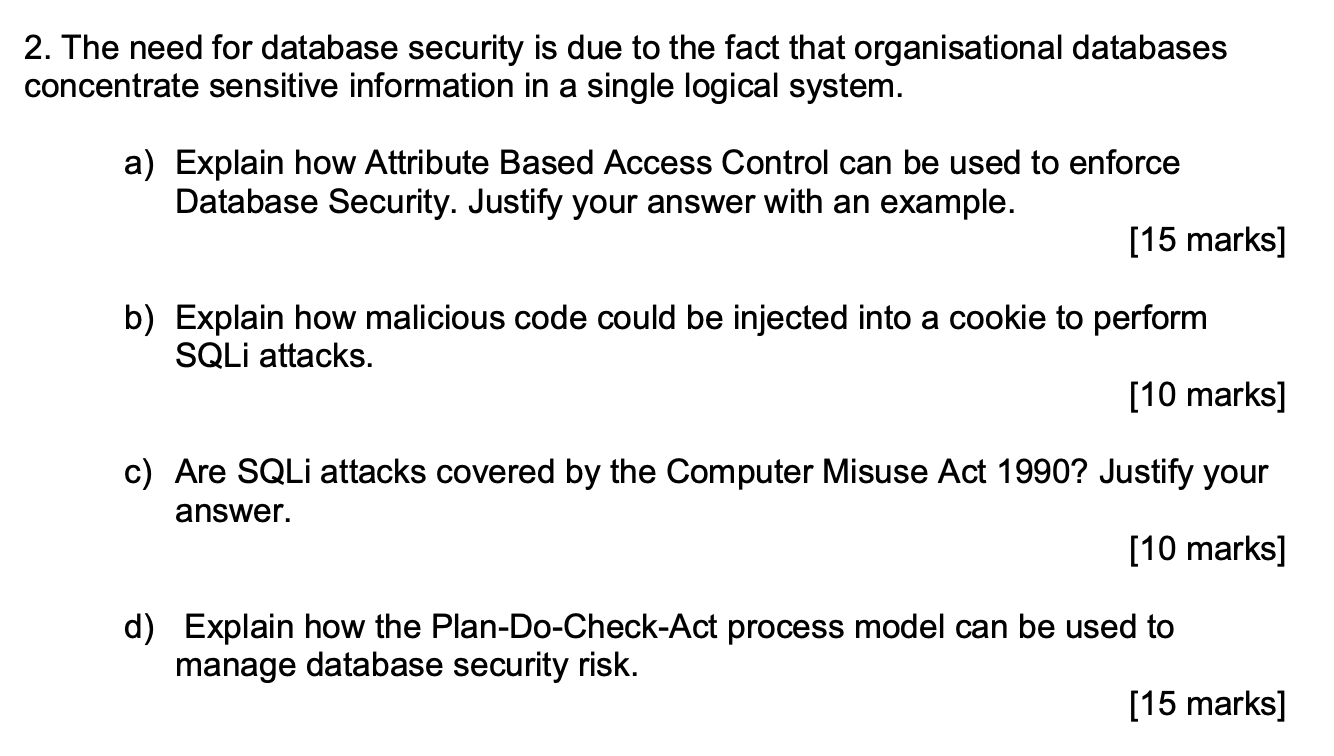
2. The need for database security is due to the fact that organisational databases concentrate sensitive information in a single logical system. a) Explain how Attribute Based Access Control can be used to enforce Database Security. Justify your answer with an example. [15 marks] b) Explain how malicious code could be injected into a cookie to perform SQLi attacks. [10 marks] c) Are SQLi attacks covered by the Computer Misuse Act 1990? Justify your answer. [10 marks] d) Explain how the Plan-Do-Check-Act process model can be used to manage database security risk. [15 marks] 2. The need for database security is due to the fact that organisational databases concentrate sensitive information in a single logical system. a) Explain how Attribute Based Access Control can be used to enforce Database Security. Justify your answer with an example. [15 marks] b) Explain how malicious code could be injected into a cookie to perform SQLi attacks. [10 marks] c) Are SQLi attacks covered by the Computer Misuse Act 1990? Justify your answer. [10 marks] d) Explain how the Plan-Do-Check-Act process model can be used to manage database security risk. [15 marks]
Expert Answer:
Answer rating: 100% (QA)
a AttributeBased Access Control ABAC is a security model that uses attributes as building blocks in a structured language to evaluate and enforce acce... View the full answer

Related Book For 

Principles Of Information Security
ISBN: 9780357506431
7th Edition
Authors: Michael E. Whitman, Herbert J. Mattord
Posted Date:
Students also viewed these programming questions
-
Do some amendment and enhance the given research paper: Table of Content Abstract..3 Action Research.4 Research Methodology and Design...5 Literature Review: NoSQL Database7 Proposal.7 Iteration 1..8...
-
Managing Scope Changes Case Study Scope changes on a project can occur regardless of how well the project is planned or executed. Scope changes can be the result of something that was omitted during...
-
Dylan Flaherty, marketing clerk for TipTop Marketing Agency, recorded the following information for last year: He would like to be able to estimate customer service costs using the number of...
-
What is the return on assets ratio?
-
Cape Cod Shirt Shop manufactures T-shirts and decorates them with custom designs for retail sale on the premises. Several costs incurred by the company are listed below. For each cost, indicate which...
-
Political expectations, inflation, and unemployment Consider a country with two political parties, Democrats and Republicans. Democrats care more about unemployment than Republicans, and Republicans...
-
(Pension Expense, Journal Entries, Amortization of Loss) Gottschalk Company sponsors a defined benefit plan for its 100 employees. On January 1, 2010, the companys actuary provided the following...
-
Nirmo Power and Light has two P1,000 par value bonds outstanding. Bond X matures in five years and Bond Y matures in 15 years. Both bonds pay P80 interest annually and currently sell at their par...
-
Repeat Example 9.2, but with a feed pressure of 5.0 MPa. Compare your results to those obtained at a feed pressure of 1.0 \(\mathrm{MPa}\). Data From Example 9.2:- Air can be separated into...
-
The message signal input to a modulator is given by A, cos (27 x 10r). (a) If frequency modulation is performed with kr = 5x x 10, find the FM bandwidth when (i) Am = 2 and (ii) Am = 4. (b) If phase...
-
How an organization remains successful is when their supply chain managers are strategists, able to synchronize every effort involved in the process: planning, sourcing, producing and delivering a...
-
Evaluate the feasibility of applying blockchain technology to an organization's supply chain. assess blockchain technology and its applicability to supply chain management. Consider how the...
-
What role does social capital play in bolstering individual and collective resilience, and how can social networks be leveraged to enhance adaptive capacity and promote community well-being in times...
-
How do cognitive and emotional processes interact to cultivate resilience in individuals facing adversities, and what neurobiological mechanisms underpin these processes?
-
1. (3 pts) Use a built-in Matlab function to find the solution to the following equation. x ex-1=0 2. (3 pts) Use a built-in Matlab function to determine the area under the curve for -1 x 1 for the...
-
Week Practical Exercise Instructions Compatibility Modej - Word WEEK THREE PRACTICAL EXERCISE INSTRUCTIONS AND HELP PART 1 OF YOUR EXERCISE HORIZONTAL ANALYSIS - Is a method of analyzing financial...
-
The following items were displayed in the statement of affairs for Lubbock Company: Fully secured liabilities ......... $90,000 Partially secured liabilities ....... 12,000 Unsecured liabilities...
-
Illustrate to students that intellectual property is recognized as a protected asset in the United States. U.S. copyright laws extend this privilege to the published word, which includes electronic...
-
I. Comprehend the fact that remote site computing involves a wide variety of computing sites outside the organizations main facility and includes all forms of telework. II. Define the concept of...
-
Which of the following is an event that triggers alarms when no actual attacks are in progress? a. Evasion b. False positive c. False attack stimulus d. False negative
-
Which transaction would generate foreign currency transaction exposure for Ambleu? A . Transaction 1 B . Transaction 2 C . Transaction 3
-
Based on Exhibit 1, what is the foreign exchange gain resulting from Transaction 3 on the December 31, 2016 fi nancial statements? A . NVK1.70 per ton B . NVK90.75 per ton C . NVK248.54 per ton
-
In response to the boards second question, Templeton should reply that if the change is made, the consolidated fi nancial statements for Consolidated Motors would begin to recognize: A . realized...

Study smarter with the SolutionInn App


