3. Give an example of class B private IP address. Is a private address unique? Can...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
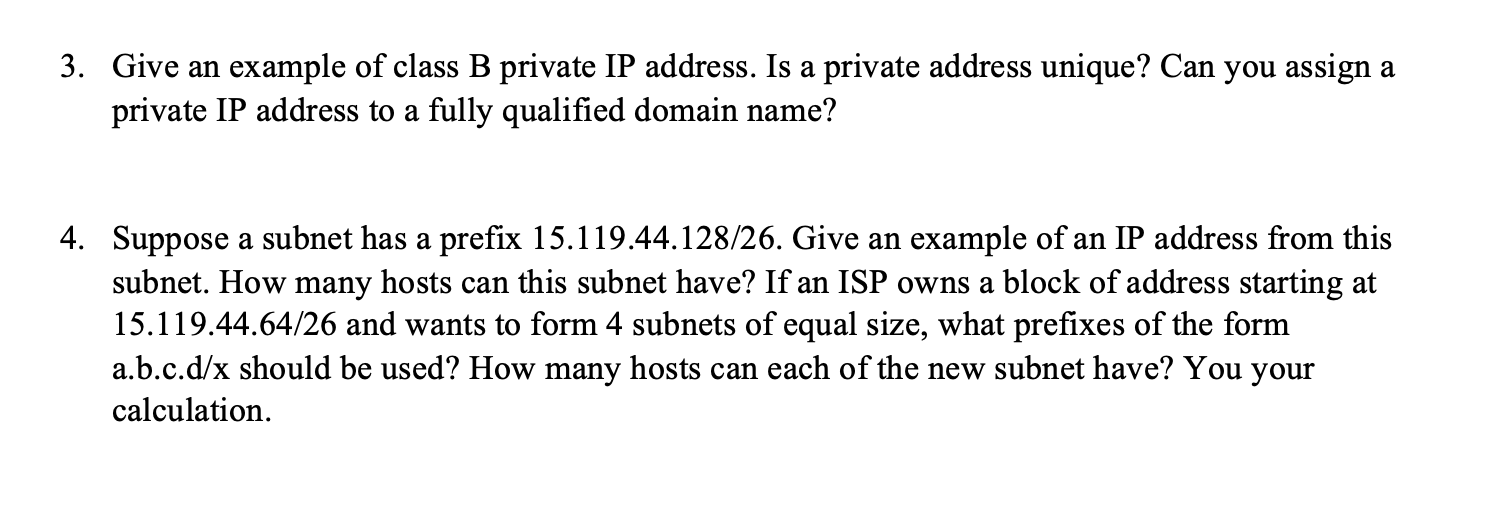
3. Give an example of class B private IP address. Is a private address unique? Can you assign a private IP address to a fully qualified domain name? 4. Suppose a subnet has a prefix 15.119.44.128/26. Give an example of an IP address from this subnet. How many hosts can this subnet have? If an ISP owns a block of address starting at 15.119.44.64/26 and wants to form 4 subnets of equal size, what prefixes of the form a.b.c.d/x should be used? How many hosts can each of the new subnet have? You your calculation. 3. Give an example of class B private IP address. Is a private address unique? Can you assign a private IP address to a fully qualified domain name? 4. Suppose a subnet has a prefix 15.119.44.128/26. Give an example of an IP address from this subnet. How many hosts can this subnet have? If an ISP owns a block of address starting at 15.119.44.64/26 and wants to form 4 subnets of equal size, what prefixes of the form a.b.c.d/x should be used? How many hosts can each of the new subnet have? You your calculation.
Expert Answer:
Answer rating: 100% (QA)
Answer The Range of Class B private IP address is 1721600 17231255255 Class B IP address 172160016 The private IP address is not globally unique They ... View the full answer

Related Book For 

Computer Networking A Top-Down Approach
ISBN: 978-0136079675
5th edition
Authors: James F. Kurose, Keith W. Ross
Posted Date:
Students also viewed these electrical engineering questions
-
What purpose does regression analysis serve? Give an example of how it might be used in marketing research. How is the strength of regression measures of association determined?
-
What is activity-based costing? Give an example of how it could be used to identify an incremental fixed cost.
-
Give an example of an application in which data in a file should be accessed in the following order: a. Sequentially b. Randomly
-
Analyze the residuals from the regression model on the patient satisfaction data from Exercise 4.49. Comment on the adequacy of the regression model. MTB> Stat> Regression > Regression Normal...
-
Each team member is to become an expert on one depreciation method to facilitate teammates understanding of that method. Follow these procedures: a. Each team member is to select an area for...
-
Explain how income is recognized under the cash method of accounting.
-
State a conclusion. Exercises 49 refer to the following data: Electric motors are assembled on four different production lines. Random samples of motors are taken from each line and inspected. The...
-
On February 25, Madison County Rocks Inc., a marble contractor, issued for cash 120,000 shares of $36 par common stock at $40, and on June 3, it issued for cash 50,000 shares of preferred stock, $8...
-
How does advanced computational fluid dynamics (CFD) analysis contribute to the design optimization of complex hydraulic structures such as spillways, weirs, and stormwater management systems,...
-
An investor wants to minimize market risk on a $50 million stock portfolio by using futures for hedging. The portfolios beta with respect to the S&P 500 equity index is 1.25. The current index...
-
13. Express logx (81y) logx (3) + logx (2y) as a single logarithm,
-
A projectile of mass 0.525 kg is shot from a cannon, at height 6.6 m, as shown in the figure, with an initial velocity v having a horizontal component of 6.9 m/s. The projectile rises to a maximum...
-
Solve: 8x-1=323x
-
6. An object is rotating about a fixed axis with a constant angular speed of wo= rad/s. At t = 0s, the object is at 0o = - rad. a) What is the angular position of the object at t = 1s? b) What is the...
-
Eg3: Show that the vectors v =(1, 2, 1), v = (2. 9, 0), and v (3, 3, 4) form a basis for R.
-
Can you help me add comments to the following code: package testing; import java.util.Random; public class dice { public static void main(String[] args) { Random random = new Random(); int...
-
Read the case study Richter: Information Technology at Hungarys Largest Pharma and answer the following question: How does the organization ensure the accuracy of the data it stores?
-
Design (give a pseudocode description of) an application-level protocol that maintains the host addresses of all hosts participating in a multicast group. Specifically identify the network service...
-
We have said that an application may choose UDP for a transport protocol because UDP offers finer application control (than TCP) of what data is sent in a segment and when. a. Why does an application...
-
Consider our authentication protocol in Figure 8.16 in which Alice authenticates herself to Bob, which we saw works well (i.e., we found no flaws in it). Now suppose that while Alice is...
-
You are the senior partner of a large, local audit firm. In reviewing the work of a junior staff member on a compilation engagement for Greasemonkey's Delight Inc., a local autoparts store (in which...
-
You have been assigned to audit the accounts payable of Slamtastic, a small recording company specializing in alternative music. Following is a portion of their accounts payable journal for the month...
-
The chapter discussed three issues to consider when obtaining evidence using a sample-based audit procedure: a. The number of transactions or items to examine b. The actual transactions or items to...

Study smarter with the SolutionInn App


