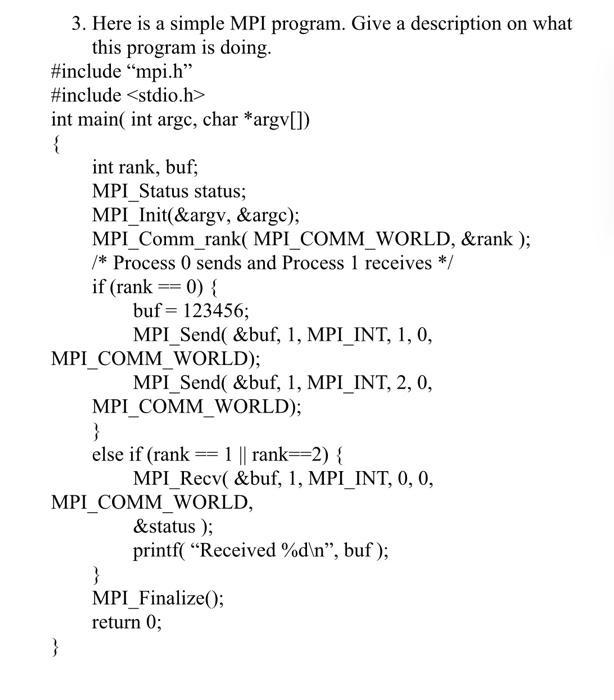
3. Here is a simple MPI program. Give a description on what this program is doing....
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
3. Here is a simple MPI program. Give a description on what this program is doing. #include "mpi.h" #include <stdio.h> int main(int argc, char *argv[]) { int rank, buf; MPI Status status; MPI_Init(&argv, &argc); MPI Comm_rank( MPI_COMM_WORLD, &rank); /* Process 0 sends and Process 1 receives */ } if (rank == 0) { MPI COMM_WORLD); buf = 123456; MPI Send( &buf, 1, MPI_INT, 1, 0, MPI Send( &buf, 1, MPI_INT, 2, 0, MPI COMM_WORLD); } else if (rank 1 || rank 2) { == } MPI COMM_WORLD, &status); printf("Received %d\n", buf); MPI Recv( &buf, 1, MPI_INT, 0, 0, MPI_Finalize(); return 0; 3. Here is a simple MPI program. Give a description on what this program is doing. #include "mpi.h" #include <stdio.h> int main(int argc, char *argv[]) { int rank, buf; MPI Status status; MPI_Init(&argv, &argc); MPI Comm_rank( MPI_COMM_WORLD, &rank); /* Process 0 sends and Process 1 receives */ } if (rank == 0) { MPI COMM_WORLD); buf = 123456; MPI Send( &buf, 1, MPI_INT, 1, 0, MPI Send( &buf, 1, MPI_INT, 2, 0, MPI COMM_WORLD); } else if (rank 1 || rank 2) { == } MPI COMM_WORLD, &status); printf("Received %d\n", buf); MPI Recv( &buf, 1, MPI_INT, 0, 0, MPI_Finalize(); return 0; 3. Here is a simple MPI program. Give a description on what this program is doing. #include "mpi.h" #include <stdio.h> int main(int argc, char *argv[]) { int rank, buf; MPI Status status; MPI_Init(&argv, &argc); MPI Comm_rank( MPI_COMM_WORLD, &rank); /* Process 0 sends and Process 1 receives */ } if (rank == 0) { MPI COMM_WORLD); buf = 123456; MPI Send( &buf, 1, MPI_INT, 1, 0, MPI Send( &buf, 1, MPI_INT, 2, 0, MPI COMM_WORLD); } else if (rank 1 || rank 2) { == } MPI COMM_WORLD, &status); printf("Received %d\n", buf); MPI Recv( &buf, 1, MPI_INT, 0, 0, MPI_Finalize(); return 0;
Expert Answer:
Answer rating: 100% (QA)
Answer This is a simple MPI Message Passing Interface program written in C MPI is a sta... View the full answer

Related Book For 

Posted Date:
Students also viewed these programming questions
-
How much accrued interest should be reported on the payee's December 31 balance sheet on a $5700, 8%, 9-month note receivable issued on June 1? $266 $38 $456 $342
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Methanol may be produced by the reaction of carbon dioxide and hydrogen. CO 2 + 3H 2 CH 3 OH + H 2 O The fresh feed to the process contains hydrogen and carbon dioxide in stoichiometric proportion,...
-
The substitution u=sin(x) is suitable to evaluate the integral cosx sin 3x O True O False
-
The financial statements for the year ended 30 November 20X3 of Springboard Ltd included a provision for doubtful debts at that date of 900. During the year ended 30 November 20X4, the company...
-
For the following exercises, determine where the given function f(x) is continuous. Where it is not continuous, state which conditions fail, and classify any discontinuities. 1 x f(x)=2x x
-
A chemical reaction was run 48 times. In each run, different values were chosen for the temperature in degrees Celsius (x1), the concentration of the primary reactant (x2), and the number of hours...
-
Ruby-Star Incorporated is considering two different vendors for one of its top-selling products which has an average weekly demand of 50 units and is valued at $75 per unit. Inbound shipments from...
-
Oakmont Company has an opportunity to manufacture and sell a new product for a four-year period. The company's discount rate is 15%. After careful study, Oakmont estimated the following costs and...
-
To get up on the roof, a person (mass 92.0 kg) places a 5.60 m aluminum ladder (mass 14.0 kg) against the house on a concrete pad with the base of the ladder 2.00 m from the house. The ladder rests...
-
Incentive to commit fraud usually will include all of the following, except a. inadequate segregation of duties. b. financial pressure. c. personal habits and lifestyle. d. feelings of resentment. e....
-
To authenticate the message sender in an asymmetric-key encryption system, which of the following keys is required to decrypt the received message? a. Senders private key b. Senders public key c....
-
Authentication is the process by which the a. system verifies that the user is entitled to enter the transaction requested. b. system verifies the identity of the user. c. user identifies him- or...
-
Data processing activities may be classified in terms of three stages or processes: input, processing, and output. An activity that is not normally associated with the input stage is a. batching. b....
-
Using an uninterruptible power supply is a a. preventive control. b. detective control. c. corrective control.
-
Which of the following is NOT an advantage of pooling sample variances? Choose the correct answer below. OA. Hypothesis tests have more power. B. The number of degrees of freedom is a little higher....
-
Use the graphs of f and g to graph h(x) = (f + g) (x). To print an enlarged copy of the graph, go to MathGraphs.com. 1. 2. y 24 8. 2. -2 -2 4 6
-
Six stations, A through F, communicate using the MACA protocol. Is it possible for two transmissions to take place simultaneously? Explain your answer.
-
On the day of a major sporting event, such as the championship game in some popular sport, many people go to the official Web site. Is this a flash crowd in the same sense as the 2000 Florida...
-
A simple telephone system consists of two end offices and a single toll office to which each end office is connected by a 1-MHz full-duplex trunk. The average telephone is used to make four calls per...
-
Which of the following is the reason preliminary estimates of materiality should be made by the auditor? a. Materiality guidelines cannot be adjusted after the audit procedures are conducted. b....
-
Which of the following is not a part of the audit risk model? a. Inherent risk. b. Control risk. c. Materiality risk. d. Detection risk.
-
Which of the following is a correct statement? a. There is an inverse relationship between risk levels and the amount of necessary audit effort. b. There is a direct relationship between risk levels...

Study smarter with the SolutionInn App


