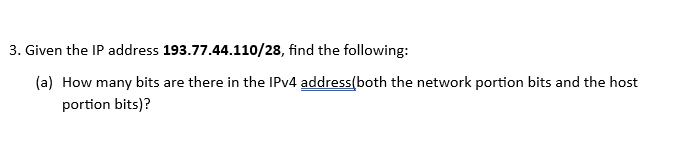
3. Given the IP address 193.77.44.110/28, find the following: (a) How many bits are there in...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
3. Given the IP address 193.77.44.110/28, find the following: (a) How many bits are there in the IPv4 address(both the network portion bits and the host portion bits)? 3. Given the IP address 193.77.44.110/28, find the following: (a) How many bits are there in the IPv4 address(both the network portion bits and the host portion bits)?
Expert Answer:
Answer rating: 100% (QA)
In IPv4 an address is represented by 32 bits These 32 bits are typically d... View the full answer

Related Book For 

Business Data Networks and Security
ISBN: 978-0134817125
11th Edition
Authors: Raymond R. Panko, Julia L. Panko
Posted Date:
Students also viewed these programming questions
-
a. How many bits are there in an IPv4 mask? 5a.) A mask has _____ bits. a. 8 b. 16 c. 32 d. It cannot be determined from the information given. b. What do the 1s in an IPv4 network mask correspond to...
-
XYZ Corporation is considering two mutually exclusive projects that require a $150,000 investment each. Project A has an expected life of 6 years and will generate net cash flows of $35,000 per year....
-
Use the graphs of f and f 1 to complete each table of function values. (a) (b) (c) (d) y y 4. 4. -2 2 4 -2 2 4 -2 -2 -4 2. -4 -2 0| 4 (f(f-'(x)))
-
The isothermal compressibility of copper at 293 K is 7.35 10 7 atm 1 . Calculate the pressure that must be applied in order to increase its density by 0.08 per cent.
-
Given the following information, prepare a statement of cash flows. Increase in accounts receivable $25 Increase in inventories Operating income Interest expense 30 75 12 25 Increase in accounts...
-
Consider FASB standards for reporting by private not-for-profit organizations and answer the following: a. What are the financial reports required of all not-for-profits? What additional report is...
-
In the video below, critique the introduction and conclusion that was delivered in a speech on "Cyber Security." What are the speaker's weaknesses?
-
Annette Creighton opened Creighton Consulting. She rented a small office and paid a part-time worker to answer the telephone and make deliveries. Her chart of accounts is as follows: Creighton's...
-
At the beginning discuss research by J. Sholl et al. on the relationship between gender and sense of direction. Recall that, in their study, the spatial orientation skills of 30 male and 30 female...
-
Discuss key differences between arbitration and mediation. Explain collective bargaining, including the role of arbitration in collective bargaining. Using examples from workplace situations, explain...
-
now what if we change variables to: Scenario Probability Market Return Aggressive Stock Defensive Stock 1 0.5 6% 2.8% 4.6% 2 0.5 15 28 10
-
Technical Analysis: Interest Rate Risk Management at Union Carbide Corporation Please provide me excel based analysis
-
With your knowledge of the differences between awards and enterprise agreements explain the impact that these have on your preparation of staffing rosters.
-
Consider a coupon bond with a time to maturity of 4 years. This bond, if things work out, pays a coupon of $50 per year at the end of each year. The bond has a face value = $1,000. a) What is the...
-
The water in a tank is pressurized by air, and the pressure is measured by a multifluid manometer as shown in Fig. 1. Determine the gage pressure of air in the tank if hi = 0.2 m, h; 0.3 m, and h;=...
-
The packaging division of a company having considered several alternative package designs for the company's new product has finally brought down their choices to two designs of which only one has to...
-
A router that has the routing table in Figure 8-11 receives an incoming IPv4 packet. The source IPv4 address in the arriving packet is 10.55.72.234. The destination IPv4 address is 10.4.6.7. The TTL...
-
Keys and passwords must be long. Yet most personal identification numbers (PINs) that you type when you use a debit card are only four or six characters long. Yet this is safe. Why?
-
a. Why is oversight important? 12a.) Policies should drive ________. a. Implementation b. Oversight c. Both A and B d. Neither A nor B b. List the three types of oversight described in the text....
-
Alma, Inc., manufactures high-pressure cleaners for large transportation companies. It uses standard costing and allocates variable and fixed manufacturing overhead based on machine-hours. For each...
-
Michael Roberts is a cost accountant and business analyst for Darby Design Company (DDC), which manufactures expensive brass doorknobs. DDC uses two direct-cost categories: direct materials and...
-
Omegas Fleet Feet, Inc., produces dance shoes for stores all over the world. While the pairs of shoes are boxed individually, they are crated and shipped in batches. The shipping department records...

Study smarter with the SolutionInn App


