2. You are to interface a keyboard to the microprocessor. The keyboard generates a 1-bit control...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
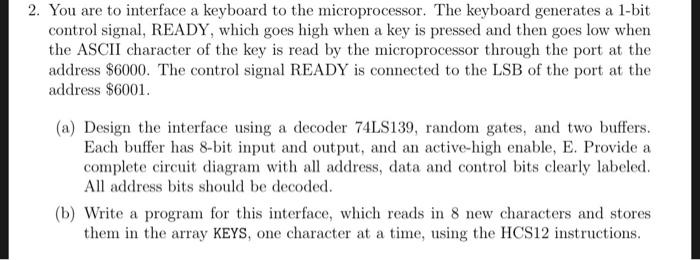
2. You are to interface a keyboard to the microprocessor. The keyboard generates a 1-bit control signal, READY, which goes high when a key is pressed and then goes low when the ASCII character of the key is read by the microprocessor through the port at the address $6000. The control signal READY is connected to the LSB of the port at the address $6001. (a) Design the interface using a decoder 74LS139, random gates, and two buffers. Each buffer has 8-bit input and output, and an active-high enable, E. Provide a complete circuit diagram with all address, data and control bits clearly labeled. All address bits should be decoded. (b) Write a program for this interface, which reads in 8 new characters and stores them in the array KEYS, one character at a time, using the HCS12 instructions. 2. You are to interface a keyboard to the microprocessor. The keyboard generates a 1-bit control signal, READY, which goes high when a key is pressed and then goes low when the ASCII character of the key is read by the microprocessor through the port at the address $6000. The control signal READY is connected to the LSB of the port at the address $6001. (a) Design the interface using a decoder 74LS139, random gates, and two buffers. Each buffer has 8-bit input and output, and an active-high enable, E. Provide a complete circuit diagram with all address, data and control bits clearly labeled. All address bits should be decoded. (b) Write a program for this interface, which reads in 8 new characters and stores them in the array KEYS, one character at a time, using the HCS12 instructions.
Expert Answer:
Answer rating: 100% (QA)
2 Keyboard Interface and Program a Circuit Diagram Heres the circuit diagram for interfacing the key... View the full answer

Related Book For 

Auditing An International Approach
ISBN: 978-0071051415
6th edition
Authors: Wally J. Smieliauskas, Kathryn Bewley
Posted Date:
Students also viewed these programming questions
-
Q1. You have identified a market opportunity for home media players that would cater for older members of the population. Many older people have difficulty in understanding the operating principles...
-
can someone solve this Modern workstations typically have memory systems that incorporate two or three levels of caching. Explain why they are designed like this. [4 marks] In order to investigate...
-
1. Was 1MDB a fraudulent venture from the beginning? Why or why not? 2. How did the US Government become involved in the 1MDB saga? 3. What does the involvement of so many financial institutions in...
-
a. Five "mathletes" celebrate after solving a particularly challenging problem during competition. If each mathlete high fives each other mathlete exactly once, what is the total number of high...
-
Use Table 4 of the Appendix to find tc for a 0.90 confidence level when the sample size is 22. Critical Values for Student's t Distribution TABLE 4 one-tail area 0.250 0.125 0.100 0.075 0.050 0.025...
-
Which of the following is not affected by temperature? (a) Fugacity (b) Activity co-efficient (c) Free energy (d) All of these.
-
Assigning corporate support costs, activity-based costing Zeta Department Store has developed the following information in order to develop a timedriven ABC model for its Accounts Receivable...
-
How do you explain that fewer and fewer organizational management levels exist incorporations today. In other words, there is a flattening of the organizational pyramid. How does this phenomenon...
-
For the second approximation A, we subdivide the 0 to 1 interval into two equal parts. This gives us two rectangles, each touching the curve at its top-right corner. 2. Draw the image shown at right...
-
Has the moral integrity of the criminal law been jeopardized by the increasing number of offenses for which a person can be convicted without proof of any criminal intent?
-
Is there a justification for the criminal law not punishing a person for failing to act when there is a clear moral duty to act?
-
Should it be a defense to a charge of attempt that the accused voluntarily abandoned the attempt?
-
How are laws proscribing obscenity susceptible to the overbreadth and vagueness challenges?
-
How does the criminal law distinguish between mere preparatory conduct and the overt act required for a criminal attempt? Can you think of a situation in which preparatory conduct might have the...
-
A typical pump system is given in Fig. Q1. Pipes are 1 4 in nominal (42.4/3.25mm) and volumetric flow rate is 5.5 m'/h. At this condition, pressure supplied by the pump is 8 mWH. Liquid is the water...
-
Imagine that your best friend knows you are taking a psychology course and wonders what psychology is all about. How would you define psychology for your friend? Write an essay on the discipline of...
-
Does sampling risk always exist in both statistical and non-statistical sampling? Explain your response.
-
You are about to commence the audit of Delta Ltd. (See Exhibit DC 10-2) This is the first time you have worked in the field without direct supervision by a senior, and you are, of course, anxious to...
-
Golden Years Inc. owns and operates 20 rental retirement properties. It has a total of 9000 one-bedroom and 3000 two-bedroom rental units. Tenants pay rent monthly by giving a cheque to the property...
-
How do you determine the number of degrees of freedom of a lumped-mass system?
-
Why are the mass, damping, and stiffness matrices symmetrical?
-
Define these terms: mass coupling, velocity coupling, elastic coupling.

Study smarter with the SolutionInn App