3. Alice and Bob are employees residing in two dispersed branches, D1 and D2, of the...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
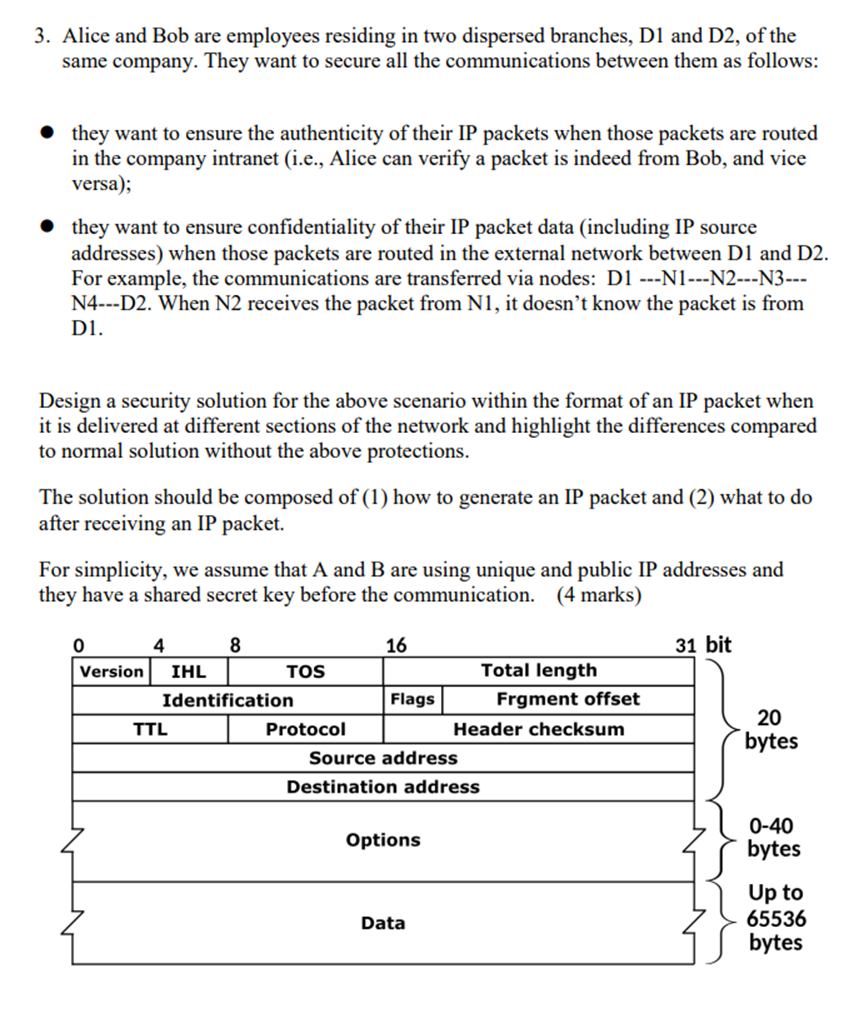
3. Alice and Bob are employees residing in two dispersed branches, D1 and D2, of the same company. They want to secure all the communications between them as follows: they want to ensure the authenticity of their IP packets when those packets are routed in the company intranet (i.e., Alice can verify a packet is indeed from Bob, and vice versa); they want to ensure confidentiality of their IP packet data (including IP source addresses) when those packets are routed in the external network between D1 and D2. For example, the communications are transferred via nodes: D1 ---N1---N2---3--- N4---D2. When N2 receives the packet from N1, it doesn't know the packet is from D1. Design a security solution for the above scenario within the format of an IP packet when it is delivered at different sections of the network and highlight the differences compared to normal solution without the above protections. The solution should be composed of (1) how to generate an IP packet and (2) what to do after receiving an IP packet. For simplicity, we assume that A and B are using unique and public IP addresses and they have a shared secret key before the communication. (4 marks) 0 4 8 16 31 bit Version IHL TOS Total length Identification Flags Frgment offset TTL Protocol Header checksum Source address Destination address Options Data 20 bytes 0-40 bytes Up to 65536 bytes 3. Alice and Bob are employees residing in two dispersed branches, D1 and D2, of the same company. They want to secure all the communications between them as follows: they want to ensure the authenticity of their IP packets when those packets are routed in the company intranet (i.e., Alice can verify a packet is indeed from Bob, and vice versa); they want to ensure confidentiality of their IP packet data (including IP source addresses) when those packets are routed in the external network between D1 and D2. For example, the communications are transferred via nodes: D1 ---N1---N2---3--- N4---D2. When N2 receives the packet from N1, it doesn't know the packet is from D1. Design a security solution for the above scenario within the format of an IP packet when it is delivered at different sections of the network and highlight the differences compared to normal solution without the above protections. The solution should be composed of (1) how to generate an IP packet and (2) what to do after receiving an IP packet. For simplicity, we assume that A and B are using unique and public IP addresses and they have a shared secret key before the communication. (4 marks) 0 4 8 16 31 bit Version IHL TOS Total length Identification Flags Frgment offset TTL Protocol Header checksum Source address Destination address Options Data 20 bytes 0-40 bytes Up to 65536 bytes
Expert Answer:

Related Book For 

Posted Date:
Students also viewed these computer network questions
-
Developments in Technology Light is incident from air on the end face of a multimode optical fibre at angle of incidence as shown below. n n 1 2 The refractive indices of the core and cladding are...
-
1456HHSC attend all (a) In the quantum teleportation protocol, Alice and Bob are every in possession of one qubit of a couple in the joint country00i + statei. Explain how the protocol works. In...
-
One way to delete nodes from a known position in a leftist heap is to use a lazy strategy. To delete a node, merely mark it deleted. When a findMin or deleteMin is performed, there is a potential...
-
What is the characteristic aspect of Rayleigh flow? What are the main assumptions associated with Rayleigh flow?
-
Solve each logarithmic equation in Exercises 4992. Be sure to reject any value of x that is not in the domain of the original logarithmic expressions. Give the exact answer. Then, where necessary,...
-
What are some of the limitations of the traditional HR metrics?
-
The postanesthesia care area (recovery room) at St. Lukes Hospital in Maumee, Ohio, was recently enlarged. The hope was that with the enlargement the mean number of patients per day would be more...
-
Assume a 10-year Treasury bond has a coupon rate of 3.2 % and par value of $1000, and yield to maturity of 2%. Is this bond selling at a premium or discount? Explain why?
-
State and analyze De Sade's argument that the purpose of sex is not procreation? I need more in details?
-
9) Consider the following reaction: 2NO(g) N2(g) + O2(g) with a Keq = 9.92 at 1000C. What is the concentration of NO when the equilibrium concentrations of the other compounds are as follows: [N2] =...
-
What is the hybridization of each carbon in CH3CH CHCOCH? What are the CCC bond angles?
-
A 25.0 mL solution of Ba(OH)2 is neutralized with 37.9 mL of 0.250 M HBr. What is the concentration of the original Ba(OH)2 solution?
-
If 1 0 0 . 0 mL of 0 . 1 0 0 M of acetic acid, HCH 3 COO, is added to 1 0 0 . 0 mL of 0 . 1 0 0 M potassium hydroxide, KOH, calculate the pH of the resulting solution. The Ka of acetic acid is 1 . 8...
-
Aphids secrete an alarm pheromone having the structure shown. What is its molecular formula? Classify each carbon according to its hybridization state.
-
Using the governmental- and proprietary-type funds, indicate which would be used to record each of the following events. GF General Fund SRF Special Revenue Fund DSF Debt Service Fund CPF Capital...
-
The Pletcher Transportation Company uses a responsibility reporting system to measure the performance of its three investment centers: Planes, Taxis, and Limos. Segment performance is measured using...
-
Initially, both legs of a mercury manometer are open to the atmosphere, and the mercury height in the left leg is \(40.0 \mathrm{~mm}\). You inflate a balloon until it has a surface area of \(0.300...
-
At an atmospheric pressure of \(1.00 \mathrm{~atm}\), the height of the liquid in the tube of a mercury barometer is \(760 \mathrm{~mm}\) only if you ignore capillary rise in the tube. Obtain an...
-
A hydrogen-filled balloon is used to lift a \(125-\mathrm{kg}\) stone off the ground. The basket holding the stone has a mass of \(15.0 \mathrm{~kg}\). What must the minimum radius \(R\) of the...

Study smarter with the SolutionInn App


