3. Differentiate between: a. Encrypt & Decrypt b. Encipher & Decipher c. Symmetric Encryption and Asymmetric...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
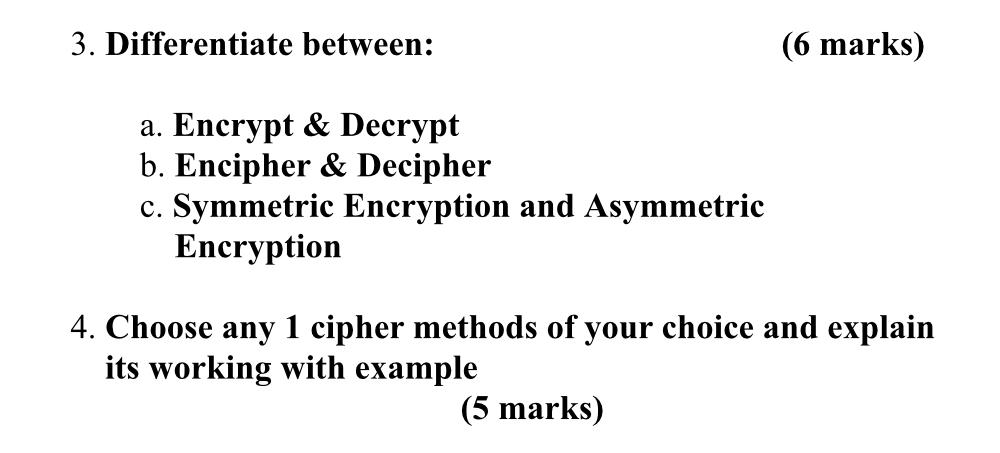
3. Differentiate between: a. Encrypt & Decrypt b. Encipher & Decipher c. Symmetric Encryption and Asymmetric Encryption (6 marks) 4. Choose any 1 cipher methods of your choice and explain its working with example (5 marks) 3. Differentiate between: a. Encrypt & Decrypt b. Encipher & Decipher c. Symmetric Encryption and Asymmetric Encryption (6 marks) 4. Choose any 1 cipher methods of your choice and explain its working with example (5 marks)
Expert Answer:
Answer rating: 100% (QA)
Lets go through the questions as outlined 3 Differentiate between 6 marks a Encrypt Decrypt Encryption is the process of converting plain text or any other form of data into a coded version called cip... View the full answer

Related Book For 

Principles Of Information Security
ISBN: 9780357506431
7th Edition
Authors: Michael E. Whitman, Herbert J. Mattord
Posted Date:
Students also viewed these programming questions
-
If A is a square matrix, then which of the following matrix is not symmetric (a) A+ A' (b) AA' (c) A'A (d) A-A'
-
Solve the shortest-route problem for the network shown inFigure. 9 6 4 2 0 5 6 6 3 5
-
At one time the Thames River in England supported an abundant community of fish. Pollution then destroyed all the fish in a 40-mile stretch near its mouth for a 45-year period beginning in 1915....
-
Do you think that it is important to maintain net neutrality? Why or why not?
-
Use the matrices below as needed to complete Problems. Perform the indicated operations in Problems A + B 4 2 -5 -5 -11 8 A = 3 -1 B 4 4 -3 -2 -2 1 4 -2 1 1 3 D = 1 1 E = 4 1 C = 2 1 3 6. G -1 -5 1 |...
-
In spring 1989, Michael Jordan and the Chicago Bulls were in Indianapolis, Indiana, to play against the Indiana Pacers. At the same time, Karla Knafel was singing with a band at a hotel in...
-
Landers Company manufactures a number of products. The standards relating to one of these products are shown below, along with actual cost data for May. The production superintendent was pleased when...
-
India's trade deficit has risen by almost 88% in financial year 2022. While total exports increased, imports too soared to a great extent. Analyze the impact of this trade deficit on the balance of...
-
Sunnyville Bank wants to identify customers who may be interested in its new mobile banking app. The worksheet called Mobile_Banking_Data contains 500 customer records collected from a previous...
-
(a) Find the value of k for which the following ODE is an exact ODE. (xy + x 2y + 3)dx + x?ydy = k(x + y)dy (b) Find it's general solution once you find a value of k in (a). (c) Find the particular...
-
Derive an Equation for Magnetic Force F12 The magnetic force F12 cannot be determined from Coulomb's law because the pole strengths q* and q2* are not known. In the space below, derive an algebraic...
-
A chemicals company produces two main products, C and B. The market price of C is 205 and that of B is 155 per 100 kg. The resource requirements for producing 100 kg of each of the two products are: ...
-
A company manufactures computer monitors. Among the various models, 5 models are top products which bring high revenue. Assuming the manufacturing lines are running for 9 hours a day for 7 days a...
-
Q1. A stock that is priced at $3,810 today has an implied volatility of 18.3%. The continuously compounded risk- free interest rate is 6.5% per annum. (a) (i) Determine the theoretical price of a...
-
Given f(x) = x+3x-1 x+1 3 find all x such that f(x) = 5.
-
TransWays, Inc. is a global U.S. company and provider of offshore oil drilling services and equipment based in Houston, Texas. The company just received a multi-million-dollar contract to explore for...
-
Determine whether the lines are parallel, perpendicular, or neither. 2x + 3y = -12, 2y - 3x = 8
-
Gain an understanding that to have a full understanding of the importance of an information system, one must have an awareness of what all is included within it. Review the six most common elements...
-
True or False: SESAME is an authentication system that is the result of a European research and development project and is similar to Kerberos.
-
Describe this category and comment to students that it includes the possibility of acts performed without intent or malicious purpose by an individual who is an employee of an organization. Discuss...
-
In the past five years, there have been significant innovations in technology such as smartphones and tablets. Technology companies rely on intellectual property (IP) rights, such as patents,...
-
Respondents Varsity Brands, Inc., Varsity Spirit Corporation, and Varsity Spirit Fashions & Supplies, Inc., design, make, and sell cheerleading uniforms. Respondents have obtained or acquired more...
-
Mr. Tam is the front man for the Asian American dance-rock band The Slants. Mr. Tam named his band The Slants to reclaim and take ownership of Asian stereotypes. The band draws inspiration for its...

Study smarter with the SolutionInn App


