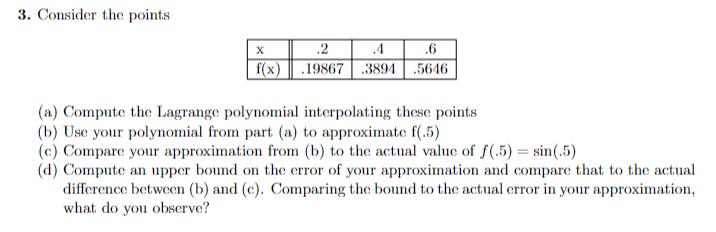
3. Consider the points X .2 .4 .6 f(x) 19867 .3894 5646 (a) Compute the Lagrange...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
3. Consider the points X .2 .4 .6 f(x) 19867 .3894 5646 (a) Compute the Lagrange polynomial interpolating these points (b) Use your polynomial from part (a) to approximate f(.5) (c) Compare your approximation from (b) to the actual value of f(.5)=sin(.5) (d) Compute an upper bound on the error of your approximation and compare that to the actual difference between (b) and (c). Comparing the bound to the actual error in your approximation, what do you observe? 3. Consider the points X .2 .4 .6 f(x) 19867 .3894 5646 (a) Compute the Lagrange polynomial interpolating these points (b) Use your polynomial from part (a) to approximate f(.5) (c) Compare your approximation from (b) to the actual value of f(.5)=sin(.5) (d) Compute an upper bound on the error of your approximation and compare that to the actual difference between (b) and (c). Comparing the bound to the actual error in your approximation, what do you observe?
Expert Answer:

Posted Date:
Students also viewed these programming questions
-
Helena Paper Corporation is testing its ability to budget Direct Material costs by comparing the standards it predicted to actual data. Helena has the following standards: Standard Quantity per unit:...
-
You have been provided with the description of a programming language, J, intended for scripting applications. Its syntax is similar to a cut-down version of Java in that it consists of function...
-
The operating system typically provides each process with the illusion that it runs in a contiguous piece of memory. State the problem of external fragmentation in memory where processes have...
-
A company acquired a chargeable asset (not a chattel) in 1979. The asset was sold in December 2020 for 2,800. Compute the chargeable gain or allowable loss if the original cost of the asset and its...
-
Give some examples of a need for BI coverage from dependent properties.
-
Histidine is an amino acid with three titratable groups: an - NH3+ group (pKa = 9.2), a -COOH group 1 (pKa = 1.8), and an imidazole (amine-like) group 1 (pKa = 6.0). Te titration curve for histidine...
-
Explain in a few lines why diversifiable risk cannot be remunerated on markets in equilibrium?
-
Two light sources of identical strength are placed 10 m apart. An object is to be placed at a point P on a line parallel to the line joining the light sources and at a distance d meters from it (see...
-
Keep-Or-Drop Decision, Alternatives, Relevant Costs Reshier Company makes three types of rug shampooers. Model 1 is the basic model rented through hardware stores and supermarkets. Model 2 is a more...
-
A cybersecurity risk-management plan is a plan designed to protect a system exposed to the Internet, internal employees, contractors, disasters, failures, and more. What are some common cybersecurity...
-
3 01 If A-1 -5 14 B 10 7-6 13. A-B (69) -2 3 8 -76 0 and C= 10-35 [6 1-8 [92] cal , calculate the value of each expression below. -2 4 14. 3A (69) 15. CB (69)
-
Do consumer products and services perform missions?
-
List the sources and briefly discuss the various strategies associated with each source for integrating cost and value in projects.
-
Is the term mission restricted to the military applications? Explain why?
-
What is a State of Operation?
-
Provide an overview of the project cost and value integration process.
-
b ) Compare and contrast the three drivers of fraud discussed in class. Provide a real - world example of each
-
In Problem use geometric formulas to find the unsigned area between the graph of y = f(x) and the x axis over the indicated interval. f(x) = x + 5; [0, 4]
-
Prepare the operating budget, the financial budget, and the supporting schedules.
-
Distinguish between operating and financial budgets.
-
Follow the principal steps in preparing a master budget.

Study smarter with the SolutionInn App

