Encryption Mode-ECB vs. CBC The file pic original. bmp can be downloaded from course Blackboard, and...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
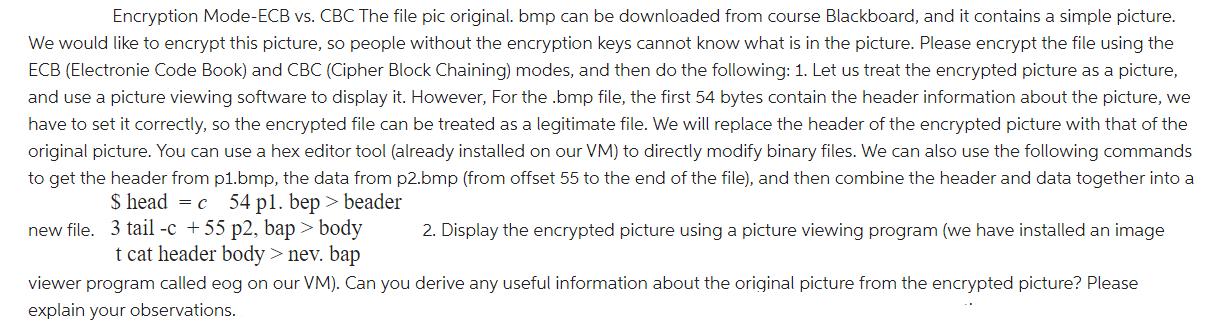
Encryption Mode-ECB vs. CBC The file pic original. bmp can be downloaded from course Blackboard, and it contains a simple picture. We would like to encrypt this picture, so people without the encryption keys cannot know what is in the picture. Please encrypt the file using the ECB (Electronie Code Book) and CBC (Cipher Block Chaining) modes, and then do the following: 1. Let us treat the encrypted picture as a picture, and use a picture viewing software to display it. However, For the .bmp file, the first 54 bytes contain the header information about the picture, we have to set it correctly, so the encrypted file can be treated as a legitimate file. We will replace the header of the encrypted picture with that of the original picture. You can use a hex editor tool (already installed on our VM) to directly modify binary files. We can also use the following commands to get the header from p1.bmp, the data from p2.bmp (from offset 55 to the end of the file), and then combine the header and data together into a $ head = c 54 pl. bep > beader new file. 3 tail -c +55 p2, bap> body t cat header body > nev. bap 2. Display the encrypted picture using a picture viewing program (we have installed an image. viewer program called eog on our VM). Can you derive any useful information about the original picture from the encrypted picture? Please explain your observations. Encryption Mode-ECB vs. CBC The file pic original. bmp can be downloaded from course Blackboard, and it contains a simple picture. We would like to encrypt this picture, so people without the encryption keys cannot know what is in the picture. Please encrypt the file using the ECB (Electronie Code Book) and CBC (Cipher Block Chaining) modes, and then do the following: 1. Let us treat the encrypted picture as a picture, and use a picture viewing software to display it. However, For the .bmp file, the first 54 bytes contain the header information about the picture, we have to set it correctly, so the encrypted file can be treated as a legitimate file. We will replace the header of the encrypted picture with that of the original picture. You can use a hex editor tool (already installed on our VM) to directly modify binary files. We can also use the following commands to get the header from p1.bmp, the data from p2.bmp (from offset 55 to the end of the file), and then combine the header and data together into a $ head = c 54 pl. bep > beader new file. 3 tail -c +55 p2, bap> body t cat header body > nev. bap 2. Display the encrypted picture using a picture viewing program (we have installed an image. viewer program called eog on our VM). Can you derive any useful information about the original picture from the encrypted picture? Please explain your observations.
Expert Answer:
Answer rating: 100% (QA)
To encrypt the picture using ECB Electronic Code Book and CBC Cipher Block Chaining modes we need to ... View the full answer

Related Book For 

Probability and Statistical Inference
ISBN: 978-0321923271
9th edition
Authors: Robert V. Hogg, Elliot Tanis, Dale Zimmerman
Posted Date:
Students also viewed these programming questions
-
James was delivered at 39 weeks in a planned delivery. He was the largest of my babies, weighing 8 pounds, 4 ounces, and measuring 21.5 inches. He had a raspy cry, a full head of hair, and very light...
-
A sequence of n job candidates is prepared to interview for a job. We would like to hire the best candidate, but we have no information to distinguish the candidates before we interview them. We...
-
Find the values of the parameter p > 0 for which the following series converge. In k
-
Refer to Vargas Products in E12-27A. Compute the IRR of each project and use this information to identify the better investment. Use the NPV method to determine whether Vargas Products should invest...
-
For the following exercises, evaluate the function f(x) = 3x 2 + 2x at the given input. Write the domain of the function f(x) = 3 x in interval notation.
-
On June 14, 1988, Thomas John Heck Jr. executed a note promising to pay Paul D. Heck \($51,000\) at 7 percent interest compounded annually. The note contains the following payment terms: Perpetual 90...
-
McLennon Company had an Accounts Receivable balance of $320,000 and a credit balance in Allowance for Uncollectible Accounts of $16,700 at January 1, 2014. During the year, the company recorded the...
-
In some labor markets, the supply of labor is as follows (where W represents wages and L represents the number of employees): W = 113 + 0.21L However, the demand for labor is: W = 958 -0.28L a) At...
-
? ?? ? ? Assume that Alpha and Omega compete in the same four-digit SIC code industry and offer comparable products and services. The following table contains their reported financial performance and...
-
81.5% complete Question A financial organization is currently handling a document that contains sensitive customer information, including financial details and social security numbers. According to...
-
In the case of the VA situation, what, if any, would be the benefit of a "pilot program", feasibility study, or experimental trial?
-
Introduce yourself as leader and post your Leader Within representation and description here.
-
6. Ann obtains a fully amortizing 30 year Fixed Rate Mortgage with monthly payments for $1,250,000 at 4.38%. What fraction of Ann's 40th payment goes to interest? Write your answer in percent,...
-
Compare adverse impact and disparate treatment during the staffing process by providing specific examples in your response. Discuss the federal law or laws that may be violated when an adverse impact...
-
Examine the challenges and potential arrangements for planning and executing a feasible vitality framework for a large-scale mechanical office, with a center on mechanical building standards
-
S1: Gross Philippine Billings (GPB) is the total amount of gross revenue from the passage of persons, excess baggage, and cargoes originating from the Philippines irrespective of the place of sale...
-
Why is it important to understand the macro-environment when making decisions about an international retail venture?
-
Let X1, X2, . . . , Xn be a random sample from a gamma distribution with known and with = 1/. Say has a prior pdf that is gamma with parameters 0 and 0, so that the prior mean is 00. (a) Find the...
-
Let X equal the weight of the soap in a 6-pound box. Assume that the distribution of X is N(6.05, 0.0004). (a) Find P(X < 6.0171). (b) If nine boxes of soap are selected at random from the production...
-
Let X have a logistic distribution with pdf Show that Has a U(0, 1) distribution. f(x) = (1+e-x)2 00 < X < 00. X-24 1
-
Methanol can be produced by the reaction of carbon dioxide and hydrogen as per the following reaction: The fresh feed available is 500 kmol/hr with 2% inerts and the rest being the reactants in...
-
In an instant coffee plant, 10000 kg/hr of coffee extract containing 20% solids is concentrated using a vacuum evaporator which is designed to produce a concentrated extract with 50% solids suitable...
-
The water gas shift reaction (WGSR) is the reaction of carbon monoxide with steam to produce carbon dioxide and hydrogen and it is used in the production of hydrogen for industrial applications. 600...

Study smarter with the SolutionInn App