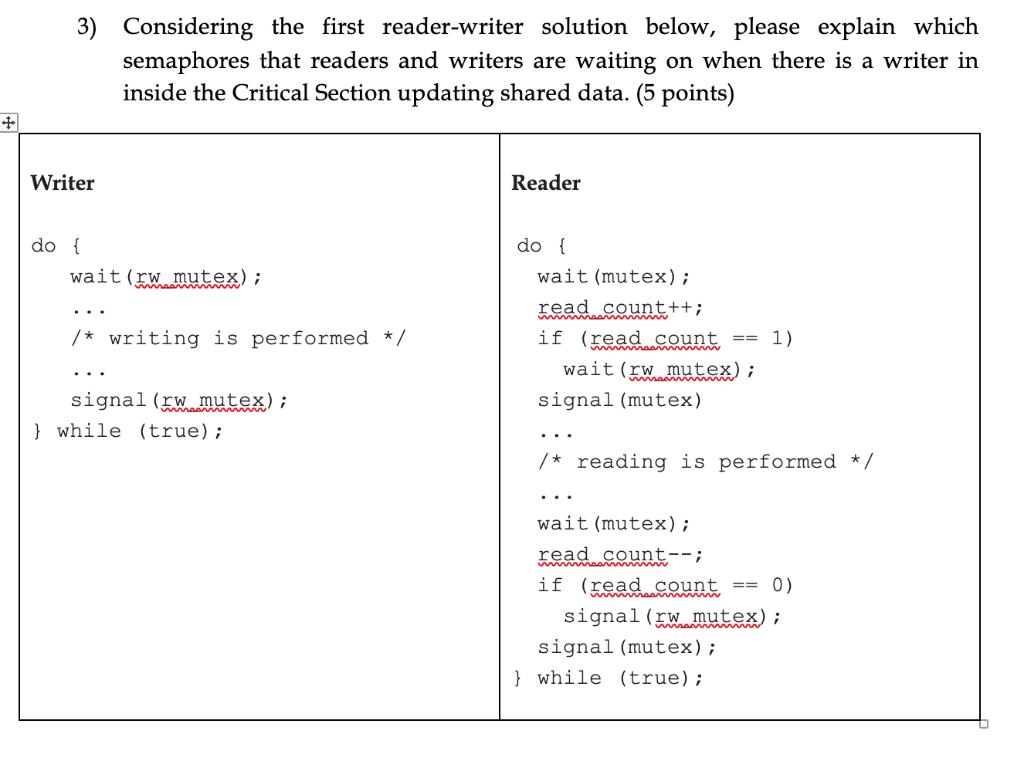
+ 3) Considering the first reader-writer solution below, please explain which semaphores that readers and writers...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
+ 3) Considering the first reader-writer solution below, please explain which semaphores that readers and writers are waiting on when there is a writer in inside the Critical Section updating shared data. (5 points) Writer Reader do { wait (rw mutex); do { wait (mutex); read count++; /* writing is performed */ if (read count == 1) wait (w mutex); signal (w mutex); signal (mutex) } while (true); ... /* reading is performed */ wait (mutex); read count--; if (read count == 0) signal (w mutex); signal (mutex); } while (true); + 3) Considering the first reader-writer solution below, please explain which semaphores that readers and writers are waiting on when there is a writer in inside the Critical Section updating shared data. (5 points) Writer Reader do { wait (rw mutex); do { wait (mutex); read count++; /* writing is performed */ if (read count == 1) wait (w mutex); signal (w mutex); signal (mutex) } while (true); ... /* reading is performed */ wait (mutex); read count--; if (read count == 0) signal (w mutex); signal (mutex); } while (true);
Expert Answer:
Answer rating: 100% (QA)
The image you sent depicts a solution to the readerswriters problem which is a classical problem in concurrent programming It describes how to synchro... View the full answer

Related Book For 

Principles Of Information Security
ISBN: 9780357506431
7th Edition
Authors: Michael E. Whitman, Herbert J. Mattord
Posted Date:
Students also viewed these programming questions
-
"internet radios" for streaming audio, and personal video recorders and players. Describe design and evaluation processes that could be used by a start-up company to improve the usability of such...
-
CANMNMM January of this year. (a) Each item will be held in a record. Describe all the data structures that must refer to these records to implement the required functionality. Describe all the...
-
What are two important limitations of the Heckscher- Ohlin theory?
-
Compare HomePro Corp. and Away Inc. by converting their income statements to common size. Which company earns more net income? Which company's net income is a higher percentage of its net sales? (in...
-
(a) How might the confirmation tendency affect your client acceptance decision? (b) How might the overconfidence tendency come into play in your client acceptance decision? (c) How might an auditor...
-
Reconsider Problem 65. Plot a graph of capital recovery cost versus useful life for lives 1 to 25 by 1. Data from problem 65 Crush Autosmashers can purchase a new electromagnet for moving cars at a...
-
On June 10, Rebecca Company purchased $7,600 of merchandise from Clinton Company, FOB shipping point, terms 2/10, n/30. Rebecca pays the freight costs of $400 on June 11. Damaged goods totaling $300...
-
A bank in Toronto charges 2.2% commission to buy and sell currencies. Assume that the current exchange rate is US$1 = C$1.1153. a. How many Canadian dollars will you have to pay to purchase US$4,500?...
-
Description: The bill below was received on February 12, 2021. Please fill out the transaction form below to display how this invoice would be booked. In addition, please add any questions you may...
-
The vapor pressure of n-pentane is given by In Pbar = 8.630-2819.7/T + (1.855 10)T. Derive an expression for AHvap as a function of temperature and find AHvap at its normal boiling point 36.1 C.
-
Assume that consumers view haircuts as the same among sellers and there are hundreds of barbers in a given market. The current market equilibrium price for a haircut is $15. Bobs Barbershop has a...
-
Explain the main principles of critical thinking and describe how these might apply to individual and work colleagues ideas to assist objective and rationale debate.
-
2. a. What is the area under the normal curve between z = -1.0 and z = -2.0? b.The standard normal probability distribution is unique because it has ________.
-
Remote teams yes, prove to add different issues of their own due to the nature of not being solely located in a FTF format for staff to work through any issues. But, at the same time, are these...
-
International Shoe v. Washington, 326 U.S. 310 (1945), Write a 500 (2 pages) word summary of where the courts stand on long-arm jurisdiction, specifically emphasizing websites and long-arm...
-
Conduct a VRIO analysis by ranking Husson University (in Maine) business school in terms of the following six dimensions relative to the top three rival schools. If you were the dean with a limited...
-
Which of the following is the component of the maintenance model that focuses on identifying, assessing, and managing the configuration and status of information assets in an organization? a....
-
I. Explain that the purpose of a wireless vulnerability assessment is to find and document vulnerabilities in the organizations wireless networks. II. Gain an understanding that attackers from this...
-
Explain how to identify the risk. Explain how to determine the current level of risk (risk analysis). Discuss how to determine if the current level of risk is acceptable (risk evaluation). Determine...
-
Derive Eq. (13.79). Equation (13.79) Pa 1 (1+K) Mnp Mp-1 k=0 1 (Mnp+k) K k! (Mnp) (1+K,
-
Develop a MATLAB program to calculate the cumulative probability of detection.
-
The sum inside Eq. (13.79) presents a very formidable challenge. It can be, however, computed recursively with relative ease. Develop a recursive algorithm to calculate this sum. Equation (13.79)...

Study smarter with the SolutionInn App


